Reno/Sparks Law Firm Risk
The outage or lockout is usually the last symptom to appear, not the first. Phishing clicks, password reuse, and weak account hygiene create weak points that can disrupt backup and disaster recovery and put account security, access stability, and business continuity at risk. Reducing that risk starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Human Error Shuts Down Law Firm Operations Faster Than Most Technical Failures
For law firms in Sparks, the human element is often the first break in the chain. The visible problem may look like a system outage, a locked account, or missing access to files, but the root cause is frequently much simpler: a user clicks a convincing reset link, reuses a password already exposed elsewhere, or approves a sign-in prompt without verifying the request. Once that happens, attackers do not need to break the firewall. They use valid credentials to move through email, cloud storage, and line-of-business systems in ways that look normal at first.
This is where backup and disaster recovery gets misunderstood. Many firms assume backups solve the problem, but compromised identities can interfere with recovery timing, retention integrity, and access to the very systems needed during an incident. We regularly see firms improve resilience by pairing recovery planning with stronger identity controls and backup and disaster recovery support in Northern Nevada that accounts for account compromise, not just server failure. In a legal environment, where deadlines, trust accounting, document retention, and privileged communications all matter, a single bad click can create cascading operational issues long before anyone realizes what happened. That is why incidents like the one affecting Adalyn rarely stay isolated to one inbox or one workstation.
- Identity compromise: A stolen or reused password can give an attacker access to email, cloud files, and administrative settings, which can interrupt document retrieval, alter mailbox rules, and delay recovery actions.
- Weak account hygiene: Shared credentials, stale accounts, and missing MFA enforcement increase the chance that one user mistake becomes a firm-wide access problem.
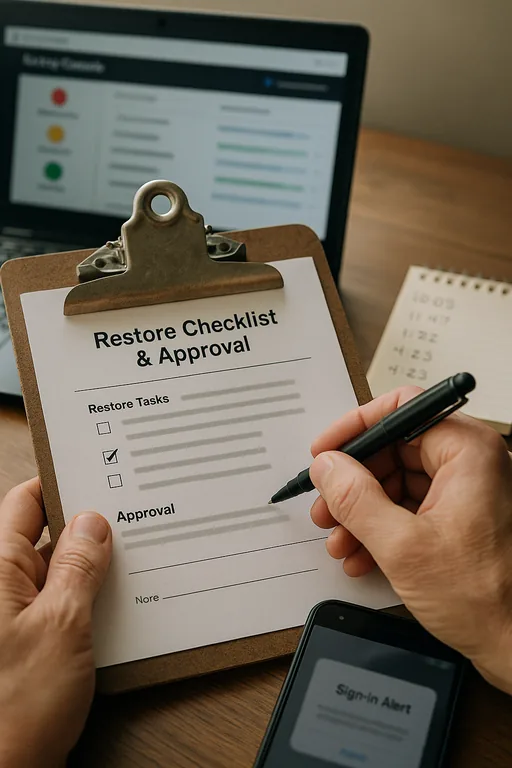
- Recovery dependency: If backup alerts, restore approvals, or cloud admin roles depend on the same compromised accounts, recovery slows down at the exact moment the firm needs speed and certainty.
- Legal workflow disruption: Intake, calendaring, e-filing preparation, and billing all depend on stable access, so even a short lockout can affect revenue and client service.
Practical Controls That Reduce Human-Driven Downtime
The fix is not a single product. It is a layered operating model that assumes users will occasionally make mistakes and builds controls around that reality. For most firms, that starts with phishing-resistant MFA where possible, conditional access policies, mailbox auditing, privileged account separation, and endpoint detection that can isolate suspicious behavior quickly. It also means testing whether backup administrators, cloud tenants, and restore workflows remain usable if a primary user account is compromised.
We also advise firms to treat this as a leadership and process issue, not just a help desk issue. Clear approval paths, documented incident roles, and regular review of access rights are part of effective strategic IT leadership for regulated business operations . For practical guidance on reducing phishing and credential abuse, CISA’s recommendations on strong passwords and account security are useful because they align with what works in day-to-day business environments.
- MFA hardening: Enforce MFA across email, document systems, VPN, and backup consoles, with stronger methods for administrators and finance-related users.
- Conditional access: Restrict risky sign-ins by geography, device state, impossible travel, and legacy authentication.
- Mailbox and sign-in monitoring: Alert on forwarding rule creation, repeated failed logins, unusual token activity, and privilege changes.
- Backup validation: Confirm restores can be performed by protected admin accounts that are separate from daily user identities.
- User conditioning: Run short, recurring phishing simulations and reset training around real examples rather than annual checkbox sessions.
Field Evidence: Credential Abuse Contained Before a Full-Day Lockout
We worked through a similar pattern for a professional office operating between Sparks and Reno with staff moving between court-related deadlines, remote email access, and shared document repositories. Before remediation, the firm had inconsistent MFA enrollment, broad admin permissions, and no clear alerting for suspicious mailbox changes. A single compromised account created confusion around whether files were missing, whether backups were intact, and whether staff should stop using email altogether.
After tightening identity controls, separating admin access, validating restore procedures, and aligning future spending through IT planning and budgeting for continuity-focused operations , the firm moved from reactive cleanup to a controlled response model. The next suspicious sign-in was contained within minutes instead of turning into a half-day interruption. That matters in Northern Nevada, where smaller offices often rely on a lean internal team and cannot afford repeated downtime during busy filing periods or end-of-month billing cycles.
- Result: Suspicious account activity was isolated in under 15 minutes, no production data restore was required, and the firm reduced unplanned access-related downtime by more than 70 percent over the following quarter.
Reference Guide: Human Element Risks in Legal IT Environments
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Backup And Disaster Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, and Northern Nevada and Northern Nevada.

Local Support in Sparks, Reno, and Northern Nevada
Law firms in Sparks often depend on fast coordination between cloud systems, document access, and staff working across Reno-area offices and court-related schedules. From our office on Ryland Street, we support organizations throughout the region with practical response and recovery work, including the Dandini area where even a short credential-related lockout can disrupt billing, intake, and case preparation.
Reduce the Risk Before the Lockout Becomes the Outage
When systems go down in a law firm, the visible disruption often starts with a person, not a platform. A phishing click, reused password, or weak approval habit can interrupt email, document access, and recovery workflows quickly, especially in smaller offices where the same accounts touch daily work and administrative control.
The practical takeaway is straightforward: backup and disaster recovery only works well when identity security, access discipline, and response procedures are built around real user behavior. Firms in Sparks and the surrounding Reno market are better served by tightening those controls early than by trying to sort them out during a billing delay or client communication problem.

