Reno Law Firm Audit
Problems like this tend to stay hidden until something important breaks. For law firms in South Meadows, that often means systems going down, avoidable delays, or a bigger recovery burden than expected. The best response is reviewing controls, access, and recovery steps before they are tested under pressure.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Compliance Gaps Turn Into Systems Down Events
When a law firm in South Meadows has systems go down, the immediate assumption is usually hardware failure, an internet issue, or a bad software update. In practice, we often find a broader compliance gap underneath the outage. Policies may say backups exist, access is controlled, and recovery is documented, but the actual environment tells a different story. Regulations and client security requirements change faster than many internal IT teams can document them, especially when legal staff are focused on casework, deadlines, and billing.
That gap matters because legal operations depend on reliable access to document management systems, email, scanned records, timekeeping, and line-of-business applications. If permissions drift, backup jobs are not tested, or recovery order is unclear, a routine incident becomes a business interruption. Firms trying to reduce that exposure typically need structured backup and recovery programs in Reno that verify whether protected data can actually be restored in the right order, within a realistic timeframe, and with the right access controls in place. That is where the difference shows up between a short disruption and a full day of lost legal work.
- Documentation drift: Security and recovery procedures often lag behind actual system changes, leaving firms exposed when staff, software, or regulatory expectations shift.
- Access control sprawl: Former users, shared credentials, and inconsistent MFA enforcement create confusion during outages and increase recovery risk.
- Unverified backups: A completed backup job does not confirm that case files, email archives, and practice-management data will restore cleanly.
- Priority mismatch: Critical systems such as document repositories and billing platforms are not always mapped to a clear recovery sequence.
- Operational consequence: As with Makayla’s situation, attorneys and support staff lose billable time quickly when they cannot trust file availability or system integrity.
What Practical Remediation Looks Like for a Law Firm
The fix is not a single tool. It is a disciplined review of controls, recovery logic, and system ownership. We start by identifying which systems are required for intake, active matters, calendaring, billing, and secure communication. From there, we validate backup scope, retention, restore testing, account permissions, MFA enforcement, and the order in which services must come back online. Firms with hybrid environments usually also benefit from tighter network server and cloud management in Northern Nevada so that local file access, Microsoft 365, and line-of-business applications are governed as one operating environment rather than separate silos.
For compliance-sensitive firms, remediation should align to a recognized control model instead of informal checklists. The CISA small business cyber guidance is a practical starting point because it emphasizes access control, backup discipline, incident response, and recovery planning in operational terms. For legal offices handling regulated or contract-sensitive data, that structure helps close the gap between what the firm believes is protected and what can actually be defended and restored under pressure.
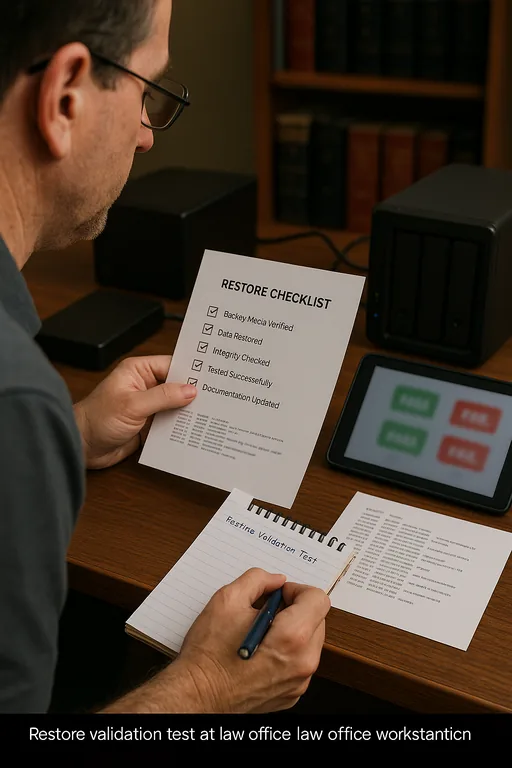
- Backup validation: Run scheduled restore tests for document stores, email, and practice-management data, not just backup job status checks.
- MFA hardening: Enforce MFA for email, remote access, admin accounts, and cloud applications with documented exception handling.
- Recovery sequencing: Define which systems must return first so attorneys can resume work without waiting on noncritical services.
- Alerting improvements: Set actionable alerts for failed backups, storage thresholds, account lockouts, and replication issues.
- Change control: Tie policy updates to actual infrastructure changes so compliance documentation stays current.
Field Evidence: Restoring Order After a Documentation Failure
We have seen this pattern in firms operating between South Meadows, Midtown, and downtown Reno where attorneys move between office, court, and remote work. Before remediation, the environment looked stable on paper: backups were running, cloud services were active, and staff had access. In reality, restore priorities were unclear, shared folders had inconsistent permissions, and no one had recently tested whether a full matter file could be recovered without manual cleanup.
After a structured audit and remediation cycle, the firm had a documented recovery order, tested restore points, cleaner account governance, and stronger segmentation across core systems with IT systems for multi-location operations . That reduced uncertainty during the next disruption caused by a building-side connectivity issue and shortened the return to productive work substantially.
- Result: Recovery testing improved from unverified backups to documented restores, and estimated downtime for a core file-access incident dropped from most of a workday to under 90 minutes.
Compliance Gap Audit Reference Points for Law Firms
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Backup And Recovery Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in South Meadows, Reno, Sparks, Carson City, and Northern Nevada
From our Reno office, we regularly support firms that need fast response across South Meadows and nearby business corridors. For legal offices, proximity helps, but the larger value is having documented recovery priorities, tested backups, and infrastructure oversight already in place before an outage affects filings, intake, or billing.
Closing the Gap Before the Next Outage
For law firms in South Meadows, systems going down is often the visible symptom of a quieter control problem. If backup scope is incomplete, access rules are inconsistent, or recovery steps have not been tested against current compliance requirements, even a short disruption can expand into missed work, delayed billing, and unnecessary recovery cost.
The practical takeaway is straightforward: review the controls behind the outage, not just the outage itself. When backup validation, access governance, and infrastructure dependencies are documented and tested, firms are in a much stronger position to keep legal operations moving and to recover cleanly when something does fail.

