Compliance & Risk Management
Compliance and risk management gives leadership a structured way to identify technology exposure, document obligations, assign control ownership, and reduce avoidable downtime, security incidents, and audit stress before weak processes turn into expensive business problems.
During a cyber insurance renewal, Adam V. learned an old administrator account still had remote access to Microsoft 365 and the finance system, where it had been used to create hidden invoice-forwarding rules. The fraud review, payment delays, and emergency cleanup cost $52,000 and exposed control gaps the business thought were already covered.
{HOOK_DISCLOSURE}
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage secure infrastructure, maintain stable operations, recover from outages, and reduce operational risk across compliance-aware technology environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Compliance & Risk Management because mature environments depend on documented controls, recovery readiness, disciplined change management, and proof that systems are being maintained consistently in real business settings, including Reno and Sparks organizations that need resilient technology operations.
This article explains common compliance and risk management practices in business IT environments and how decision-makers can evaluate them. This is general technical information; specific network environments and compliance obligations change strategy.
In business operations, compliance and risk management is the discipline of identifying what data, systems, vendors, and workflows create legal, security, or continuity exposure, then assigning controls and owners so those exposures are managed instead of ignored. A common failure point is treating compliance as paperwork while the real risk sits in unreviewed access, unsupported software, undocumented vendor connections, or recovery steps that exist only in someone’s memory.
- Obligations: A business needs to know which laws, contracts, insurer requirements, and customer expectations actually apply to its systems and data.
- Risk ownership: Important assets, likely threats, and acceptable exceptions should be documented so responsibility is clear before a problem occurs.
- Control evidence: Policies only matter when they are backed by access reviews, patching records, logging, testing, and documented response workflows.
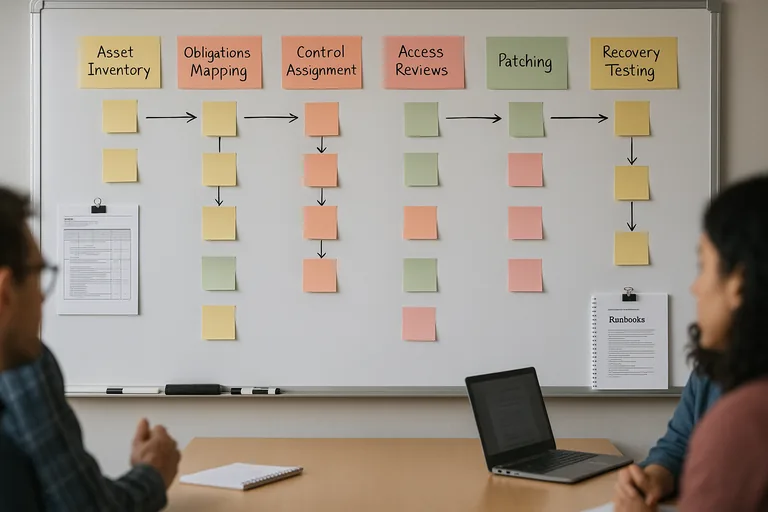
When this work is handled properly, it connects governance to operations. Leadership should be able to trace a business obligation to a technical control, a responsible person, and supporting evidence, which is where managed IT services often intersect with audit readiness, business continuity, vendor oversight, and day-to-day infrastructure stability.
What does compliance and risk management actually mean in a business IT environment?
It means translating obligations into repeatable operating controls. A policy may say sensitive data must be protected, but the operational version of that policy is much more concrete: approved access groups, multifactor authentication, encrypted devices, monitored admin accounts, documented vendor access, and a review cadence that shows those controls are still active. What usually separates a stable environment from a fragile one is not the policy binder; it is whether ownership, evidence, and exception handling exist when a system changes.
Why does it matter beyond passing an audit?
Because the cost of weak control management usually shows up in disrupted operations before it shows up in formal penalties. For Nevada businesses, Nevada Revised Statutes NRS 603A matters because it requires reasonable security measures and breach notification when protected personal information is exposed. In practice, that turns a missed laptop encryption setting, a badly offboarded employee, or an unvetted vendor connection into legal exposure, insurance friction, customer distrust, and management time lost to investigation.
Which operational risks does it usually reduce?
It usually reduces identity abuse, data handling mistakes, vendor exposure, and avoidable downtime caused by unmanaged change. Guidance in NIST SP 800-63B exists because user identity is often the easiest path into a business environment; stronger authentication only helps when account lifecycle management is consistent from onboarding through termination. In mature environments, this work also limits privilege sprawl, unsupported software, shadow IT, and the common situation where one overlooked system falls outside patching, logging, or backup policy and becomes the weakest point in the business.
How does competent compliance and risk management work in practice?
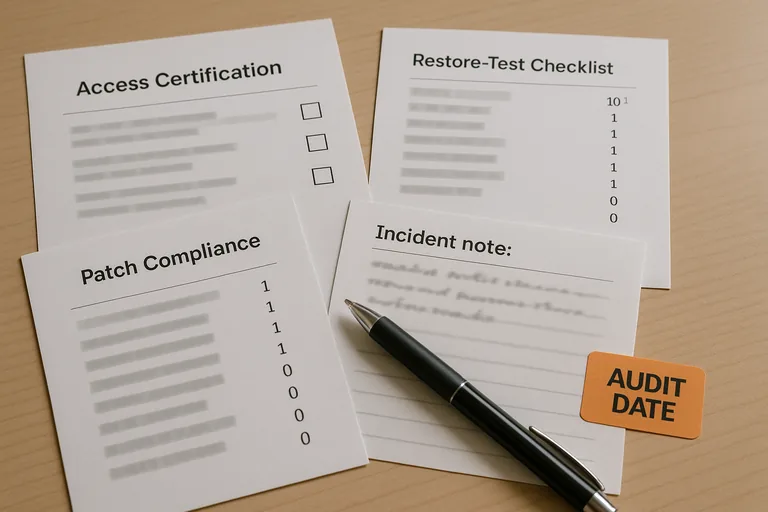
In mature environments, the process is cyclical rather than reactive: maintain a current asset inventory, classify data, map obligations to controls, assign owners, review vendor access, enforce patching and endpoint standards, confirm logging coverage, and document exceptions with a review date. During a routine access certification, a VPN log may show nightly connections from a disabled employee account; investigation often finds the user was removed from Microsoft 365 but never removed from the firewall or line-of-business application, which means offboarding was partial and undocumented. That is why compliance-aware managed IT operations should produce joiner-mover-leaver checklists, change records, access approvals, vulnerability summaries, and incident playbooks instead of relying on verbal confirmation that everything is under control.
How can a business tell whether controls are real or just assumed?
- Access reviews: There should be dated reports showing who reviewed privileged access, former-user access, and service accounts, along with what was removed or formally approved as an exception.
- Patch evidence: A mature environment produces patch compliance reports and documented remediation for systems that missed updates, not just a statement that updates are automatic.
- Monitoring and response: Dashboards matter, but alert escalation logs matter more because they show whether someone investigated, documented, and closed suspicious events.
- Recovery readiness: Incident playbooks, restore test records, and ownership assignments show that continuity plans can support real recovery rather than existing only as policy language.
When does weak implementation become dangerous?
This tends to break down when a business has policies on paper but no operating cadence behind them. A common failure point is quarterly reviews that are never held, multifactor authentication enabled for email but not for VPN or administrator tools, vendor questionnaires answered from memory, and exceptions granted without expiration or follow-up. In that condition, risk management oversight looks complete until an insurance application, customer audit, or incident investigation exposes missing evidence, unclear ownership, and months of unmanaged exposure that nobody realized had accumulated.
What should leadership do next?
Leadership should ask for a current list of critical systems, the obligations tied to those systems, the named owner for each control, and the evidence that the control was reviewed recently. A competent provider should be able to explain where access review records live, how exceptions are tracked, how incident response is escalated, and what reporting proves patching, logging, and offboarding are working. If those answers depend on memory, scattered spreadsheets, or one employee who “usually handles it,” the environment needs structure before the next disruption tests it.

