Reno/Sparks Hub Risk
Problems like this tend to stay hidden until something important breaks. For logistics hubs in South Meadows, that often means operations stopping, avoidable delays, or a bigger recovery burden than expected. The best response is standardizing how new users, devices, and systems are brought online.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Scalability Failures Stop Logistics Operations
The scalability ceiling shows up when a business grows faster than its IT standards. In logistics hubs around South Meadows, that usually means the network, identity controls, shared storage, wireless coverage, and application access were all built for yesterday’s headcount. Then the company adds another shift, more scanners, more dock devices, more supervisors, or another software integration, and the environment starts failing in ways that look random but are actually predictable.
We see this most often when hiring plans move ahead before infrastructure planning does. A company may have enough bandwidth on paper, but not enough switch capacity, DHCP scope, wireless density, license headroom, or documented provisioning steps. That is why disaster recovery planning and recovery in Northern Nevada is not just about restoring after a major outage. It also means identifying where growth can interrupt operations before a full stoppage occurs. In cases like Jean’s, the outage is only the visible symptom; the root cause is an environment that cannot absorb change safely.
- Identity and access sprawl: New users and devices are added inconsistently, creating permission conflicts, duplicate accounts, and failed access to warehouse, dispatch, or billing systems.
- Wireless and endpoint saturation: Additional handhelds, tablets, label printers, and workstations can overwhelm access points or expose weak segmentation between office and floor devices.
- Undersized core infrastructure: Aging switches, limited IP ranges, and flat networks often work until a hiring burst or seasonal volume increase pushes them over the edge.
- Unmanaged application dependencies: Shipping platforms, ERP tools, shared drives, and remote vendor connections may all rely on one another, so one bottleneck can stop receiving, picking, and dispatch together.
How to Remove the Ceiling Before the Next Hiring Wave
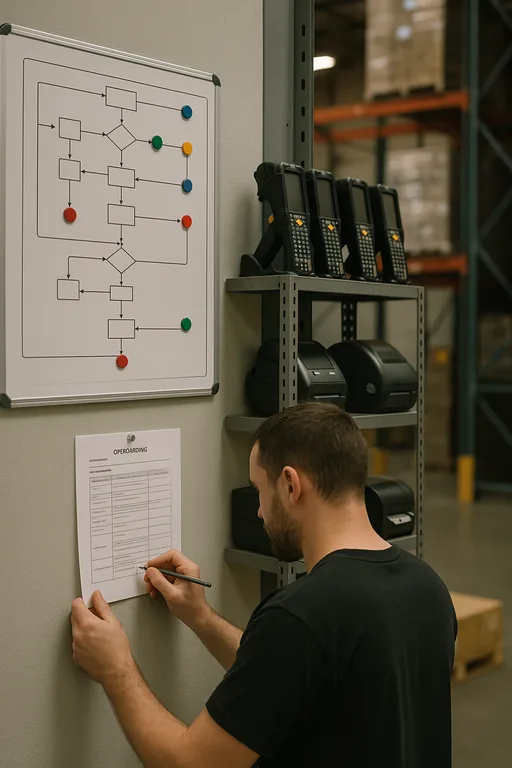
The practical fix is standardization. New users, devices, scanners, printers, and workstations should be brought online through the same documented process every time. That includes role-based account creation, preapproved device profiles, VLAN placement, license checks, wireless validation, and confirmation that backups and recovery points include the systems the new team depends on. Businesses that are expanding quickly usually benefit from compliance-focused IT management because it forces operational discipline into day-to-day changes instead of waiting for a failure.
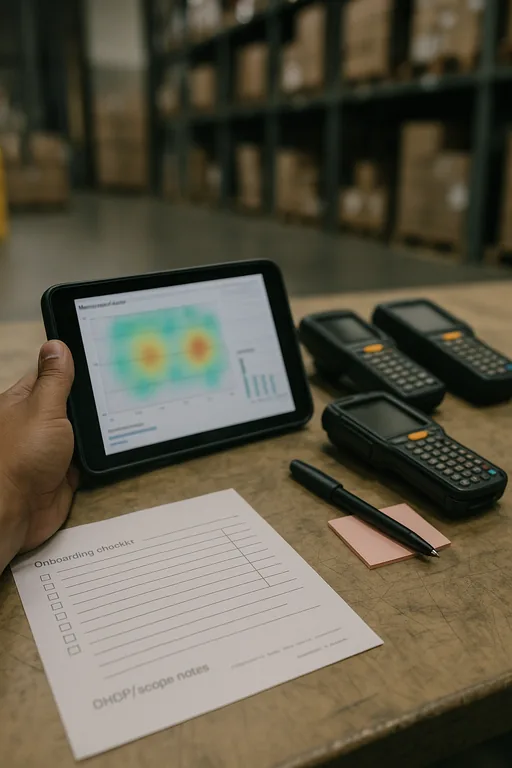
We also recommend testing capacity before the next ten hires, not after. That means reviewing switch utilization, wireless heat maps, DHCP scope, storage growth, authentication dependencies, and failover readiness. For logistics environments, the Cybersecurity and Infrastructure Security Agency provides useful operational guidance on resilience and incident preparation through CISA’s Cybersecurity Performance Goals , which align well with practical business continuity controls.
- Standardized onboarding: Build one checklist for users, endpoints, scanners, printers, and application access so every addition follows the same validated path.
- Network segmentation: Separate warehouse devices, office systems, guest access, and critical servers with VLANs to reduce broadcast noise and contain failures.
- Capacity review before expansion: Validate switch ports, wireless coverage, licensing, storage, and ISP performance before adding staff or opening another workflow lane.
- Backup validation: Confirm that file shares, ERP data, shipping records, and configuration backups can actually be restored within the business’s recovery window.
Field Evidence: Growth Pressure in a Northern Nevada Shipping Corridor
In one regional warehouse environment serving customers between South Meadows and the Sparks industrial corridor, operations were repeatedly slowing during shift changes and new employee onboarding. Before remediation, new devices were being added ad hoc, wireless coverage was uneven near loading areas, and account permissions were handled differently by each supervisor request. That created recurring lockouts, duplicate device records, and delays in outbound documentation.
After standardizing provisioning, segmenting warehouse traffic, and documenting recovery priorities, the site moved from reactive troubleshooting to controlled expansion. We also added a structured support model for future staffing increases through support for growing Reno businesses , so the next round of hiring did not create the same operational drag.
- Result: New-user setup time dropped from nearly a full day of interruptions to under 90 minutes, and unplanned access-related downtime during onboarding was reduced by more than 70 percent.
Scalability Risk Control Reference for Logistics Hubs
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Disaster Recovery Planning And Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Sparks, Reno, and Northern Nevada and Northern Nevada.
Local Support in South Meadows, Sparks, Reno, and Northern Nevada
We regularly support businesses moving between Reno, South Meadows, and the Sparks industrial corridor, where growth often happens faster than infrastructure planning. For warehouse, logistics, and distribution teams, local response matters, but so does knowing the operating pattern of the region: multi-shift staffing, industrial wireless challenges, and the need to keep receiving, inventory, and dispatch systems aligned as headcount increases.
Standardization Is What Keeps Growth from Becoming Downtime
When a logistics hub hits a scalability ceiling, the outage is rarely caused by one bad device or one isolated mistake. The real problem is that growth was allowed to outpace standards for onboarding, access, capacity, and recovery. In South Meadows and across Northern Nevada, that can stop receiving, delay dispatch, and create a larger recovery event than the business expected.
The practical takeaway is straightforward: if you plan to add people, devices, shifts, or locations, your IT environment needs to expand first. Standardized provisioning, segmented networks, validated backups, and documented recovery priorities give operations room to grow without crashing into preventable limits.

