Healthcare
Healthcare organizations often need local guidance, reliable vendor coordination, and practical IT support that fits clinical workflows, protects patient data, and keeps front desks, billing teams, and care delivery moving during daily operational pressure.
At 8:12 a.m., Alejandro F. learned that a former billing contractor’s account was still active in the practice management portal; overnight remittance changes froze claims reconciliation, delayed patient check-in, and emergency response, rework, and cash-flow disruption totaled $60,100.
The operational stakes are higher because a delay at one point in the chain can ripple into missed appointments, delayed claims, charting workarounds, and privacy exposure. The HHS HIPAA Security Rule matters here because its administrative, physical, and technical safeguards are intended to preserve the confidentiality, integrity, and availability of protected health information, not just create paperwork. Healthcare also shares governance pressure seen in regulated financial services environments, where leaders need proof that controls are actually enforced.
The following incident pattern is drawn from real managed IT environments. Identifying details have been changed to protect privacy, while the business consequences remain representative.
Scott Morris is a managed IT and cybersecurity professional who helps businesses secure, maintain, and recover critical systems when downtime, data exposure, or weak operational controls threaten daily operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Healthcare because clinics, specialty practices, and administrative healthcare environments depend on stable infrastructure, controlled access, recovery readiness, compliance-aware system management, and practical risk reduction that supports business continuity and operational resilience in Reno and Sparks business environments.
This is general technical information; specific network environments and compliance obligations change strategy. Healthcare organizations should review legal, clinical, privacy, and vendor-specific requirements before changing systems that affect patient care or protected data.
Healthcare operations depend on more than an electronic health record. Reception, exam rooms, billing, labs, imaging, phone systems, printers, mobile devices, cloud identities, and vendor portals all have to work together, which is why disciplined managed IT services in this sector are built around workflow continuity as much as technical uptime.
- Clinical continuity: Staff need documented downtime procedures when an application, scanner, or internet circuit fails during patient care or intake.
- Identity control: Every workforce change, vendor account, and privileged login needs ownership, approval, and timely removal.
- Vendor coordination: EHR, imaging, lab, phone, copier, and network providers must be managed as one operating environment, not separate islands.
What does healthcare IT actually include?
Healthcare IT includes the EHR or practice management platform, imaging workstations, e-prescribing, patient communication tools, payment workflows, endpoint devices, wireless networks, scanners, phones, cloud email, and the identity system that decides who can access each part. A common failure point is assuming the software vendor owns all risk; in practice, local devices, permissions, patching, network stability, and staff offboarding usually remain the healthcare organization’s responsibility.
Why does healthcare demand a different level of operational discipline?
Healthcare tolerates very little ambiguity because security, uptime, and workflow speed are linked. A password reset delay can slow patient intake, a printer failure can interrupt consent and lab processing, and a poorly timed update can derail a clinic session. What usually separates a stable environment from a fragile one is documented change control, vendor coordination, and the ability to shift into a downtime process without losing track of patient information or billing activity.
Which healthcare risks are most often missed until operations are disrupted?
A common failure point is identity lifecycle management: shared front-desk accounts, former staff still enabled in a portal, vendor support logins excluded from multifactor authentication, and tablets or specialty devices left outside normal policy. Guidance in NIST SP 800-63B matters because strong authentication only works when account provisioning, exceptions, and removal are handled consistently across the full lifecycle. In environments that have not been reviewed recently, these gaps often stay invisible until claims stop posting, messages are misdirected, or no one can explain who accessed protected data.
How does competent healthcare IT management work in practice?
Competent healthcare IT management starts with a current asset inventory, system criticality ranking, role-based access, patch windows that respect clinic schedules, endpoint monitoring, log review, and written escalation paths between the practice, software vendor, and IT provider; this is where structured healthcare IT operations usually outperform ad hoc support. During a routine access review, repeated overnight login failures from a radiology workstation revealed a vendor support account that had been left outside conditional access because the application was considered too sensitive to change. The workstation was functioning, but the exception created an unmonitored path into scheduling, which is why mature environments document each exception, assign an owner, and review it on a fixed cadence.

How can a healthcare organization verify that protections are really working?
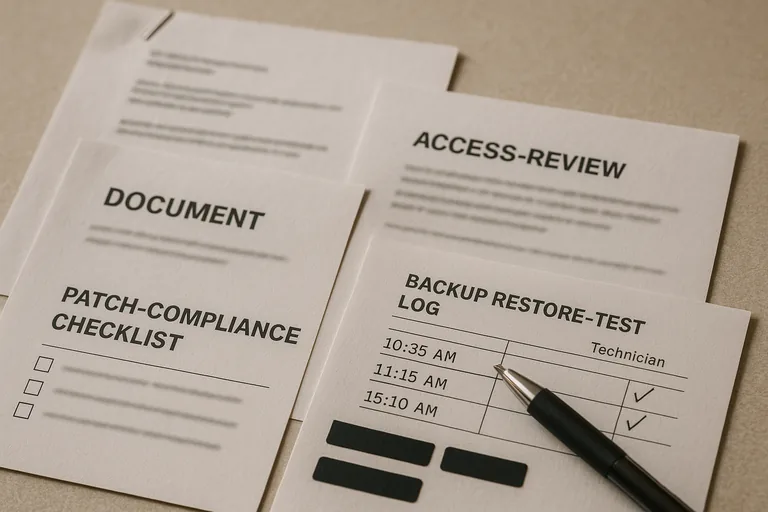
A mature environment produces visible evidence, not just verbal assurance: access review reports showing who approved PHI access, patch compliance reports for servers and workstations, endpoint protection health dashboards, change records for vendor updates, backup restore test results, and incident timelines that show who responded and how quickly. In practice, this often breaks down when tools are installed without response workflows; alerts may fire, but nobody can show escalation records, policy exceptions, or proof that failed systems were restored cleanly during testing. If leadership cannot see current evidence, the control may exist only on paper.
What should leadership evaluate before trusting a healthcare IT provider or internal team?
- Access governance: Ask how new users are approved, how former staff are removed, and how vendor accounts are tracked and reviewed.
- Operational reporting: Ask for sample patch reports, endpoint health summaries, access review records, and documented exception lists.
- Recovery proof: Ask when the last restore test was performed, what systems were included, and whether downtime procedures were practiced with staff.
- Ownership clarity: Ask who coordinates the EHR vendor, internet provider, phone system, imaging devices, and line-of-business software during an incident.
When should a healthcare organization escalate and get outside review?
An outside review is usually warranted when leadership cannot get clear answers about access ownership, unsupported devices remain in daily use, repeated workflow problems are treated as isolated tickets, or the organization has not seen a recent risk review tied to actual systems. This tends to break down when the environment has grown through mergers, new providers, remote staff, or specialty applications without one party maintaining the full map. Bringing in an experienced advisor at that point can clarify hidden dependencies before a billing interruption, privacy event, or extended outage forces a more expensive response.

