Reno/Sparks Hub Audit
This kind of issue rarely appears all at once. For logistics hubs in Northern Nevada, it usually builds through phishing clicks, password reuse, and weak account hygiene and then surfaces as operations stopping, slower recovery, or higher exposure. A more reliable setup starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Human Error Stops Logistics Operations Faster Than Most Hardware Failures
The main question here is straightforward: how does the human element stop a logistics hub? In practice, it happens when a single user action opens the door to account compromise, then weak identity controls allow that problem to spread into dispatch, inventory, billing, and vendor communication. In Northern Nevada logistics environments, that chain reaction is common because operations depend on shared systems, fast shift changes, mobile access, and constant email traffic from carriers, brokers, and customers.
The discussion context is accurate: the biggest security hole is often not a software flaw but an employee clicking a fake reset link. Once credentials are exposed, attackers do not need to break the firewall first. They log in as a valid user, move through cloud apps, and exploit poor password discipline, stale accounts, and weak multifactor enforcement. Businesses trying to maintain audit readiness and reporting consistency usually need tighter regulatory compliance support in Northern Nevada because these incidents rarely stay isolated; they affect access logs, data handling, retention practices, and incident documentation. We often see the same pattern in Reno and Sparks facilities where a phishing event looks minor at first, then turns into shipment delays, missed scans, and after-the-fact cleanup. That is why Nayara’s situation is less about one bad click and more about the controls that failed before and after it.
- Identity hygiene: Password reuse across dispatch, Microsoft 365, and line-of-business systems allows one compromised account to create wider operational disruption.
- Email trust gaps: Staff handling frequent vendor messages are more likely to engage with fake reset notices, invoice prompts, or file-share requests that look routine.
- Shared workstation exposure: Warehouse and shipping stations often stay signed in too long, making lateral access easier after one account is compromised.
- Compliance drift: Weak account lifecycle management creates audit gaps around access reviews, privileged use, and incident traceability.
Practical Remediation for Identity Risk, Recovery Speed, and Audit Readiness
The fix is not a single training session. It is a layered operating model that reduces the chance of a bad click becoming a business outage. We typically start by hardening identity controls: enforce phishing-resistant multifactor authentication where possible, remove shared credentials, tighten conditional access, disable legacy authentication, and review mailbox forwarding and sign-in anomalies. For logistics organizations with mixed on-premise and cloud dependencies, this work is more effective when paired with structured server and hybrid infrastructure management so authentication, file access, and line-of-business applications are governed together instead of in silos.
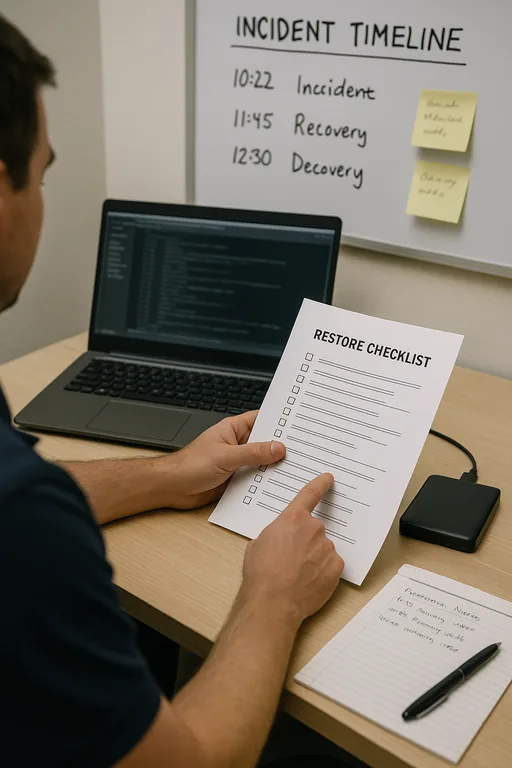
Recovery also depends on validation, not assumptions. That means tested backups for critical systems, documented account lockout and restoration procedures, alerting tied to impossible travel or suspicious sign-ins, and role-based access reviews on a schedule. For user-facing controls, the most practical standard remains to train people on current phishing tactics and reinforce reporting behavior with short, repeatable exercises. The CISA guidance on strong passwords and account protection is useful because it aligns with what actually reduces credential abuse in day-to-day operations.
- MFA hardening: Require multifactor authentication for email, remote access, cloud apps, and privileged accounts, with stronger methods than SMS where feasible.
- Account separation: Eliminate shared logins and assign named access for dispatch, billing, warehouse, and admin functions.
- Conditional access: Restrict sign-ins by geography, device state, and risk signals to reduce unauthorized access from stolen credentials.
- Backup validation: Test restoration of shipment records, file shares, and billing data on a routine schedule instead of assuming backups are usable.
Field Evidence: Credential Abuse in a Multi-Shift Shipping Environment
We worked through a similar pattern for a Northern Nevada operation serving routes between Reno, Sparks, and Carson-area customers. Before remediation, the site relied on reused passwords, broad mailbox access, and loosely controlled warehouse terminals. A phishing event led to account lockouts, delayed proof-of-delivery updates, and manual dispatch workarounds during a busy shipping window. After identity cleanup, access reviews, and cloud policy tightening, the organization had clearer sign-in visibility and a much smaller blast radius when suspicious activity appeared.
One important improvement came from tightening Microsoft 365 controls and standardizing permissions across shared workflows. That kind of stability is easier to maintain with disciplined cloud and Microsoft environment management , especially when logistics teams depend on email, Teams, file sharing, and mobile access across office and warehouse roles.
- Result: Phishing-related account incidents dropped, recovery steps were documented, and dispatch disruption was reduced from several hours of manual work to under 35 minutes of contained response.
Human Element Audit Reference Points for Logistics Hubs
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Regulatory Compliance Support and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno, Sparks, Carson City, and Northern Nevada
Our office on Ryland Street is only a short drive from the VA Medical Center District, which matters when a logistics team is dealing with locked accounts, stalled dispatch activity, or urgent access review work. For Reno-area operations, local response is not just about travel time. It helps when the support team understands how warehouse workflows, billing cutoffs, and compliance obligations intersect across Northern Nevada businesses.
Operational Takeaway for Northern Nevada Logistics Teams
When operations stop after a phishing click or password reuse event, the real issue is usually weak identity discipline across the environment. Logistics hubs depend on fast access, shared workflows, and reliable communication, so even a small lapse in account hygiene can interrupt dispatch, billing, and reporting. The right response is to treat user behavior, access control, and recovery planning as one operational system.
For Northern Nevada organizations, that means reducing shared credentials, validating recovery steps, tightening cloud access, and making security habits part of normal warehouse and office routines. Done properly, the result is not just fewer incidents. It is faster containment, cleaner audits, and less disruption when something does go wrong.

