Reno Law Firm Audit
What looks like a one-off issue is often tied to compliance gaps. In law firm environments, missing controls, weak documentation, and loose access policies can turn into audit findings, fines, and operational disruption long before anyone notices the warning signs. Closing those gaps early makes managed cybersecurity services far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why a Law Firm Outage Often Starts with a Compliance Gap
When systems go down in a law firm, the outage is rarely just a hardware event. In most cases, the real issue is that required controls were never fully documented, reviewed, or enforced. We see this in Washoe County firms that have grown quickly, added cloud tools, changed staff roles, or inherited older line-of-business systems without updating access policies and recovery procedures. The immediate symptom may be lost access to files, email, or practice-management software, but the root cause is often weak governance around identity, retention, logging, and backup validation.
That is where managed cybersecurity services in Washoe County become operationally important. A law office handling client records, financial data, and privileged communications cannot rely on informal processes when regulations and contractual requirements change faster than internal IT documentation. Braxton’s outage is a good example of how stale permissions and missing evidence of control testing can create both downtime and audit exposure at the same time.
- Access control drift: User permissions often expand over time as attorneys, paralegals, and support staff change roles, creating unnecessary exposure and making outages harder to isolate.
- Documentation gaps: If recovery steps, vendor dependencies, and system ownership are not current, even a short disruption takes longer to diagnose and restore.
- Framework misalignment: Requirements tied to HIPAA, CMMC, client security questionnaires, or cyber insurance can outpace internal review cycles, leaving firms noncompliant without realizing it.
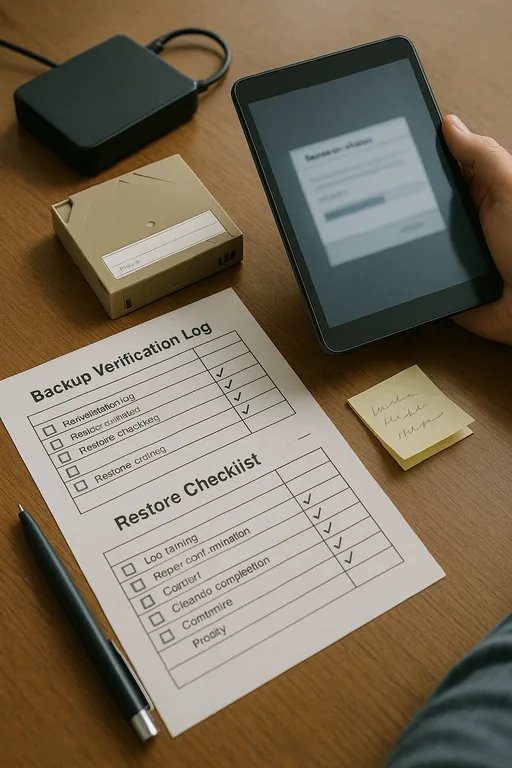
- Unverified recovery readiness: Backups that exist but are not routinely tested may satisfy a checklist on paper while failing under actual pressure.
How to Close the Gap Before the Next Audit or Outage
The practical fix is not a single tool. Law firms need a repeatable control structure that ties security, documentation, and recovery together. We typically start by mapping systems to business function: case files, billing, intake, email, remote access, and document storage. From there, we review who has access, how that access is approved, what logs are retained, and whether recovery steps have been tested against real failure scenarios. Endpoint visibility also matters, especially when attorneys work remotely between Reno, Sparks, Carson City, and court or client locations.
A strong remediation plan usually includes hardened authentication, documented role-based access, tested backups, and better endpoint telemetry through endpoint and threat protection for law office systems . For firms trying to align controls with recognized guidance, the CISA Cybersecurity Performance Goals provide a practical baseline for identity security, asset visibility, backups, and incident response.
- Identity review: Remove stale accounts, enforce MFA, and align permissions to actual job roles rather than historical convenience.
- Backup validation: Test restores on a schedule, document recovery time expectations, and verify that legal document repositories can be recovered intact.
- Endpoint controls: Deploy EDR, isolate unmanaged devices, and improve alerting so suspicious activity is caught before it becomes an outage.
- Policy evidence: Maintain current documentation for onboarding, offboarding, privileged access, retention, and incident handling so audits are supported by evidence, not memory.
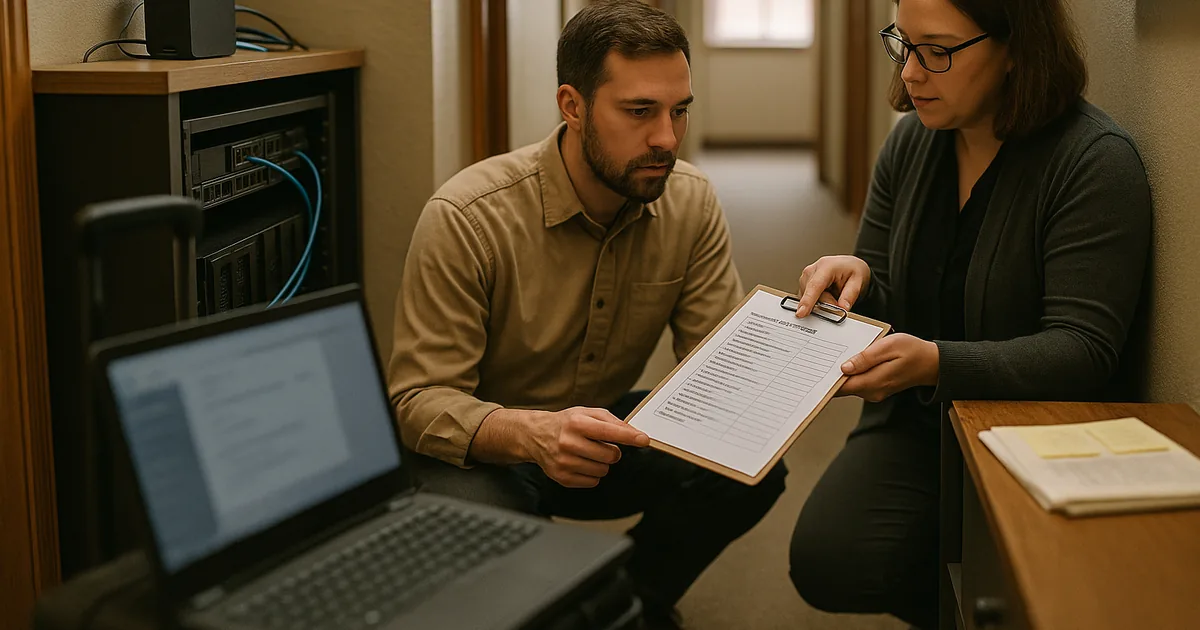
Field Evidence: Downtown Firm Restores Stability After Control Review
In one Northern Nevada legal office corridor, the initial complaint was simple: intermittent lockouts, slow file access, and uncertainty about whether archived matter data could be restored. The deeper review showed overlapping admin rights, inconsistent endpoint policies, and no recent proof that backup jobs had been tested against the firm’s actual document workflow. After a structured remediation effort, the firm moved from reactive troubleshooting to documented control ownership and predictable recovery procedures.
Part of that improvement came from tightening user security around email, identity, and remote access with compliance-focused identity and email security . That matters in Washoe County, where small firms often operate with a mix of office-based staff, hybrid users, and older buildings that complicate network upgrades. Once controls were documented and tested, support calls dropped and recovery confidence improved.
- Result: Unplanned access interruptions were reduced by 70 percent over the next quarter, backup restore testing moved to a documented monthly schedule, and audit preparation time dropped from several days to a few hours.
Compliance Gap Audit Reference Points for Law Firms
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Services and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.

Local Support in Washoe County
Our office on Ryland Street supports firms across Reno, Sparks, and the broader Washoe County area. For downtown law practices, response planning is not just about distance. It is about knowing how local offices operate, how quickly staff need access restored, and how compliance documentation holds up when systems are under pressure. The route from Reno Computer Services to 10 N Virginia St is typically about 3 minutes, which helps when an issue needs both remote triage and local coordination.
Compliance Gaps Need to Be Treated as Operational Risks
For law firms in Washoe County, systems going down is often the visible result of a deeper control failure. Missing documentation, inconsistent access management, and untested recovery processes create the conditions for both downtime and audit trouble. The longer those gaps remain hidden, the more expensive the eventual interruption becomes.
The practical takeaway is straightforward: review controls before they are tested by an outage, client questionnaire, insurance renewal, or formal audit. Firms that align identity, endpoint security, backup validation, and written procedures are in a much stronger position to keep legal operations moving without unnecessary disruption.

