Reno Law Firm IT
What looks like a one-off issue is often tied to hidden threats. In law firm environments, stolen credentials, MFA gaps, and weak monitoring can turn into ransomware, fraud, and data loss long before anyone notices the warning signs. Closing those gaps early makes managed cybersecurity programs far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Hidden Credential Abuse Brings Law Firm Systems Down
When a law firm in Washoe County reports that systems are suddenly unavailable, the root cause is often not a failed server or a bad internet circuit. More often, it is an invisible threat already inside the environment. Modern attackers do not need to break through the perimeter if they can log in with a valid username, a reused password, or a session token captured from an unmanaged device. That is why firms relying only on firewalls and basic antivirus still end up with document management outages, locked accounts, suspicious forwarding rules, and missing access to case files.
We see this pattern regularly in legal environments where Microsoft 365, remote access, e-filing portals, and shared storage all depend on identity security. If MFA is inconsistently enforced, if sign-in alerts are not reviewed, or if privileged accounts are not separated from daily use, a small compromise can spread quietly. For firms trying to reduce exposure, structured cybersecurity services in Washoe County are less about adding noise and more about finding the login activity your firewall will never see. In incidents like the one affecting Natalie’s office workflow, the visible outage is usually the last symptom, not the first.
- Identity compromise: Stolen credentials, legacy authentication, and weak MFA coverage allow attackers to access email, cloud storage, and line-of-business systems without triggering traditional perimeter alarms.
- Monitoring gaps: Without centralized alerting on impossible travel, mailbox rule changes, privilege escalation, and abnormal file access, firms often discover the problem only after staff cannot work.
- Operational impact: In a legal practice, even a short interruption affects billable hours, filing deadlines, client communications, and document integrity across multiple users at once.
Practical Remediation for Law Firms in Washoe County
The fix is not a single tool. It is a layered response that starts with identity hardening, then adds visibility, containment, and recovery discipline. We typically begin by reviewing conditional access, disabling legacy protocols, enforcing phishing-resistant or app-based MFA, separating admin accounts, and validating that endpoint detection is actually reporting to a monitored console. For firms handling regulated or sensitive client data, this work should align with documented oversight such as compliance-focused IT management so security controls match retention, privacy, and audit expectations.
From there, the environment needs tested response steps. That includes mailbox auditing, sign-in log review, endpoint isolation procedures, privileged access review, and backup verification for both cloud and local data. The most useful outside guidance for this type of incident remains CISA’s recommendations on strong authentication and account protection , because the issue is usually identity misuse before it becomes ransomware or fraud.
- MFA hardening: Require MFA for all users, block legacy authentication, and apply conditional access policies by role, device, and location.
- EDR and alerting: Deploy monitored endpoint detection with alerts for suspicious sign-ins, token abuse, and lateral movement indicators.
- Access control: Remove standing admin rights, review shared mailbox permissions, and limit who can alter forwarding rules or retention settings.
- Recovery validation: Confirm that file, email, and system backups are recoverable and that restore priorities are documented before the next incident.
Field Evidence: Credential Abuse Hidden Behind a Routine Outage
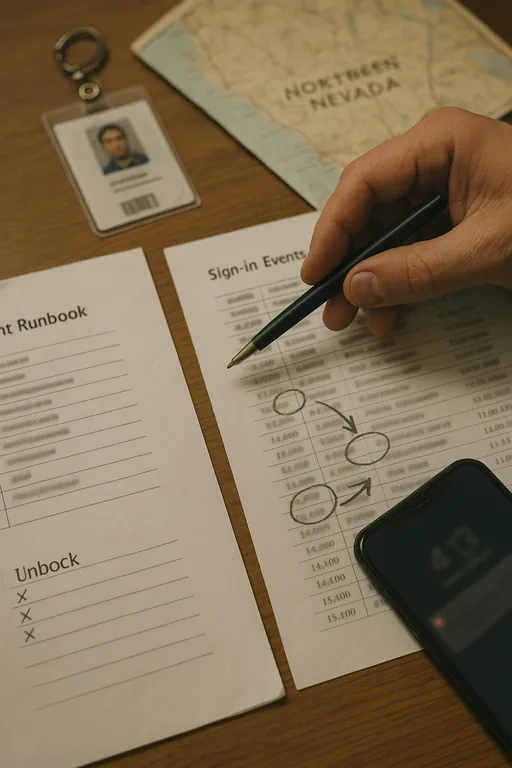
In one Northern Nevada legal office corridor, the initial complaint was simple: staff could not open matter folders and email prompts kept reappearing. Before remediation, the firm had inconsistent MFA enrollment, no meaningful review of Microsoft 365 sign-in anomalies, and backup assumptions that had never been tested against a real access failure. The issue looked like a workstation problem until mailbox rules, failed token refreshes, and unusual after-hours access patterns showed otherwise.
After the firm tightened identity controls, enabled monitored endpoint visibility, and validated backup and disaster recovery for business continuity , the operating picture changed. Instead of discovering problems after attorneys lost access, the team had earlier warning through sign-in alerts and clearer isolation steps. That matters in Washoe County, where firms may be balancing downtown Reno offices, remote staff, court deadlines, and weather-related travel delays in the same week.
- Result: Suspicious sign-in events were identified in minutes instead of hours, priority file access was restored the same day, and the firm reduced repeat account lockout incidents over the following quarter.
Reference Points for Hidden Threat Control in Legal Environments
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.

Local Support in Washoe County
Reno Computer Services supports firms across Reno, Sparks, and the broader Washoe County area where legal offices often depend on cloud identity, secure remote access, and fast recovery from account-based incidents. From our Ryland Street office, the route to the Rattlesnake Mountain area is typically about 17 minutes, which is why remote visibility, alerting, and documented response steps matter before an on-site visit is even underway.
What Law Firms Should Take Away from Invisible Threat Incidents
If a law firm in Washoe County has systems down and the cause is not immediately obvious, identity compromise should be high on the list. Stolen credentials, weak MFA enforcement, and poor monitoring create the kind of silent exposure that can sit unnoticed until staff lose access, billing is interrupted, or client data handling becomes a compliance concern.
The practical takeaway is straightforward: treat account security, alert review, and tested recovery as core operations, not optional add-ons. Firms that do this well usually detect abnormal behavior earlier, contain incidents faster, and avoid turning a login problem into a full business interruption.

