Reno/Sparks Hub Fix
Problems like this tend to stay hidden until something important breaks. For logistics hubs in South Meadows, that often means operations stopping, avoidable delays, or a bigger recovery burden than expected. The best response is reviewing controls, access, and recovery steps before they are tested under pressure.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Compliance Gaps Stop Logistics Operations
When operations stop at a logistics hub, the visible outage is usually only the last symptom. The deeper problem is often a compliance gap: policies say one thing, actual permissions and device controls say another, and no one notices until a workflow depends on them. In South Meadows and across Reno-area warehouse and distribution environments, we commonly see this happen when regulations such as CMMC, HIPAA, customer security requirements, or internal audit standards change faster than the business can document and enforce them.
That gap matters because logistics operations depend on tightly connected systems. Shipping stations, shared folders, line-of-business applications, handheld devices, label printers, vendor portals, and remote access tools all rely on consistent identity and access rules. If those rules are outdated, a cleanup effort or audit response can remove access too broadly, or leave risky access in place for too long. Businesses dealing with that kind of drift often need structured IT support and help desk coverage in Reno so user changes, permissions, and incident response are handled in a controlled way instead of reactively. In cases like Jodi’s, the outage is not caused by one bad click. It is caused by months of undocumented exceptions, inherited permissions, and recovery steps that were never tested against actual operations.
- Access governance drift: User roles, shared credentials, and inherited permissions no longer match current job duties, creating both compliance exposure and sudden lockouts during cleanup.
- Documentation lag: Regulatory requirements and customer controls change faster than internal IT notes, SOPs, and approval records are updated.
- Operational dependency concentration: A small number of workstations, shared drives, or admin accounts often support receiving, dispatch, billing, and reporting at the same time.
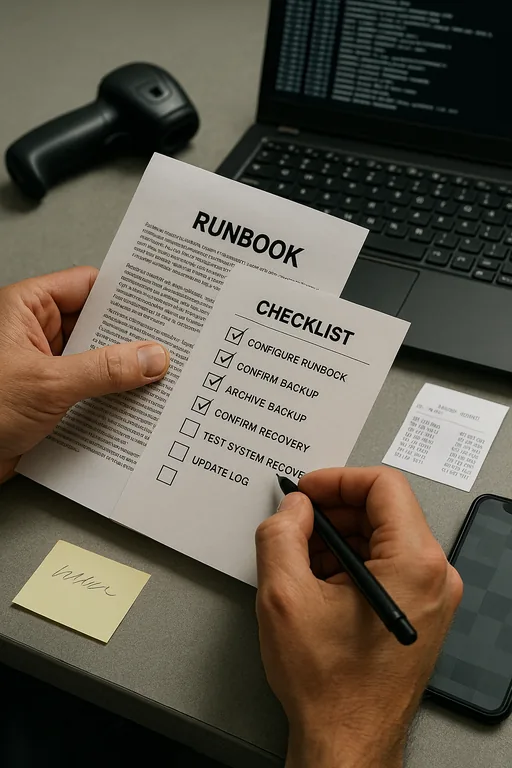
- Recovery blind spots: Teams may have backups, but not validated restore steps for permissions, application access, or device-specific workflows.
Practical Remediation for Access, Controls, and Recovery
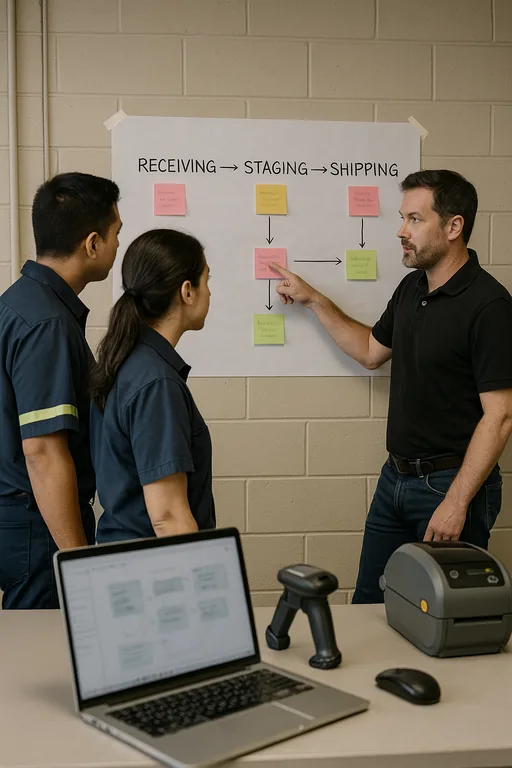
The fix is not just restoring access and moving on. We typically start by mapping the operational workflow first: receiving, staging, shipping, billing, vendor communication, and reporting. Then we align user roles, endpoint policies, and recovery procedures to those workflows. That means removing shared accounts, tightening group membership, documenting approval paths, and validating which systems are actually in scope for compliance obligations. For warehouse and dispatch environments, this also includes checking how handhelds, kiosk PCs, and shipping stations authenticate after password changes or policy updates.
From there, the remediation should include monitored endpoint standards, alerting, and policy enforcement so the same drift does not return six months later. That is where proactive endpoint management for regulated operations becomes important. Device health, patching, local admin control, encryption status, and EDR visibility need to be reviewed as part of the same control set. For a practical external benchmark, the CISA guidance on secure access and protective controls is useful because it translates security expectations into actions businesses can actually implement.
- Role-based access review: Rebuild permissions around current job functions, not legacy exceptions or shared credentials.
- MFA hardening: Require multifactor authentication for admin access, remote access, and sensitive business applications.
- Endpoint control: Standardize workstation policies for warehouse PCs, dispatch terminals, and mobile devices with EDR and patch compliance.
- Backup validation: Test restores for file access, application permissions, and operational data, not just raw backup completion.
- Change documentation: Tie policy changes to approvals, affected systems, and rollback steps so audits and recovery are both manageable.
Field Evidence: Restoring Throughput After Access Control Drift
We have seen this pattern in Northern Nevada operations corridors where warehouse teams depend on a mix of office systems and floor devices, especially in facilities serving Reno, Sparks, and North Valleys routes. Before remediation, the common pattern is broad access, inconsistent device standards, and no clean record of which controls support which compliance requirement. That creates a fragile environment where one policy change can interrupt shipping, receiving, or billing all at once.
After a structured review, the environment usually becomes much more stable. Permissions are narrowed by role, critical devices are brought under consistent monitoring, and restore procedures are documented against actual workflows. In one comparable case, a distribution operation reduced access-related tickets by 43 percent over the next quarter and cut user restoration time from several hours to under 30 minutes. Longer term, businesses benefit from clearer oversight through IT systems for multi-location operations , especially when compliance, dispatch, and accounting functions overlap across sites and carriers. Winter weather delays, carrier schedule compression, and end-of-month billing cycles all make that operational discipline more important in Northern Nevada than many teams expect.
- Result: Faster access restoration, fewer recurring permission errors, and measurable reduction in downtime during policy or staffing changes.
Compliance Control Reference for Logistics IT Environments
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in It Support And Help Desk and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, and Northern Nevada and Northern Nevada.
Local Support in South Meadows, Reno, Sparks, and Northern Nevada
Our team supports businesses throughout Reno and the surrounding logistics corridors, including facilities that coordinate between South Meadows, North Valleys, Sparks, and regional carrier routes. For operations with compliance pressure, distance is only part of the equation. What matters more is having documented controls, clear escalation paths, and recovery procedures that match the way the site actually ships, receives, and bills work.
Closing the Gap Before the Next Operational Stop
A compliance gap becomes an operations problem when access, documentation, and recovery controls no longer match the way the business actually works. In logistics environments, that mismatch shows up fast: delayed loads, stalled billing, locked-out users, and avoidable confusion during what should have been a routine change.
The practical takeaway is straightforward. Review permissions against job roles, validate endpoint standards, document control changes, and test recovery steps against real workflows. For South Meadows and greater Reno operations, that work is usually less expensive than one day of disruption and far easier than rebuilding trust after an audit failure or preventable outage.

