Infrastructure Management Programs
Infrastructure management programs give businesses a structured way to monitor, maintain, and optimize servers, networks, endpoints, and cloud services so performance stays predictable, security gaps are found early, and operational disruptions are reduced before they become expensive outages.
Ainhoa M., an operations director at a regional distributor, lost a full shipping day when a virtual host datastore filled overnight, the ERP server paused, and staff reverted to paper orders because storage alerts were never routed to anyone under the company’s infrastructure management program. Emergency labor, missed shipments, and expedited vendor recovery added up to $56,500.
The following scenario reflects a redacted real-world incident pattern encountered in business IT environments. Identifying details have been changed for privacy, while the operational failure and financial impact remain representative.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure stability, security, maintenance, recovery readiness, and continuity planning across network, server, cloud, and user environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Infrastructure Management Programs because reliable business systems depend on disciplined monitoring, secure configuration, documented recovery procedures, and routine verification rather than assumptions; in Reno and Sparks business environments, this practical approach supports risk reduction, operational resilience, and fewer avoidable outages.
This article explains operational patterns, controls, and evaluation points that matter when businesses depend on stable IT. This is general technical information; specific network environments and compliance obligations change strategy. Regulated industries, legacy applications, and vendor-dependent systems often require different control choices and review cadence.
Infrastructure management programs are the repeatable operating procedures that keep business technology stable: asset inventory, monitoring, patching, configuration control, capacity tracking, service ownership, and recovery planning across servers, cloud services, firewalls, switches, and line-of-business platforms. Businesses often treat this as part of network, server, and cloud management, but the real distinction is governance: who watches what, how issues are escalated, and what gets verified before a technical condition becomes a business interruption.
- Visibility: Every supported system, vendor dependency, license, and operational owner is known.
- Maintenance discipline: Patches, firmware, certificate renewals, storage thresholds, and hardware health are handled on a schedule instead of after a disruption.
- Control evidence: Reports, logs, and test records show that monitoring, backups, access reviews, and recovery procedures are functioning.
In practice, mature programs connect infrastructure stability to cybersecurity and continuity. That is why businesses reviewing network infrastructure management should also ask how remote access, privileged administration, vendor support paths, and regulated data are handled; for medical and compliance-sensitive offices, related obligations often extend into areas covered under HIPAA security requirements and similar control expectations.
What is an infrastructure management program?
It is an operating model for the full infrastructure lifecycle, not just a collection of tools. It defines how assets are onboarded, hardened, monitored, changed, reviewed, and retired. What usually separates a stable environment from a fragile one is not the presence of software alone but named ownership, maintenance cadence, and documented dependencies between internet circuits, switches, servers, cloud services, printers, remote access systems, and the applications staff actually need to do their jobs.
Why does it matter to business operations?
A common failure point is not the dramatic outage but the quiet condition that no one owns: a certificate expires, a firewall disk fills with logs, a DHCP scope runs out, a UPS battery reports degraded runtime for months, or a storage warning is acknowledged without remediation. Infrastructure management programs reduce that exposure by turning hidden technical drift into scheduled work. In business terms, that usually means fewer work stoppages, less emergency labor, and faster recovery when a vendor platform or local device starts behaving unpredictably.
What risks does it actually reduce?
It can reduce downtime, unsupported assets, unauthorized change, weak recovery readiness, and security exposure created by stale systems or unmanaged administrative access. In practice, the issue is rarely the tool alone; it is the process around it. Guidance from the Cybersecurity and Infrastructure Security Agency (CISA) treats backup and networked storage design as resilience controls because data is only useful if it can be restored quickly and cleanly after corruption, encryption, or operator error. The same logic applies to firmware, configuration backups, and network segmentation: if they are not maintained and tested, the business may discover the gap only during an outage.
How does a mature program work in practice?
In mature environments, the program starts with asset inventory and dependency mapping, then applies monitoring thresholds, patch windows, configuration baselines, privileged access rules, and change management around those assets. Alerts are triaged by severity, documented, and either resolved immediately or pushed into scheduled remediation with clear ownership. During one routine review pattern, recurring packet-loss alerts on a warehouse switch led to a floor walk that found an unmanaged desktop switch tucked under a packing station, creating intermittent loops whenever staff rearranged equipment; the fix was not only replacing the device, but updating the network map, port security settings, and physical review checklist so the problem could not quietly return.

What evidence shows the program is being managed competently?
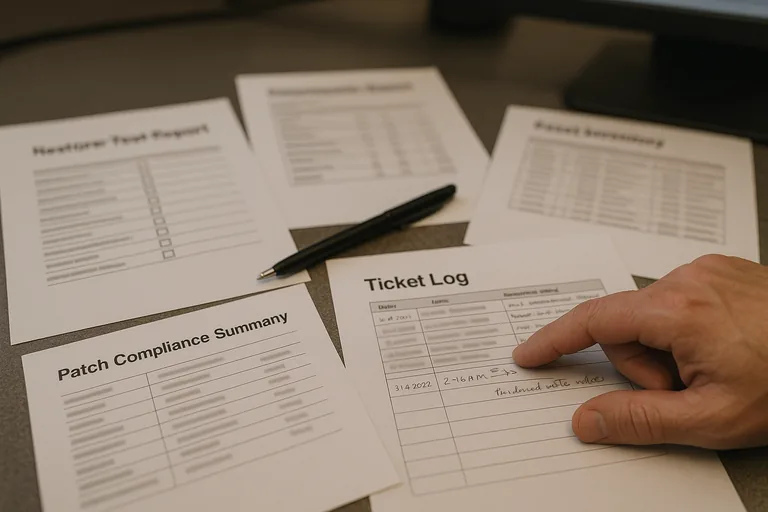
A competent provider should be able to explain the program and also produce evidence that it is operating: current asset inventories, monitoring dashboards with acknowledged alerts, patch compliance reports, change records, lifecycle data, privileged access review logs, and backup restore test results. A common failure point is a dashboard that looks healthy because thresholds are too loose or exceptions are undocumented. Real operational maturity becomes visible through review cadence and exception handling: who approved a delayed patch, when a failed job was corrected, which systems remain unsupported, and what compensating controls exist until remediation is complete.
What should a business ask before trusting a provider or internal team?
- Can they show a current asset list? If nobody can produce an accurate inventory, monitoring and patching claims are difficult to trust.
- Who owns alerts after hours? A tool may generate warnings, but response quality depends on documented escalation and acknowledgement records.
- What was the last restore or recovery test? Recovery readiness should include dates, scope, results, and lessons learned, not verbal reassurance.
- How are changes tracked? Stable environments keep records of firewall, server, cloud, and application changes so new problems can be traced quickly.
- How are privileged accounts reviewed and removed? Access tends to accumulate over time unless someone audits it on a schedule.
What should leadership do next if the environment feels stable but has not been reviewed end to end?
Low ticket volume is not proof of health. In environments that have not been reviewed recently, it is common to find unsupported network gear still in production, old service accounts with broad permissions, cloud resources billed but unmanaged, or vendor dependencies known only to one employee. This tends to break down when that employee leaves, a circuit fails, or a routine change collides with an undocumented dependency. Leadership should ask for an end-to-end review that tests assumptions, confirms ownership, and identifies where the environment is truly recoverable versus where it is merely still running.

