Reno/Sparks Law Firm IT
The outage or lockout is usually the last symptom to appear, not the first. Surprise spending, delayed upgrades, and aging infrastructure create weak points that can disrupt regulatory compliance support and put budget control, resilience, and uptime at risk. Reducing that risk starts with planning upgrades deliberately and aligning IT decisions to business risk.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Financial Roadmap Gaps Turn Into Law Firm Downtime
When systems go down in a Sparks law office, the visible failure is often a server crash, login lockout, or inaccessible case files. The underlying problem is usually financial planning, not just technology. Without a vCIO function, IT becomes a surprise expense instead of a controlled operating line. Hardware stays in service past its safe lifecycle, licensing renewals get deferred, backup storage is undersized, and compliance-related controls are added only after an incident forces the issue.
For firms handling regulated client information, that pattern creates risk on several fronts at once. Aging infrastructure affects uptime, but it also affects retention, audit readiness, access control, and recovery confidence. In practice, we see firms benefit from structured regulatory compliance support in Northern Nevada because it ties budgeting decisions to operational risk instead of waiting for a failure to expose the gap. That is the point many firms miss: the financial roadmap is not separate from resilience; it determines whether resilience is affordable, scheduled, and tested.
In the Sparks and Reno corridor, this issue is amplified by multi-office workflows, court deadlines, remote access expectations, and the reality that older buildings may still have network closets, power protection, or cabling that were never designed for current document-management and security demands. By the time Julian saw users locked out of active matters, the real problem had already been developing for months through delayed refresh decisions and reactive spending.
- Deferred infrastructure lifecycle: Servers, firewalls, storage arrays, and line-of-business systems that stay in production too long create a higher chance of outage, slower recovery, and compliance support gaps during audits or incident review.
- Unplanned budget behavior: When IT is approved only as emergencies arise, firms tend to fund break-fix work but postpone strategic upgrades, creating uneven protection across endpoints, backups, and access controls.
- Compliance dependency on uptime: Legal operations rely on consistent access to files, email, billing, and retention systems; downtime quickly becomes a records, response-time, and client-service problem.
How To Correct The Risk Before The Next Outage
The practical fix is to move from reactive spending to a documented roadmap with refresh dates, recovery targets, and compliance-driven priorities. That means identifying end-of-life systems, ranking them by business impact, and assigning budget windows before failure occurs. For law firms, we typically start with file systems, identity controls, backup retention, and the devices used for remote document access. From there, we align the roadmap to actual business deadlines such as case activity, billing cycles, and records retention obligations.
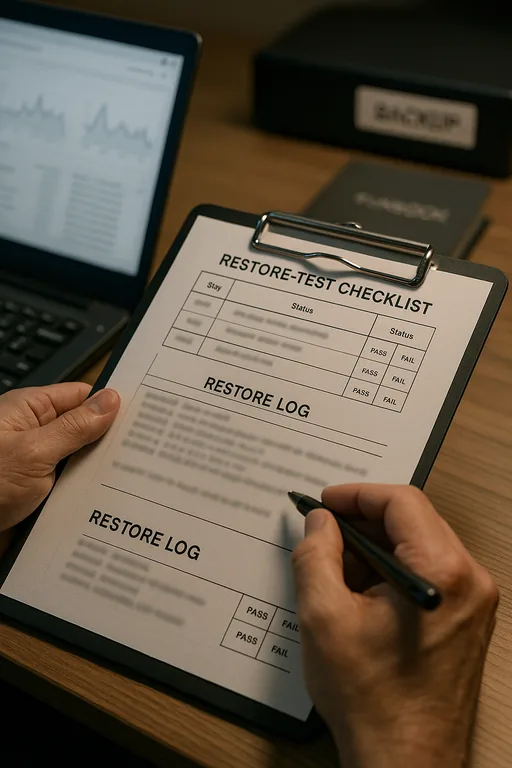
Remediation also requires proving that recovery works, not assuming it does. Firms with recurring risk usually need stronger business continuity and backup compliance controls so they can restore matter data, email, and shared drives within defined recovery objectives. Guidance from CISA is useful here because it emphasizes tested backups, access hardening, and incident preparation rather than relying on a single defensive tool.
- Lifecycle planning: Build a 12- to 36-month refresh schedule for servers, storage, firewalls, and critical workstations so replacement happens before instability affects operations.
- Backup validation: Run scheduled restore tests for document repositories, billing systems, and shared folders to confirm recovery time and data integrity.
- MFA and identity hardening: Protect remote access, Microsoft 365, and privileged accounts with enforced MFA, conditional access, and role-based permissions.
- Alerting improvements: Configure monitoring for disk health, failed jobs, storage thresholds, and authentication anomalies so support teams see degradation before users do.
- Business-risk budgeting: Tie each IT investment to a measurable risk reduction such as lower downtime exposure, faster recovery, or improved audit readiness.
Field Evidence: Stabilizing A Sparks Legal Operations Environment
We worked through a similar Northern Nevada pattern where a professional office near the Sparks business corridor had no reliable replacement schedule for its core server, backup appliance, or firewall. Before remediation, the environment had inconsistent patching, backup jobs that were completing without meaningful restore testing, and no clear budget path for replacing aging equipment. Staff could continue working most days, but every quarter brought another interruption, usually around billing runs or document-heavy deadlines.
After a structured review, the organization moved to staged hardware replacement, documented recovery testing, and a budgeted roadmap tied to operational risk. We also added a separate recovery workflow using backup and recovery programs built for business continuity so file access and shared data could be restored without rebuilding the entire environment first. In a region where weather events, power fluctuations, and travel time between Reno and Sparks can affect response windows, that preparation materially reduced downtime exposure.
- Result: Unplanned infrastructure incidents dropped from multiple service interruptions per quarter to one minor event in nine months, and tested file recovery time improved from most of a workday to under 90 minutes.
Financial Roadmap Controls For Compliance-Focused Firms
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Regulatory Compliance Support and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, and Northern Nevada and Northern Nevada.

Local Support in Sparks, Reno, and Northern Nevada
Reno Computer Services supports organizations across Reno and Sparks where travel time, building age, and multi-site operations all affect how quickly an outage can be contained. For firms working between downtown Reno, Prater Way, and the broader Washoe County corridor, local support matters because recovery planning is not just remote monitoring; it also includes on-site validation, hardware coordination, and practical response when a critical system fails.
Planning IT As A Business Function Prevents Predictable Failures
For Sparks law firms, systems-down incidents are often the result of delayed decisions rather than isolated bad luck. When infrastructure, backup validation, and compliance controls are funded only after something breaks, the business absorbs the cost through downtime, delayed billing, and operational disruption.
A financial roadmap gives leadership a way to prioritize upgrades before they become emergencies. That approach improves uptime, supports compliance obligations, and turns IT from a surprise expense into a managed operational function with clearer risk control.

