Cyber Insurance Readiness
Cyber insurance readiness means being able to prove that security controls, recovery capability, and incident response processes are not merely promised but operating, documented, and reviewable before an insurer prices coverage or evaluates a claim.
After a controller at Aleix Z.‘s distribution firm entered credentials into a spoofed Microsoft 365 login page, attackers accessed shared mailboxes and altered payment instructions. The insurer challenged the claim because multifactor authentication was not enforced for every user and no access review records existed, leaving the business with $59,750 in unrecoverable fraud, legal review, and emergency response costs.
The following incident pattern is drawn from real managed IT environments. Identifying details have been changed to protect privacy, while the business consequences remain representative.
Scott Morris is a managed IT and cybersecurity professional who helps businesses secure identity systems, maintain reliable infrastructure, recover from disruptions, and build stronger continuity and documentation practices. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Cyber Insurance Readiness because insurers increasingly examine whether access controls, backup integrity, incident response procedures, and operational records are actually maintained in real business environments, including Reno and Sparks organizations that need stable, secure, compliance-aware technology operations.
This article explains common technical readiness issues and how businesses can evaluate them before an application, renewal, or claim. This is general technical information; specific network environments and compliance obligations change strategy.
Readiness also affects the claim phase. A common failure point is that an application says endpoint protection, backups, or MFA are in place, but during investigation the controls are found to be partial, undocumented, or not enforced on every system. What usually separates a stable environment from a fragile one is not the tool alone; it is the ownership, review cadence, and evidence produced by ongoing infrastructure management.
What is cyber insurance readiness?
Cyber insurance readiness is the operational state in which a business can show that its key cybersecurity and continuity controls are implemented, assigned to owners, and supported by records. In practice, it is less about filling out a form and more about proving that identity protection, patching, logging, endpoint security, backups, and response procedures are working consistently enough that an insurer can underwrite the risk with fewer unknowns.
Why does it matter before renewal or a claim?
It matters because policy applications and renewal questionnaires are increasingly detailed, and a mismatch between stated controls and actual controls can create coverage disputes at the worst possible moment. A common failure point is that leadership believes MFA exists because some staff use it, while administrators, legacy mail protocols, or remote access exceptions were never brought into enforcement. When an incident happens, that gap becomes a business problem: more downtime, more investigation cost, more pressure from legal and finance teams, and less certainty about whether the insurer will treat the loss as a covered event.
What controls do insurers usually expect to see?
- Identity controls: Multifactor authentication, disabled legacy authentication, role-based access, and a reliable offboarding process reduce the chance that one compromised password becomes an account takeover or funds transfer event.
- System maintenance: Patch management, vulnerability remediation, supported software versions, and basic hardening reduce exposure to known exploits that are often involved in ransomware and data theft.
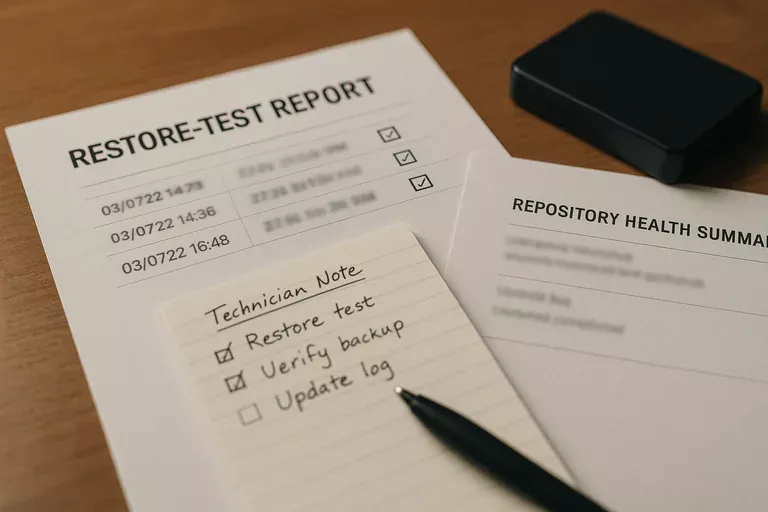
- Recovery controls: Backups need segregation, retention, and documented restore testing so the business can recover data without discovering corruption or missing systems during an outage.
- Detection and response: Endpoint security, centralized logging, and an incident response process matter because insurers want to know whether suspicious activity will be noticed, investigated, and contained quickly.
How does cyber insurance readiness work in practice?
In mature environments, readiness starts with an accurate asset inventory, a review of privileged accounts, confirmation of MFA enforcement, patch compliance checking, backup validation, and collection of the records that support those claims. Guidance in NIST SP 800-63B matters here because it treats authentication as a lifecycle discipline rather than a one-time setup; businesses reduce risk when they can show who has access, how stronger authentication is enforced, and how disabled users are removed promptly. During one routine readiness review, a sign-in report showed successful logins from an approved user account but from an unexpected foreign IP and an outdated mail protocol. The underlying issue was not the password alone; conditional access rules had never been applied to a small group of shared and service-linked accounts, which is exactly the type of implementation gap an experienced IT team is expected to find and close before a claim tests it.

How can a business tell whether its provider is truly prepared?
A competent provider should be able to produce evidence, not just reassurance. That means current asset inventory records, patch compliance reports, endpoint protection status summaries, access review logs, backup restore test results, incident response playbooks, and documented escalation workflows showing who responds to alerts and how exceptions are approved. In practice, the issue is rarely the tool alone; it is the process around it. If a provider cannot show when privileged access was last reviewed, cannot explain how failed backup jobs are escalated, or cannot demonstrate that policy exceptions are tracked and revisited, the environment may be more fragile than the insurance application suggests.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when controls exist on paper but are not validated under real conditions. This tends to break down when backups run but no one performs restore tests, when endpoint tools are installed but alert triage ownership is unclear, or when MFA is enabled for staff but not enforced for every administrative, VPN, or cloud application account. Guidance from CISA is useful here because protected and recoverable backups only reduce ransomware exposure if they are isolated enough to survive the attack and tested well enough to restore operations on schedule. Without that verification, businesses often discover during a crisis that they were insured against loss in theory while still operationally unprepared in practice.
What should happen next before renewal or application?
The next step is a gap review that compares insurer questions to actual technical controls, assigned ownership, and available evidence. Leadership should identify where answers depend on assumptions, remediate the highest-risk weaknesses first, and require proof before anything is marked complete. A useful review usually includes access enforcement checks, backup restore testing, patch and vulnerability status, incident response documentation, and a short record of approved exceptions so the application reflects the real environment rather than optimistic language.

