Defense Contractors
Defense contractors need more than general IT support; they need operational guidance, compliance-aware security, and local technical leadership that can help protect controlled data, maintain contract readiness, and connect daily IT decisions to mission and revenue.
On a Thursday before a bid submission, Alexandria Q. discovered that her engineering team’s shared folder permissions had drifted for months, exposing export-sensitive drawings to a subcontractor mailbox sync account. The disclosure review halted proposal work for nine days, forced forensic and legal review, and cost $61,200 before operations returned to normal.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses secure infrastructure, stabilize day-to-day systems, document recovery procedures, and reduce operational risk when uptime, controlled data handling, and audit readiness matter. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to defense contractors because these environments depend on disciplined access control, recovery readiness, incident response structure, and evidence that security practices are actually operating rather than merely promised. His work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience for business technology environments, including Reno and Sparks organizations that need stable, secure, compliance-aware systems.
Requirements for defense contractors vary by contract terms, data types, and subcontractor relationships. This is general technical information; specific network environments and compliance obligations change strategy. Legal, contractual, and assessment questions should be reviewed with the appropriate compliance and counsel resources.
For IT purposes, defense contractors are not defined by company size so much as by the information they touch, the clauses they inherit, and the operational dependency others have on their systems. Many firms outgrow ordinary managed IT services when drawings, purchasing data, production records, supplier communications, and engineering collaboration begin carrying federal handling expectations.
A common failure point is assuming all business data needs the same level of protection. In practice, defense contractors usually need to identify where Federal Contract Information and Controlled Unclassified Information enter the business, who can access them, how they move through email, file shares, ERP systems, CAD workstations, and vendor portals, and how a managed IT operations program actually enforces those boundaries. Without that mapping, companies often buy tools before they know what must be protected, monitored, or restricted.
- Contract flow-downs: Security expectations often arrive through customer and subcontract requirements, not only through internal policy.
- Operational evidence: The business may need to show logs, review records, configuration baselines, and test results rather than relying on verbal assurances.
- Supplier exposure: A small access exception for a machine vendor, CAD consultant, or project partner can create a large disclosure problem if ownership and review are weak.
What makes IT for defense contractors different from ordinary business support?

Ordinary office IT focuses on productivity and uptime. Defense contractor IT carries an added burden: sensitive contract information must be protected in a way that can be demonstrated. Guidance such as NIST SP 800-171 exists because contractors handling Controlled Unclassified Information need consistent safeguards around access control, logging, configuration management, incident handling, and recovery. In business terms, that means a missed permission change or unmanaged engineering laptop is not just a technical oversight; it can become a contract performance issue, a disclosure event, or a delay in future work.
Why do defense contractors get into trouble even when they already have security tools?
A common failure point is tool ownership. Companies may buy endpoint protection, multifactor authentication, email filtering, and cloud backup, yet still leave access reviews, exception handling, and subcontractor onboarding informal. In environments that have not been reviewed recently, shared folders keep legacy permissions, guest accounts remain active after projects end, and administrators create temporary workarounds that quietly become permanent. The risk is rarely the tool alone; it is the process around it. That is why defense contractors often need routine managed IT oversight with documented ownership, escalation paths, and review cadence rather than occasional check-ins.
How should a defense contractor environment work in practice?
In mature environments, the work starts with asset inventory, data mapping, role-based access, hardened endpoints, and segmented networks so engineering, finance, and production systems are not all equally reachable after one compromise. Guidance from NIST SP 800-207 Zero Trust Architecture matters because defense contractors cannot assume that being on the company network makes a user or device trustworthy; each access request should be authenticated and limited by role, device state, and data sensitivity. During a routine review pattern, repeated sign-in prompts from a CAD workstation led investigators to a service account with interactive access, stale privileges, and no current owner. The symptom looked minor, but the lesson was not: identity exceptions must be documented, limited, and reviewed before they become a path into controlled data.
What evidence shows the controls are actually working?
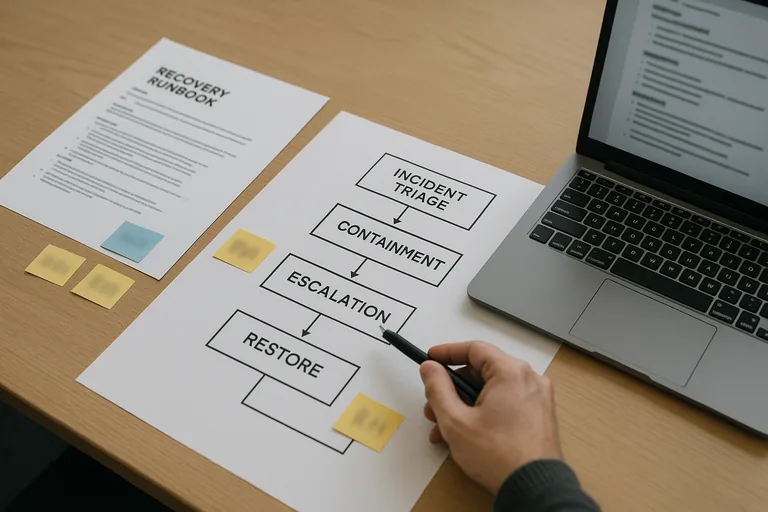
A competent environment produces evidence, not just assurances: current asset inventory records, patch compliance reports, access review logs for privileged and project-based accounts, vulnerability scan summaries, backup restore test records, and incident timelines showing who responded and when. Guidance from CISA incident response resources is relevant because response quality depends on log availability, evidence preservation, and clear containment steps. In practice, this often breaks down when alerts exist but nobody can show the escalation record, or when backups report success but no recent file-level and system-level restore test proves recovery speed.
How can leadership evaluate whether an IT provider understands defense contractor risk?
- Ask about data boundaries: A competent provider should be able to explain where contract data lives, how access is limited, and how subcontractor sharing is controlled.
- Ask for evidence: Look for patch reports, access review records, backup restore test results, exception logs, and configuration baselines rather than verbal reassurance.
- Ask about identity lifecycle: They should describe how accounts are approved, elevated, reviewed, and removed when projects end or staff change roles.
- Ask about incident handling: They should have a defined triage and escalation workflow showing who investigates suspicious activity, how scope is determined, and how decisions are documented.
When does weak implementation become dangerous for a defense contractor?
This tends to break down when compliance language is copied into policy documents while the live environment keeps broad file-share permissions, unmanaged test machines, or vendor remote access that bypasses normal controls. A common failure point is assuming the shop floor, lab, or engineering enclave is isolated when it still trusts the same directory, same admin group, and same flat network as the rest of the office. Weak implementation becomes dangerous the moment a phishing compromise, personnel change, or subcontractor dispute forces the business to prove who had access to what and when. If that proof is missing, the problem expands from technical cleanup into reporting pressure, customer confidence damage, and delayed contract work.
What should happen next if your environment has grown informally?
The practical next step is a documented baseline review: inventory systems touching contract work, map where controlled data enters and leaves, identify privileged accounts, confirm logging coverage, and test a small set of recovery and access-control assumptions before treating the environment as ready. What usually separates a stable environment from a fragile one is not a larger tool stack; it is ownership, evidence, and correction of exceptions. Leadership should expect a prioritized remediation list, named control owners, and a review cadence that keeps the environment from drifting back into the same weaknesses.

