Reno Law Firm IT
Problems like this tend to stay hidden until something important breaks. For law firms in South Meadows, that often means systems going down, avoidable delays, or a bigger recovery burden than expected. The best response is hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Hidden Identity Threats Take Law Firm Systems Down
When a law firm in South Meadows reports that systems are down, the visible outage is often only the last stage of the problem. The underlying issue is frequently identity misuse rather than a failed firewall or a dead server. Modern attackers do not always force entry. They log in with valid credentials, move through email, cloud apps, and endpoints, and stay quiet long enough to create confusion before operations fail. That is why the immediate symptom can look like random lockouts, missing files, slow machines, or repeated authentication prompts instead of a clear security alarm.
For legal offices, the impact is operational first and technical second. Intake slows down, document management becomes unreliable, billing entries get delayed, and staff start working around the problem in ways that increase risk. We see this most often where endpoint visibility is thin, sign-in anomalies are not reviewed, and device posture is inconsistent across attorneys, assistants, and remote users. Firms trying to reduce recurring outages usually need tighter proactive device and endpoint management so abnormal behavior on laptops, desktops, and mobile-connected systems is caught before it turns into downtime. In cases like Leon’s, the real failure was not one broken machine. It was the lack of coordinated visibility across users, devices, and cloud access.
- Credential misuse: A valid username and password can bypass perimeter assumptions and make malicious access look like normal user activity.
- Endpoint blind spots: Unmanaged or inconsistently patched devices give attackers room to persist after the first login event.
- Operational delay: Law firms depend on document access, calendaring, and secure communication, so even a short interruption can affect filings, client response times, and billable work.
- Local complexity: South Meadows firms often support hybrid work, court deadlines, and multi-device access patterns, which makes identity-based incidents harder to spot without centralized oversight.
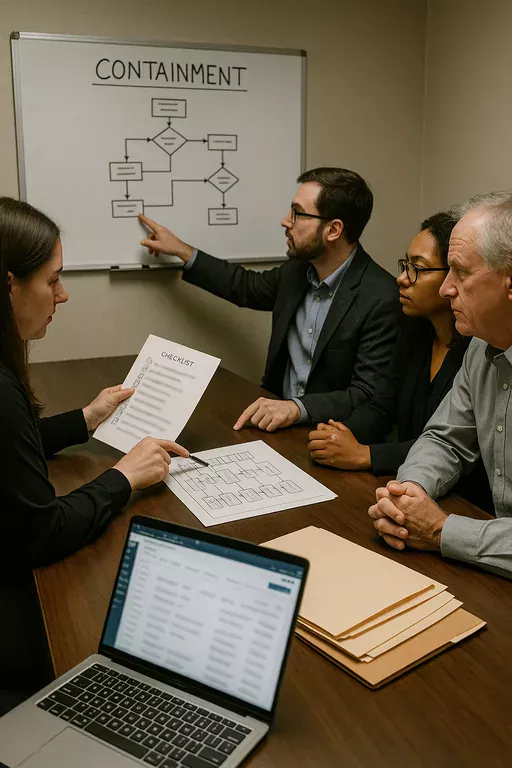
How To Contain The Threat And Keep It From Returning
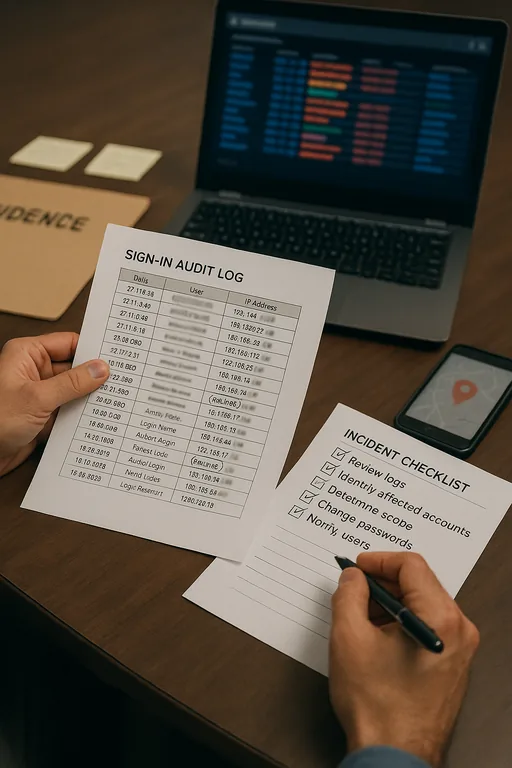
The fix starts with confirming whether the outage is tied to identity abuse, endpoint compromise, or both. We typically review sign-in logs, endpoint telemetry, conditional access events, mailbox rules, and recent privilege changes before making broad resets. For law firms, the goal is not just restoring access. It is restoring access safely, without leaving a stolen token, unmanaged device, or malicious persistence method in place.
From there, the practical controls are straightforward: enforce phishing-resistant or at least well-configured MFA, remove stale sessions, isolate affected endpoints, validate backup integrity, and tighten user risk policies. Firms that want to prevent the same issue from resurfacing usually need stronger identity and email security in Northern Nevada so suspicious sign-ins, impossible travel, inbox rule abuse, and privilege escalation are addressed as part of daily operations. Guidance from CISA remains useful here because credential theft is still one of the most common entry points in business incidents.
- Identity hardening: Require MFA across Microsoft 365, VPN, legal applications, and administrator accounts, then revoke active sessions after suspected compromise.
- Endpoint isolation: Use EDR to quarantine affected devices and review persistence mechanisms, browser tokens, and unauthorized remote tools.
- Conditional access: Block risky sign-ins by geography, device compliance state, and impossible travel indicators.
- Backup validation: Confirm that document repositories, profile data, and line-of-business systems can actually be restored within the firm’s recovery window.
- Alerting discipline: Route suspicious login and endpoint alerts into a monitored workflow so they are investigated before users report an outage.
Field Evidence: Before The Outage Looked Random, After The Pattern Was Clear
In one Northern Nevada legal environment, the initial report was inconsistent application failures, repeated password prompts, and intermittent access to shared matter folders. Staff assumed the issue was internet instability or a Microsoft problem. After review, the pattern showed repeated sign-ins from an unfamiliar source, token reuse on a workstation, and delayed response because the activity did not trigger a strong enough escalation path. Once the firm moved to tighter session control, endpoint containment, and better security monitoring and response for business systems , the same behavior became visible much earlier.
The before-and-after difference was operationally significant. Instead of discovering the problem only after attorneys could not work, the firm had a process to flag abnormal access before document systems and user sessions degraded. That matters in Northern Nevada, where firms may be balancing Reno office staff, remote users in Carson City, and court-driven deadlines that do not wait for troubleshooting.
- Result: Authentication-related disruptions dropped from repeated multi-hour incidents to isolated events contained in under 30 minutes, with no further broad workstation lockouts during the following quarter.
Reference Points For Invisible Threat Response
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Proactive Device And Endpoint Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.
Local Support in South Meadows, Reno, and Northern Nevada
We support firms across Reno and the surrounding service area from our Ryland Street office, including South Meadows practices that need a fast operational response when identity issues, endpoint failures, or access problems interrupt legal work. For this route, the estimated travel time to the referenced destination is about 26 minutes, which is why remote triage, log review, and containment steps matter before onsite work begins.
What Law Firms In South Meadows Should Take Away
If systems go down and the cause is not immediately obvious, the safest assumption is that the visible outage may be tied to a hidden identity or endpoint issue. For law firms, that means the response has to go beyond restarting devices or resetting one password. The real work is confirming how access was abused, what devices were affected, and whether the same weakness still exists elsewhere in the environment.
In practice, firms reduce repeat incidents by tightening identity controls, improving endpoint visibility, and treating abnormal sign-in behavior as an operational warning sign rather than background noise. That approach limits downtime, protects billable work, and gives legal teams a more predictable recovery path when something does go wrong.

