Reno/Sparks Hub Audit
Problems like this tend to stay hidden until something important breaks. For logistics hubs in South Meadows, that often means operations stopping, avoidable delays, or a bigger recovery burden than expected. The best response is validating backups regularly and proving recovery before a real outage.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Backup Copies Alone Do Not Keep a Logistics Hub Running
The core issue is straightforward: a backup is only a copy of data, while business continuity is the ability to keep shipping, receiving, scanning, routing, and billing even when a server, storage array, or line-of-business application fails. In South Meadows logistics operations, that distinction matters because warehouse workflows are tightly timed. If dispatch cannot access order status, barcode history, or route documentation, operations stop first and diagnosis happens second.
We typically find that the real failure is not the outage itself. It is the lack of a resilience test. Teams may see green checkmarks on backup jobs and assume recovery is covered, but they have not verified boot order, application dependencies, credential access, recovery point accuracy, or how long it takes to restore a working environment. That is why businesses reviewing managed cybersecurity programs in Northern Nevada should treat recovery validation as part of security operations, not as a separate afterthought. In a corridor like South Meadows, where distribution schedules, carrier windows, and multi-shift staffing leave little room for delay, the difference between “we have backups” and “we can recover operations” is material. That was the operational gap behind Diego’s outage.
- Recovery assumption: Backup software reported successful jobs, but no recent test had confirmed that warehouse data, user permissions, and dispatch applications could be restored in the right sequence under outage conditions.
- Application dependency: Logistics systems often rely on shared storage, SQL services, mapped drives, scanners, and print services; if one layer fails during restore, the business still cannot work.
- Operational timing: A restore that takes four hours on paper may create an all-day disruption once receiving queues, outbound schedules, and billing cutoffs are affected.
- Local infrastructure reality: In Reno and South Meadows, multi-building layouts, older industrial spaces, and mixed carrier environments can complicate failover and remote access during an incident.
How to Turn Backup Into Real Business Continuity
The practical fix is to move from passive backup retention to active recovery validation. That means defining recovery objectives for each critical system, testing restores on a schedule, documenting dependency order, and confirming that staff can continue core functions during a server, storage, or ransomware event. For logistics hubs, this usually includes dispatch platforms, shared file repositories, label printing, scanner connectivity, ERP or WMS databases, and remote access for supervisors and accounting.
We recommend building these controls into a documented continuity process rather than treating them as one-off technical tasks. A structured approach to business continuity and backup compliance helps leadership verify not only that data exists, but that operations can resume within an acceptable window. The CISA ransomware resilience guidance is useful here because it emphasizes tested backups, recovery planning, and role clarity during disruption.
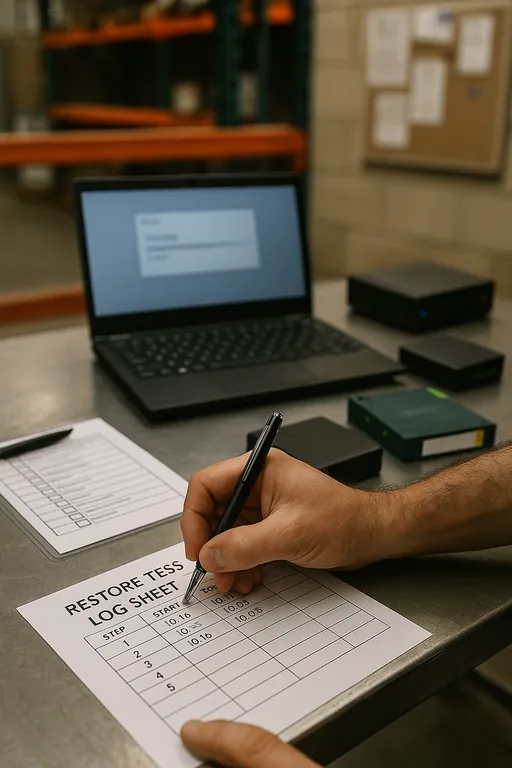
- Recovery testing cadence: Run scheduled restore tests for critical systems, not just backup job reviews, and record actual recovery time against business expectations.
- Tiered recovery design: Separate mission-critical logistics systems from lower-priority file archives so dispatch and receiving functions come back first.
- Immutable and off-site copies: Maintain protected backup sets that cannot be altered by malware or accidental deletion.
- Credential and access validation: Confirm that admin accounts, MFA methods, service accounts, and licensing all work during a recovery event.
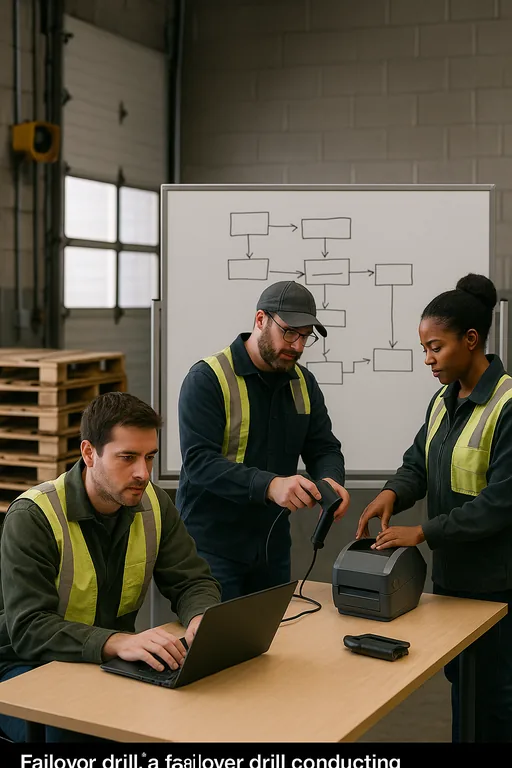
- Failover workflow: Document how staff continue shipping, receiving, and billing if the primary server environment is unavailable.
Field Evidence: Resilience Testing in a High-Throughput Reno Warehouse Corridor
In one Northern Nevada warehouse environment, the initial condition looked acceptable on paper: backup jobs completed nightly, storage utilization was monitored, and the IT team believed recovery was covered. The first live restore exercise showed otherwise. The database restored, but scanner shares did not remap correctly, print queues failed, and user groups tied to shipping supervisors were incomplete. The result was a system that was technically online but still not usable for operations.
After remediation, the environment was rebuilt around tested recovery order, documented dependencies, and isolated backup copies. The team also added quarterly validation using backup and recovery programs for operational continuity so restores were measured against actual warehouse tasks rather than software status alone. In a Reno industrial setting where morning freight windows and afternoon billing batches both matter, that change reduced uncertainty and gave managers a realistic recovery path instead of assumptions.
- Result: Verified recovery time for core dispatch and file access dropped from an unproven multi-hour estimate to a tested 58-minute restoration window for priority systems.
Resilience Test Audit Reference Points for Logistics Operations
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.
Local Support in Reno and Northern Nevada
From our Reno office, we regularly support warehouse, transportation, and multi-site operations that need practical recovery planning rather than assumptions. The route to the Clearacre area is short, but the larger value is knowing the local infrastructure, business pace, and operational dependencies that affect how quickly a logistics environment can actually recover.
The Operational Takeaway
If a logistics hub in South Meadows has never tested recovery under realistic conditions, it does not yet know whether it can keep working during a serious outage. That is the central issue behind resilience testing. Backup status alone does not confirm that dispatch, file access, printing, user permissions, and billing can be restored in the order the business actually needs.
The practical answer is disciplined validation: test restores, document dependencies, measure recovery time, and align technical controls with how the warehouse runs day to day. That approach reduces downtime, limits rework, and gives leadership a recovery plan based on evidence instead of assumptions.

