Compliance & Risk Management in Sparks, Nevada
Compliance and risk management in Sparks, Nevada means identifying where business systems, data handling, access, and documentation can fail, then putting evidence-backed controls in place so leadership can reduce exposure, meet obligations, and stay prepared for audits or incidents.
During a renewal review in Sparks, Alonso W. learned a former vendor still had remote access to the accounting server and years of payroll files were syncing to an unmanaged laptop. The access gap triggered legal review, emergency containment, and delayed month-end processing, leaving the business with $64,800 in direct response and interruption costs.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage stable infrastructure, secure user access, document operational controls, and recover cleanly when systems or processes break down. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to compliance and risk management in Sparks, Nevada because weak access control, undocumented exceptions, poor recovery readiness, and inconsistent monitoring often create both security exposure and audit problems; experienced IT teams reduce that risk by aligning policy, system administration, verification, and business continuity into one accountable operating model.
This article explains common control and verification practices used to reduce legal, security, and downtime exposure. This is general technical information; specific network environments and compliance obligations change strategy.
For many organizations, compliance and risk management is not a binder on a shelf. It is the ongoing discipline of identifying where customer data, financial systems, cloud apps, remote access, and vendor connections can fail, then assigning controls and ownership before the weakness turns into downtime, data exposure, or a failed contract review.
In Nevada, that work has direct legal meaning. Nevada Revised Statutes NRS 603A requires reasonable security measures for personal information and creates breach notification obligations when protected data is exposed. In practice, businesses in Sparks usually need someone owning asset inventory, access review, patching, vendor oversight, and incident documentation on an ongoing basis, which is why mature organizations often tie these functions to managed IT services in Sparks instead of scrambling only when an insurer, auditor, or customer sends a questionnaire.
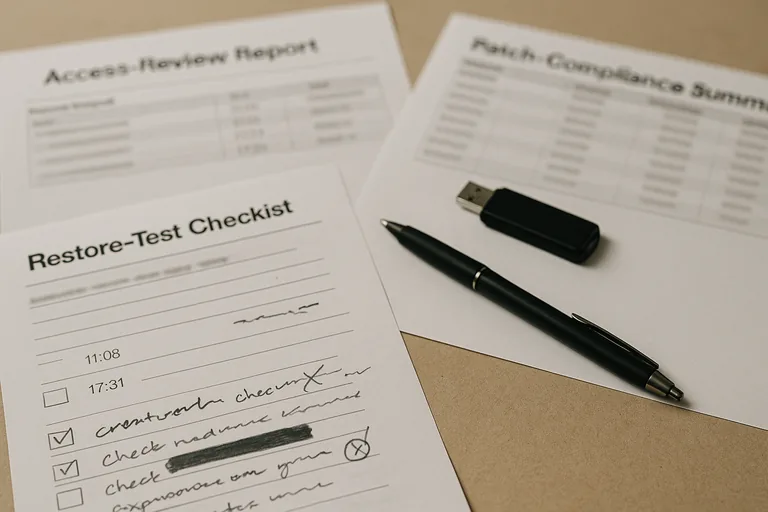
What usually separates a stable environment from a fragile one is evidence. A policy statement does not prove risk is being managed; patch compliance reports, access review logs, exception records, and documented response procedures do. A mature risk management process shows leadership what is protected, what remains open, who owns remediation, and how quickly the business could recover if a control fails.
What does compliance & risk management actually cover in a Sparks business?
It covers the operational controls that protect sensitive information and keep the business accountable when something goes wrong. That usually includes how accounts are created and removed, which systems store regulated or confidential data, how security updates are applied, how vendors connect, what logs are retained, who approves exceptions, and how incidents are documented. In mature environments, compliance is not treated as separate from IT operations because the same weak points that cause audit findings also cause outages, data leakage, and messy recovery efforts.
Why does it matter beyond passing an audit?
An audit is only one pressure point. The larger issue is that poor control discipline often shows up first as operational drag: delayed approvals, missing documentation during insurance renewals, uncertainty about what data was exposed, or hours lost proving who had access to what. What usually separates a stable environment from a fragile one is that leadership can answer those questions quickly with records, instead of reconstructing events during legal review, contract negotiations, or an active incident.
Which operational risks does it reduce most often?
- Identity sprawl: Former employees, contractors, and vendors keep access longer than expected, creating exposure and weak audit trails.
- Unsupported systems: Legacy servers and line-of-business applications remain in use because nobody owns replacement planning, leaving known vulnerabilities and compliance gaps.
- Silent monitoring failures: Security tools generate alerts, but no clear after-hours escalation or review cadence exists, so suspicious activity sits unanswered.
- Documentation breakdowns: Policies may exist, yet system owners, exception approvals, and recovery steps are missing when leadership needs proof.
How does competent implementation work in practice?
Competent implementation starts with inventory and ownership, not software purchasing. Experienced teams identify systems, users, data types, third-party connections, and business processes, then map controls to each area: access rules, patching standards, logging requirements, vendor review, backup scope, and incident escalation. Guidance from NIST SP 800-63B matters here because identity controls only reduce risk when enrollment, multifactor enforcement, password reset, and account retirement are managed through the full account lifecycle. During one access review, a suspicious overnight login pointed to a decommissioned shared mailbox that still had an active application password tied to an old copier workflow. The technical signal looked minor at first, but the underlying issue was incomplete identity retirement and no documented exception record; the fix was not just disabling the login, but correcting the lifecycle process so stale credentials could not persist unseen.
How can leadership tell whether controls are real and functioning?
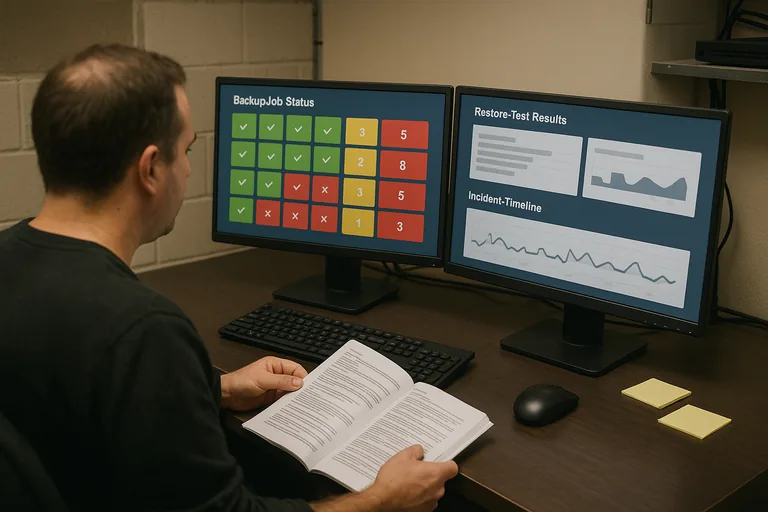
A competent provider or internal team should be able to show operational evidence, not just describe intentions. That evidence usually includes an accurate asset inventory, patch compliance reports, access review logs, vulnerability scan summaries, change records, incident timelines, and exception tracking that shows who approved deviations and when they expire. A common failure point is assuming a tool equals a control; in practice, the issue is rarely the tool alone, it is the process around it. If leadership cannot see review cadence, escalation ownership, and proof that findings are closed, the environment may be more dependent on habit than on controlled operations.
When does weak implementation become dangerous?
This tends to break down when controls exist on paper but are not validated. A common failure point is partial enforcement: multifactor authentication is enabled for email but not for privileged accounts, endpoint protection is installed but exclusions were never reviewed, or access is removed informally without an audit trail. During incident response, it is common to discover that nobody can quickly confirm which vendor had remote access, whether a terminated employee’s cloud tokens were revoked, or which systems missed security updates. That uncertainty expands scope, slows containment, increases regulatory exposure, and turns a manageable issue into a business interruption event.
What should a Sparks business do next?
Start with a practical review of obligations, systems, and ownership. Leadership should know which data types create legal or contractual exposure, which applications are critical to operations, who approves user and vendor access, how exceptions are documented, and what evidence exists to prove controls are being reviewed. If those answers depend on one person’s memory, the environment needs structure: a risk register, named control owners, documented review cadence, and verification steps that show what is working and what still needs remediation.

