Reno Financial IT Recovery
What looks like a one-off issue is often tied to hidden threats. In financial office environments, stolen credentials, MFA gaps, and weak monitoring can turn into ransomware, fraud, and data loss long before anyone notices the warning signs. Closing those gaps early makes business IT operations management far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Hidden Credential Abuse Causes Financial Office Network Failures
The invisible threat in a financial office is often not a noisy intrusion. It is a valid login used at the wrong time, from the wrong device, or with the wrong behavior pattern. Modern attackers do not need to break through a perimeter if they can sign in with stolen credentials. In Washoe County, we regularly see firms assume a network crash started with internet instability, a bad switch, or a server issue, when the actual trigger was unauthorized account use that spread into file access, mailbox compromise, or ransomware staging.
That distinction matters because the response is different. If the root cause is identity compromise, replacing hardware alone will not solve it. Financial offices depend on predictable access to client records, tax documents, custodial platforms, and secure communications. Once a compromised account starts moving laterally, the business impact can look like random slowness, lockouts, sync failures, or corrupted shares. That is why structured business IT operations management in Northern Nevada has to include identity visibility, endpoint oversight, and escalation paths, not just basic uptime checks. In cases like Angel’s, the first symptom is rarely the first event.
- Credential misuse: A stolen username and password can appear legitimate inside Microsoft 365, VPN, remote desktop, or cloud file systems, allowing an attacker to operate quietly before encryption, fraud, or data theft becomes obvious.
- MFA gaps: Partial MFA deployment, weak push approvals, or legacy accounts without modern controls leave financial systems exposed even when staff believe multifactor protection is already in place.
- Weak monitoring: Without alerting on impossible travel, unusual sign-in patterns, privilege changes, or mass file activity, suspicious behavior blends into normal office traffic.
- Operational fallout: Client service slows first, then billing, reporting, document retrieval, and compliance workflows begin to fail in sequence.
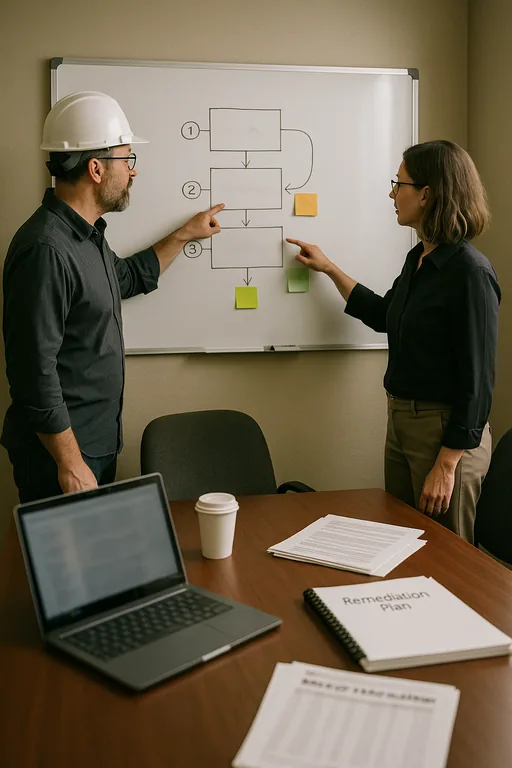
Practical Remediation for Credential-Driven Network Instability
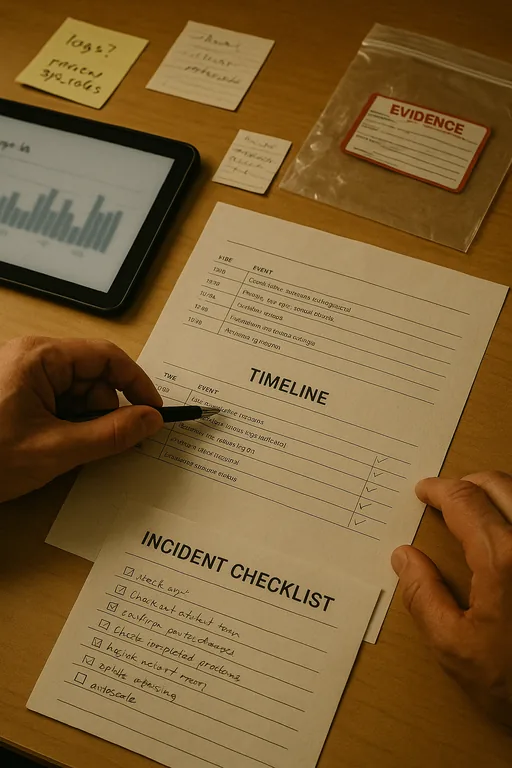
The fix starts with containment, then moves into control hardening. We typically isolate affected endpoints, revoke active sessions, reset privileged credentials, review mailbox and file access logs, and verify whether persistence was established through forwarding rules, remote tools, or unauthorized admin changes. In a financial office, that work has to happen carefully so evidence is preserved while core operations are restored in a controlled order.
After containment, the environment needs stronger detection and response. That includes enforced MFA for every user and admin account, conditional access policies, endpoint detection and response, tested backup integrity, and alerting tied to suspicious sign-in behavior. Firms that need better visibility into these events usually benefit from security monitoring and response for Washoe County operations , especially when internal staff do not have time to review logs continuously. For practical guidance on reducing credential abuse and ransomware exposure, the CISA StopRansomware resource center is a useful operational reference.
- Identity lockdown: Reset compromised accounts, remove stale admin rights, enforce phishing-resistant MFA where possible, and disable legacy authentication.
- Endpoint control: Deploy or tune EDR to detect unusual process execution, credential dumping, and ransomware behavior before encryption spreads.
- Backup validation: Confirm restore points are recent, isolated, and actually recoverable before declaring the environment stable.
- Network segmentation: Separate user devices, servers, and sensitive financial systems so one compromised account cannot move freely across the office.
- Alerting improvements: Trigger review on impossible travel, mass file changes, mailbox rule creation, and after-hours administrative activity.
Field Evidence: Credential Abuse Hidden Behind a “Network Outage”
We worked through a similar pattern for a professional office corridor in Reno where staff initially reported intermittent file access failures and unstable remote sessions. The first assumption was ISP trouble or aging network hardware. Log review showed a different story: a reused password had allowed repeated sign-ins from outside Nevada, followed by mailbox rule changes and abnormal access to shared storage. Because the office relied on time-sensitive document handling, the disruption showed up as workflow delay before it showed up as a security incident.
After account containment, MFA enforcement, endpoint review, and backup verification, the office returned to stable operations with clearer visibility into abnormal behavior. For firms that want broader protection against this kind of quiet compromise, a layered approach such as managed cybersecurity programs for growing Reno businesses helps close the gap between basic IT support and active risk control, especially in multi-user financial environments.
- Result: Sign-in anomalies were blocked, file access stabilized, and the office reduced recovery time from nearly a full business day to under two hours for future account-related incidents.
Reference Points for Hidden Threat Remediation in Financial Offices
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Business It Operations Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.
Local Support in Washoe County
Financial offices in Reno, Sparks, and the broader Washoe County area often need fast response that is close enough to be practical but disciplined enough to address the real cause of an outage. From our Reno office, the Kietzke corridor is a short drive, which helps when onsite validation, endpoint isolation, or recovery coordination is needed after a credential-driven incident.
Operational Takeaway for Financial Offices in Washoe County
When a financial office reports a network crash, the visible outage is not always the real problem. Hidden identity abuse, incomplete MFA, and weak monitoring can sit underneath normal-looking activity until file access, billing, reporting, or client communication starts to fail. The earlier those gaps are identified, the lower the recovery cost and the lower the chance of a larger business interruption.
For firms in Washoe County, the practical approach is straightforward: verify the cause, contain compromised access, restore from known-good systems, and tighten the controls that allowed the issue to stay invisible. That is how business operations become more stable, not just temporarily restored.

