Reno/Sparks Ops Stop
The outage or lockout is usually the last symptom to appear, not the first. Phishing clicks, password reuse, and weak account hygiene create weak points that can disrupt business continuity and backup compliance and put account security, access stability, and business continuity at risk. Reducing that risk starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

How Human Error Stops Logistics Operations

The human element is often the first control failure in a logistics environment, especially when staff move quickly between dispatch, receiving, scheduling, and billing. In Sparks operations, we commonly see the visible outage happen after the real problem has already been in motion for hours or days. A phishing message, a reused password, or an unreviewed sign-in prompt can give an attacker enough access to interrupt line-of-business systems, shared folders, cloud email, and backup administration. That is why business continuity and backup compliance has to include identity discipline, not just backup software.
For distribution teams and warehouse offices across Sparks and the greater Reno corridor, the impact is immediate. Dispatch boards stop updating, shipping documents cannot be retrieved, and staff begin working from memory, screenshots, or paper notes. That creates downstream errors in receiving, route changes, customer communication, and billing. In cases like Ayden’s, the lockout is only the final symptom; the real failure is that weak account hygiene allowed one bad message to move from inbox to operations floor.
- Identity exposure: Shared credentials, password reuse, and weak multifactor enrollment let a single compromised account spread risk into email, file storage, and backup consoles.
- Workflow concentration: Logistics teams often depend on a small number of shared systems for manifests, routing, proof-of-delivery records, and customer updates, so one account issue can stall multiple departments.
- Backup blind spots: If the same credentials protect production systems and backup administration, an attacker can tamper with recovery points before anyone notices.
- Local operating pressure: Fast-moving warehouse schedules in Sparks leave little room for verification, which makes fake reset notices and urgent approval prompts more effective.
Practical Remediation for Account Security and Continuity
The fix is not a single tool. It is a set of operating controls that reduce the chance that one user action can stop the business. We typically start by separating privileged accounts from daily-use accounts, enforcing phishing-resistant multifactor authentication where possible, removing password reuse through a managed password platform, and validating that backup administration is protected by separate credentials and alerting. For companies with multiple sites, shift-based staffing, or warehouse and office crossover, this work should be planned as part of broader IT strategy engagements in Northern Nevada so identity, recovery, and workflow dependencies are addressed together.
Just as important, the response process has to be rehearsed. If a dispatcher reports a suspicious sign-in, the team should know who disables sessions, who checks audit logs, who validates backup integrity, and who confirms whether file sync or mailbox rules were altered. The CISA guidance on strong passwords and account protection is a practical baseline, but businesses in logistics usually need tighter operational controls than consumer guidance alone provides.
- MFA hardening: Require multifactor authentication for email, VPN, cloud storage, and backup portals, with number matching or phishing-resistant methods where supported.
- Privileged account separation: Keep admin access out of daily email and browsing activity to reduce compromise paths.
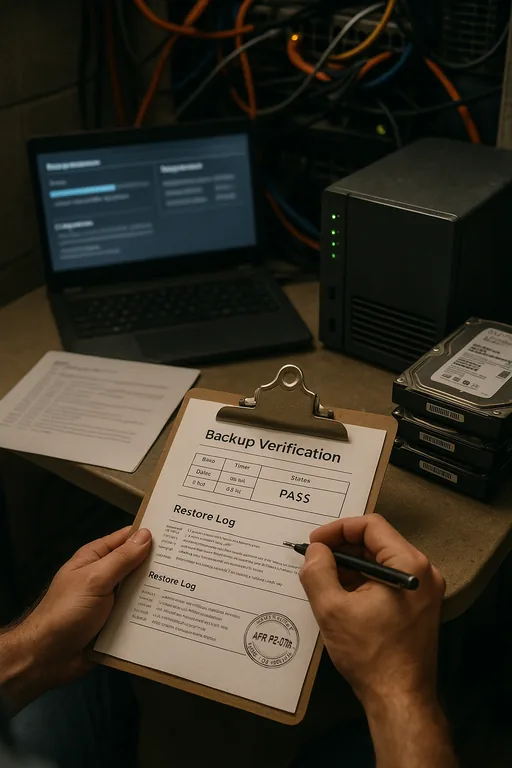
- Backup validation: Test restore points and confirm backup immutability or access separation so compromised user accounts cannot quietly damage recovery options.
- Conditional access: Block risky sign-ins by geography, device state, and impossible travel patterns.
- User reporting workflow: Give staff a fast way to report suspicious messages before they forward them internally.
Field Evidence: Warehouse Access Recovery After Credential Compromise
We worked through a similar pattern for a transportation-related operation serving the Sparks industrial area near USA Parkway traffic lanes and regional freight routes. Before remediation, the company relied on reused passwords, broad mailbox access, and a backup console tied to the same identity stack as production email. A single compromised account led to mailbox rule changes, delayed shipment communication, and uncertainty about whether recovery points had been touched.
After the environment was restructured, the business moved to separated admin accounts, enforced MFA, tested restore procedures, and added clearer escalation through IT systems for multi-location operations . The result was not just better security on paper. It reduced confusion during shift changes, shortened incident triage, and gave supervisors a cleaner path to keep dispatch and billing moving even when one account had to be isolated.
- Result: Account containment time dropped from several hours to under 30 minutes, backup verification was completed the same day, and no further shipment documentation was lost during follow-up incidents.
Reference Table: Human Element Controls for Logistics Operations
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Business Continuity And Backup Compliance and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.
Local Support in Reno and Sparks
We support businesses throughout Reno and Sparks that need practical response for account compromise, continuity planning, and recovery validation. For operations teams moving between warehouse, office, and dispatch functions, local support matters because identity incidents often affect several workflows at once. From our Reno office, the destination referenced here is a short trip, which reflects the kind of close-in operational coverage many Northern Nevada businesses expect when access problems begin to affect scheduling, billing, or backup confidence.
Operational Takeaway for Sparks Logistics Teams
When operations stop after a phishing click or account lockout, the real issue is rarely just the email itself. The deeper problem is usually weak identity control, poor separation of privileged access, and no clear process for containing a compromised user before it reaches dispatch, billing, or backup systems. In logistics environments, that gap shows up fast because so many workflows depend on a few shared platforms.
For businesses in Sparks and the surrounding Northern Nevada service area, the practical response is straightforward: tighten account hygiene, protect backup administration, rehearse incident handling, and align continuity planning with the way staff actually work. That approach reduces downtime, limits billing disruption, and makes recovery more predictable when a user-level mistake becomes an operational event.

