Governance, Policy & Audit Preparation
Governance, policy, and audit preparation turn security expectations into accountable business practice. When ownership, controls, and evidence are clear, leadership can reduce avoidable risk, answer audits confidently, and avoid expensive disruption during incidents, renewals, or regulatory reviews.
Two weeks before a customer security review, Adria L. discovered a departed supervisor still had active VPN access because offboarding was handled by email instead of policy. The account had been used to pull internal pricing files, the review was paused, and emergency forensic work, legal review, and remediation costs reached $52,900.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage secure infrastructure, stable operations, recovery readiness, and compliance-aware technology environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is directly relevant to governance, policy, and audit preparation because experienced IT teams reduce operational risk, downtime, and security exposure by tying policies to accountable owners, repeatable workflows, documented evidence, and regular review instead of leaving controls as static documents. His work supporting Reno and Sparks business environments is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience.
This article explains operational patterns, common controls, and audit-readiness practices that decision-makers can use to assess risk. This is general technical information; specific network environments and compliance obligations change strategy.
Governance, policy, and audit preparation are often mistaken for paperwork, but their real purpose is operational control. Governance decides who owns risk decisions, policy defines expected behavior, and audit preparation proves that those expectations are enforced across systems, staff, and vendors. In a mature environment, this sits inside broader compliance and risk management so leadership can see which obligations apply, who owns them, and where evidence is maintained.
- Ownership: Every control needs a named owner, review cadence, and approval path when exceptions are requested.
- Evidence: A control is not mature because it exists in a policy file; it becomes credible when logs, reports, reviews, and test records show it is active.
- Exceptions: Real businesses make exceptions, but competent environments document them, assign an expiry date, and review whether the risk is still acceptable.
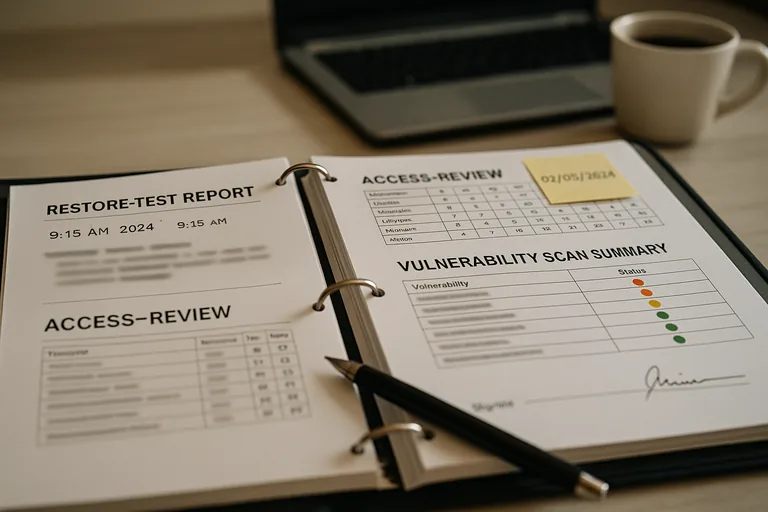
Audit readiness is not a binder assembled the week before a review. It is the ongoing discipline of maintaining asset inventories, access reviews, change records, security logs, training records, and recovery documentation so questions can be answered without scrambling. Businesses that need more formal regulatory compliance support, and medical practices working through HIPAA security requirements, usually discover that the difficult part is not writing policies; it is proving those policies match actual system behavior.
What does governance, policy, and audit preparation actually mean in day-to-day operations?
In practice, governance answers who can make a risk decision, policy answers what the organization requires, and audit preparation answers how that requirement is demonstrated. A common failure point is treating all three as the same thing. When that happens, a business may have a policy stating laptops must be encrypted, but no process for checking enrollment, no owner for remediation, and no evidence showing which devices are compliant. In mature environments, these functions connect: leadership approves expectations, IT or operations enforces them through tools and workflows, and the business keeps records that show the control is real.
Why does it matter beyond passing an audit?
Weak governance usually shows up first as confusion, not as a formal audit finding. Changes are made without approval, vendors gain access without review, employees keep permissions they no longer need, and exceptions stay in place long after the original reason has disappeared. What usually separates a stable environment from a fragile one is accountability. When ownership is clear, patching happens on schedule, offboarding is completed, critical systems are documented, and incidents move faster because people know who can approve containment, shutdowns, or emergency access. That reduces downtime, security exposure, and the cost of last-minute cleanup.
Which risks does it prevent or reduce?
Good governance reduces several quiet but expensive risks: stale access, unsupported systems, undocumented software, missing encryption, weak vendor oversight, and audit failures caused by absent evidence. These are not abstract issues. They affect insurance questionnaires, customer security reviews, contract renewals, and breach response. For Nevada businesses, obligations under Nevada Revised Statutes NRS 603A matter because organizations handling personal information are expected to maintain reasonable security measures; governance turns that legal expectation into assigned controls, review dates, and evidence rather than assumptions left to individual staff habits.
How does competent audit preparation work in practice?
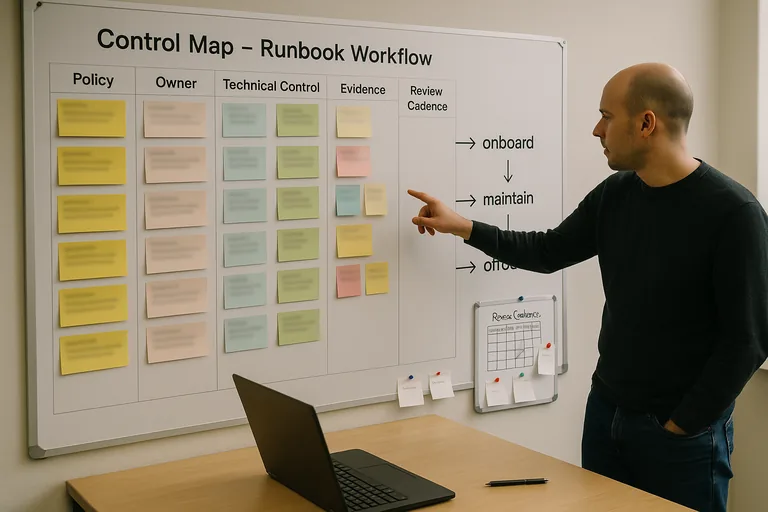
Competent audit preparation usually starts with a control map. That map ties each requirement to a policy statement, a system owner, the technical control enforcing it, the evidence proving it, the review cadence, and any approved exceptions. One of the first things experienced IT teams check is whether evidence can be reproduced on demand: access review logs, patch compliance reports, device encryption status, change records, security awareness completion records, incident timelines, and backup test results. During a routine pre-audit review, an endpoint management report showed several replacement laptops with no encryption status even though policy required it. Investigation found they had been issued quickly during a hardware shortage and never re-enrolled in the standard management workflow. The lesson was not that the policy was wrong; it was that asset reconciliation and enrollment verification were missing, so the control existed on paper but not on every device.
How can a business tell whether policies are actually being enforced?
A competent provider should be able to explain where evidence lives, who reviews it, and what happens when a control fails. In practice, real enforcement leaves artifacts: quarterly access review reports signed off by management, exception logs with expiry dates, configuration baselines, vulnerability scan summaries, alert escalation records, and documented corrective actions. Guidance in NIST SP 800-63B exists because authentication and identity controls break down when account lifecycle management is inconsistent; for a business owner, that translates into a simple question: can the team show how accounts are approved, reviewed, and removed, or is the process still happening through informal emails and memory?
When does weak implementation become dangerous?
What should leadership do next if gaps are already visible?
Start by identifying the few controls that carry the most business weight: identity lifecycle, privileged access, asset inventory, change management, vendor access, logging, recovery readiness, and exception handling. Then ask for evidence, not assurances. Leadership should be able to see the current policy owner, the last review date, the technical control enforcing the policy, the most recent report or log proving it, and any open exceptions with target dates. If that material cannot be produced without a scramble, the environment may still function day to day, but it is not truly audit-ready. That is the point where an experienced advisor can help translate obligations into an operating model the business can actually maintain.

