HIPAA
HIPAA sets the operational rules for protecting patient information, controlling access, documenting safeguards, and responding to incidents. For medical offices and any business handling protected health data, it connects privacy obligations directly to security, uptime, and accountability.
At 8:17 a.m., Alanis P. found that a former employee’s residual credentials could still open patient intake files through a misconfigured cloud fax workflow, forcing the practice into a HIPAA exposure review while staff traced access logs and counsel reviewed scope. The disruption delayed billing, consumed two days of management time, and pushed combined response costs to $58,100.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses secure infrastructure, maintain reliable systems, recover from incidents, and improve operational resilience in compliance-aware technology environments, including Reno and Sparks organizations handling sensitive data. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is relevant to HIPAA because healthcare and business-associate environments depend on practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and documented controls that continue working under daily operational pressure. Experienced IT teams approach HIPAA through layered access control, monitoring, patch governance, vendor oversight, and tested recovery procedures that reduce downtime and security exposure when something goes wrong.
This is general technical information; specific network environments and compliance obligations change strategy. HIPAA planning should be aligned with legal, compliance, and operational review of the actual systems, vendors, workflows, and data involved.
HIPAA is not a single software setting. It is a federal framework covering privacy, security, and breach notification for protected health information, or PHI, and it applies not only to covered healthcare entities but also to many business associates that create, receive, store, or transmit that data. In practice, email, file shares, copier hard drives, phones, cloud applications, and support vendors can all fall into scope, which is why structured managed IT services often become part of maintaining a workable HIPAA environment.
A common failure point is assuming HIPAA only applies to the electronic health record. Inherited environments often have PHI in scanned attachments, voicemail transcriptions, fax-to-email workflows, old laptops, and cloud backups nobody reviewed after deployment. Another point of confusion is the Security Rule’s use of the word addressable; in practice, that does not mean optional, it means the business must assess the safeguard, implement it appropriately, and document why an equivalent measure is reasonable if a different approach is used. Offices that also process payment cards should understand where healthcare obligations end and where related controls discussed in PCI DSS guidance begin, especially when the same workstation, vendor, or network touches both billing and patient workflows. Mature IT operations oversight separates those duties, documents ownership, and reduces the chance that one weak process creates two compliance problems.
- Administrative safeguards: Risk analysis, workforce procedures, vendor oversight, policies, and response planning.
- Physical safeguards: Device control, workstation use rules, secure disposal, and access to areas where PHI is stored or viewed.
- Technical safeguards: Unique user IDs, access controls, audit logs, encryption where appropriate, and integrity protections for electronic PHI.
What does HIPAA actually require from a business?
HIPAA requires organizations handling PHI to protect confidentiality, integrity, and availability, limit unnecessary disclosures, train the workforce, manage vendors that touch PHI, and follow breach response rules when exposure occurs. The HHS HIPAA Security Rule matters because it turns compliance into three safeguard groups, administrative, physical, and technical, so leadership can judge whether controls exist as operating procedures rather than as policy language alone.
Why does HIPAA matter beyond avoiding fines?
HIPAA matters because patient-data failures usually become operating failures before they become enforcement problems. When access is loose or logging is incomplete, staff lose time reconstructing who opened records, claims processing slows, supervisors improvise manual workarounds, and leadership makes decisions without reliable incident facts. What usually separates a stable environment from a fragile one is not the tool alone; it is whether identity control, documentation, and escalation are maintained well enough that a suspected exposure can be scoped quickly and normal work can continue.
What risks does HIPAA reduce in real operations?
In real business environments, HIPAA-oriented controls reduce several common exposures: former staff retaining access, shared accounts hiding accountability, unencrypted laptops carrying cached patient files, unsupported systems missing security updates, and vendors receiving PHI without a clear responsibility model. In practice, the issue is rarely one dramatic event; it is the slow accumulation of shortcuts that make unauthorized disclosure, altered records, and extended downtime more likely when a device is lost, an account is compromised, or a staff member sends information through the wrong channel.
How does HIPAA work in daily IT operations?
Daily HIPAA work looks like identity lifecycle control, endpoint hardening, audit logging, patch discipline, secure messaging decisions, and routine review of who can access which systems. Guidance in NIST SP 800-63B is useful here because authentication is not just a password rule; it is a lifecycle problem involving enrollment, multifactor enforcement, resets, privileged access, and prompt removal when job roles change. During a routine access review, sign-in logs may show a disabled employee account still authenticating to a scanner-to-email workflow because the device was using saved credentials no one documented after an office move. The signal looks minor, but the underlying issue is larger: offboarding failed across connected systems, audit trails are now less reliable, and a competent team should update the workflow, remove the stale secret, confirm enforcement on all related accounts, and record the exception handling so the gap does not quietly return.
How can a business tell whether its HIPAA controls are real?
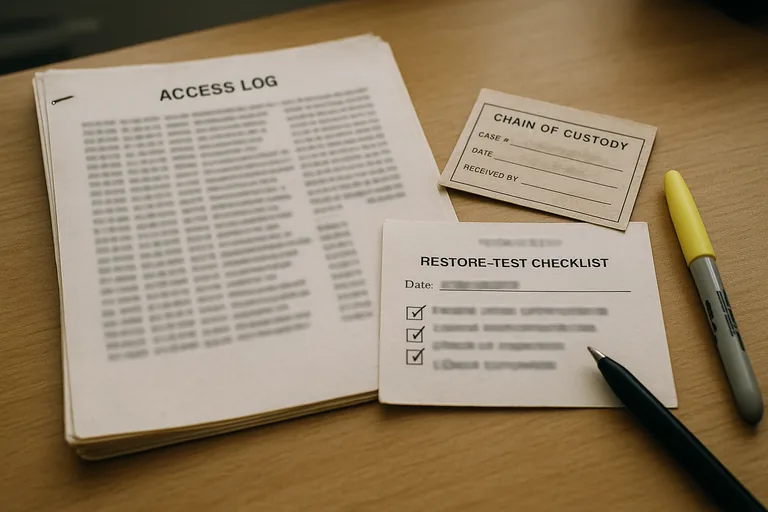
Ask for evidence, not assurances. A mature environment should produce a current risk analysis, an asset inventory showing where PHI can exist, access review logs, patch compliance reports, endpoint protection status, documented vendor records, and incident response procedures that identify who investigates, who authorizes notifications, and how evidence is preserved. A common failure point is finding policies in a binder while no one can show the last restore test, the last access certification, or the last review of terminated-user removals. If the control is real, there should be records with dates, owners, exceptions, and follow-up actions.
When does weak HIPAA implementation become dangerous?
What should leadership do next about HIPAA?
The next step is a gap-based review, not a rushed purchase. Leadership should confirm where PHI lives, which vendors can touch it, how users are provisioned and removed, whether logs and alerts are actually reviewed, and whether recovery and breach procedures have been tested with dated evidence. A competent provider should be able to explain what is already in place, what is only partial, what exceptions remain open, and how remediation will be prioritized against business disruption, not just against a checklist.

