Growing Companies
Growing companies need more than new software and extra licenses. They need dependable guidance, scalable systems, and clear operational controls so expansion does not create downtime, security gaps, or expensive confusion across people, locations, and workflows.
When Alice J.‘s 54-person service company added two new offices in one quarter, user access was still tracked in spreadsheets and a departed manager kept Microsoft 365 admin rights. That stale account was abused to set mailbox forwarding and change SharePoint permissions, delaying invoicing for three days and creating $62,300 in recovery costs and missed cash flow.
The following situation represents a realistic incident pattern derived from real business IT environments. Identifying details have been changed to preserve confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage, secure, maintain, and recover the technology environments they rely on for daily operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. His work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience, which is directly relevant when growing companies need stable onboarding, controlled access, documented support processes, and dependable recovery planning across expanding systems, staff, and locations, including Reno and Sparks business environments.
Growth often exposes gaps that were tolerable at ten users but risky at fifty, especially when ownership and documentation have not kept pace. This is general technical information; specific network environments and compliance obligations change strategy.
Growing companies are businesses whose operating model is changing faster than their internal controls. Headcount rises, vendors multiply, cloud apps appear, and one office becomes two, but ownership of accounts, devices, permissions, and documentation often stays informal. Many firms still behave like small businesses long after the complexity has outgrown memory-based IT management.
The main issue is not growth itself; it is unmanaged expansion. A common failure point is that each department adopts tools and access shortcuts without a shared process for approval, deployment, support, and offboarding. That is where disciplined managed IT services become operationally important: they create repeatable onboarding, patching, security monitoring, vendor coordination, and escalation ownership so growth does not turn into hidden fragility.
What does IT planning for growing companies actually mean?
IT planning for a growing company means designing technology so the business can add people, locations, software, and outside vendors without losing control of access, support, data flow, or recovery capability. It is less about buying more tools and more about deciding who approves changes, how new users are provisioned, where critical data lives, which systems are business-critical, and what happens when a laptop fails, an employee leaves, or a key application stops syncing.
Why does growth create more operational risk than most leaders expect?
Growth increases risk because complexity compounds quietly. Each new hire creates accounts, each new application creates another identity store, and each new location or remote workflow creates another support boundary. A common failure point is that companies outgrow the informal habits common in smaller business environments: permissions are granted by email, shared mailboxes become operational dependencies, and nobody has a current map of which systems control quoting, payroll, or customer records. The result is not abstract cyber risk; it is missed invoices, slower support, approval bottlenecks, and higher downtime when something breaks.
Which risks should a growing company reduce first?
How should growth be managed in practice across users, devices, and software?
In mature environments, growth is handled through a defined workflow: a manager submits a request, access is granted from a role template, the device is enrolled into management, baseline security policies and endpoint protection are applied, and the application owner is recorded before the user goes live. Offboarding follows the reverse order so licenses, tokens, mobile devices, and shared mailbox permissions are removed without relying on memory. During a routine sign-in review, one common diagnostic pattern is a repeated successful login from a dormant shared account; investigation often shows the account survived a reorganization because no one owned the application tied to it. The lesson is that reliable growth depends on lifecycle process, not just tools.
How can a business tell whether its IT environment is being managed competently?
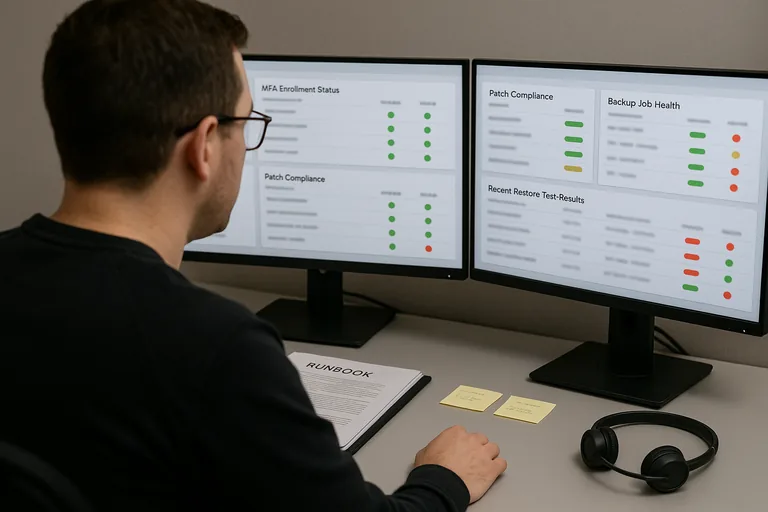
A business can test competence by asking for evidence, not promises. A mature managed IT program should be able to show a current asset inventory, patch compliance reports, MFA enrollment status, access review logs, documented onboarding and offboarding procedures, alert escalation records, and restore test results for critical systems. In practice, this often breaks down when a provider says monitoring is active but cannot show who reviews alerts, or says patching is automated while exception reports reveal laptops missing updates for weeks. Those records matter because they prove controls are operating, exceptions are known, and leadership is not relying on assumptions.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when controls exist on paper but not in enforced process. Common examples include department managers buying SaaS tools without security review, old administrators retaining rights after promotions, line-of-business applications installed on one unmonitored workstation, or security software deployed without any response workflow when it triggers. What usually separates a stable environment from a fragile one is ownership: someone must be responsible for the application, the data, the permissions, the alerts, and the recovery procedure. When ownership is unclear, growth hides the problem until a merger, audit, turnover event, or outage exposes it.
What should leadership do before growth exposes a preventable failure?
Leadership should start with a short operational review of users, devices, applications, vendors, and business-critical processes, then compare that inventory against documented ownership and actual support responsibility. The useful questions are practical: Which systems stop revenue if they fail, who can approve access, where are the exceptions, how quickly can a terminated employee be fully removed, and what evidence shows controls were reviewed recently? If those answers are incomplete, the next step is a remediation plan with dates, accountable owners, and follow-up verification rather than another round of informal workarounds.

