Backup & Disaster Recovery in South Lake Tahoe, California
Backup and disaster recovery in South Lake Tahoe, California helps businesses protect critical data, restore systems after outages or cyber incidents, and limit downtime with tested recovery procedures, secure backup storage, and clear restoration priorities.
After a winter power event in South Lake Tahoe, Angie P.‘s office learned the virtual server backup chain had been corrupt for weeks. Payroll, reservations, and billing stopped for two business days, and emergency recovery, overtime, and lost work reached $69,800.
{HOOK_DISCLOSURE}
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage stable infrastructure, reduce security exposure, and recover cleanly from outages, ransomware, hardware failures, and data-loss events. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Backup & Disaster Recovery in South Lake Tahoe, California because experienced IT teams do not stop at installing backup software; they define recovery priorities, protect backup access, monitor job health, test restores, and keep documentation current so downtime, security exposure, and operational risk are reduced in real business environments. Scott Morris’s work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience, including support for Reno and Sparks businesses that need accountable technology operations.
The article explains common operational patterns, not legal, insurance, or regulatory advice. This is general technical information; specific network environments and compliance obligations change strategy. Retention, downtime tolerance, and reporting obligations should always be reviewed against the actual systems and contracts involved.
Backup and disaster recovery is not one tool. It is the combination of protected data copies, restoration priorities, documented procedures, and the people responsible for using them under pressure. A solid backup and disaster recovery strategy defines how much data loss is acceptable, how long each system can be unavailable, and where clean recovery copies live when the primary environment is damaged.
- Backup scope: Critical file shares, line-of-business applications, Microsoft 365 or other SaaS data, server images, network device configurations, and sometimes endpoint data all need an intentional protection decision.
- Recovery objectives: Recovery point objective tells you how much recent data can be lost, and recovery time objective tells you how long the business can operate without the system.
- Isolation and documentation: Backups should not depend on the same credentials, storage, or physical site as production, and restore steps should be documented in the order systems must come back.
In South Lake Tahoe, continuity planning also has to account for weather disruption, power instability, and dependence on remote platforms when staff cannot work from the office. Businesses that already use managed IT services in South Lake Tahoe usually recover faster when infrastructure details, user access, vendor contacts, and restoration responsibilities are documented before the incident rather than assembled during it.
What does backup and disaster recovery actually include for a South Lake Tahoe business?
It includes more than copying files to another device. In a business setting, backup means preserving recoverable copies of data and systems, while disaster recovery means having a workable process to restore the right services in the right order after server failure, accidental deletion, malware, cloud sync errors, site loss, or a major configuration mistake. For many South Lake Tahoe organizations, that scope reaches beyond the file server to reservations systems, accounting platforms, email, shared drives, firewall settings, and the credentials needed to reconnect staff quickly.
Why do backup success messages often create false confidence?
A common failure point is assuming that a green check mark means the business is recoverable. In practice, backup jobs can complete even when application-consistent snapshots are missing, cloud copies have stopped replicating, retention is too short, or newer systems were never added to protection. What usually separates a stable environment from a fragile one is not the software alone; it is whether someone is reviewing failures, validating coverage against the asset list, and confirming that the restored data is usable by the business rather than merely present on storage.
What risks can a mature backup and disaster recovery program reduce?
A mature program can reduce downtime from hardware failure, corrupted virtual machines, deleted files, ransomware, vendor outages, and site-level disruption. It also limits secondary damage: missed billing cycles, payroll delays, contractual issues, customer service disruption, and rushed recovery decisions that create security gaps. Backup systems are only one part of continuity, but in mature environments they work alongside monitoring, identity controls, patch discipline, and documented escalation so the business can recover with less confusion and lower financial impact.
How does backup and disaster recovery work in practice during a real incident?
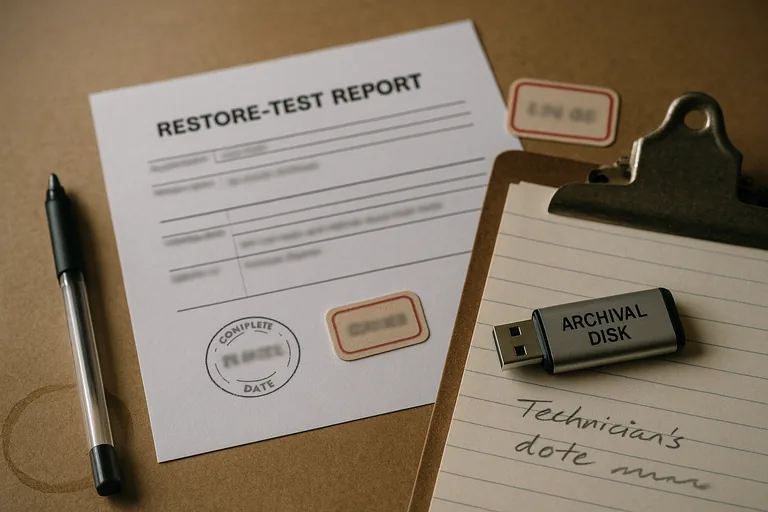
In practice, mature environments run scheduled jobs, replicate data offsite or to immutable storage, monitor each job, and test restores against defined recovery objectives. During a routine review, a storage alert showed backup jobs were reporting success but the offsite copy had been failing for 11 days after an expired API credential; the local repository was the only usable copy, which meant a building-level event would have left nothing recoverable outside the office. That is why guidance from CISA on data backup and networked storage emphasizes the 3-2-1 approach and protection against tampering. A competent team also documents restoration order, often starting with identity services, virtualization hosts, critical applications, shared data, and then user workstations, so recovery follows business dependency rather than panic.

How can a business tell whether its recovery environment is competently managed?
A competent provider should be able to explain exactly what is protected, where copies are stored, who receives failure alerts, how access to the backup console is restricted, and what the last restore test proved. Real evidence matters: a current asset inventory matched to backup scope, recovery point and recovery time targets by system, daily job review records, immutable or offline copy confirmation, and documented restore test results showing that files, virtual machines, and line-of-business data were recovered successfully within expectation. If a business recovery program cannot produce those records, the issue is usually not the product but the missing operational discipline around it.
When does weak implementation become dangerous?
This tends to break down when the backup appliance is joined to the same domain as production, the same privileged credentials manage both environments, SaaS data is assumed to be retained forever, or alerts go to a mailbox nobody reviews. In environments that have not been reviewed recently, it is common to find decommissioned servers still listed in reports while newer cloud workloads have no protection at all. The real danger is false confidence: leadership believes recovery exists until an outage exposes encrypted repositories, missing encryption keys, undocumented restore dependencies, or a retention policy that removed the only clean version before anyone noticed.

