Reno Network Crash
This kind of issue rarely appears all at once. For financial offices in Northern Nevada, it usually builds through unclear ownership, overlapping tools, and fragmented support and then surfaces as a network crash, slower recovery, or higher exposure. A more reliable setup starts with clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Vendor Chaos Turns Into a Network Crash
For financial offices, a network crash tied to vendor confusion is usually not a single hardware failure. It is a coordination failure. One provider manages the circuit, another touches the firewall, a software vendor blames latency, and the phone vendor reports no issue on their side. Meanwhile, the office manager is left trying to translate technical updates between companies that do not share the same priorities, tools, or escalation process.
We see this across Reno, Sparks, and Carson City when firms add systems over time without assigning clear ownership. A compliance-sensitive office may have cloud applications, local printers, encrypted file shares, VoIP, scanners, and line-of-business software all depending on the same network path. If no one is accountable for the full stack, recovery slows down and audit exposure increases. That is why firms dealing with recurring outages often need compliance and risk management in Northern Nevada tied directly to operational accountability, not just technical patchwork. In cases like Eden’s, the visible outage is only the final symptom.
- Fragmented ownership: Internet, firewall, voice, workstation, and application support are handled by separate vendors, so root cause analysis stalls while each party checks only its own boundary.
- Overlapping tools: Multiple remote access agents, security products, or monitoring platforms can create blind spots and conflicting alerts that slow triage.
- Compliance pressure: Financial offices cannot treat downtime as a simple inconvenience because delayed access to records, reporting, and client communications can affect retention, supervision, and risk controls.
- Escalation gaps: When there is no documented incident owner, staff lose time repeating the same issue to different vendors instead of restoring service.
How to Restore Control and Reduce Repeat Failures
The fix is not adding another vendor. The fix is establishing one accountable operating model. That starts with documenting every dependency: carrier, firewall, switch stack, wireless, voice platform, endpoint management, cloud applications, backup path, and who has authority to make changes. Financial firms benefit when this is handled through structured IT strategy engagements in Northern Nevada so technical decisions, compliance requirements, and business continuity are aligned before the next outage.
From there, we typically standardize escalation paths, remove duplicate tooling, and define what must be checked first during an incident. That includes internet failover, firewall logs, DNS resolution, switch health, endpoint reachability, and application authentication. For firms handling regulated data, controls should also map to practical guidance such as the CISA ransomware and resilience guidance , because weak ownership and poor recovery discipline often show up in both outage response and security response.
- Single incident owner: Assign one technical lead to coordinate all vendors, approve changes, and keep the office from becoming the message relay.
- Network baseline: Document firewall rules, WAN circuits, VLANs, switch uplinks, and ISP demarcation so troubleshooting starts with facts instead of assumptions.
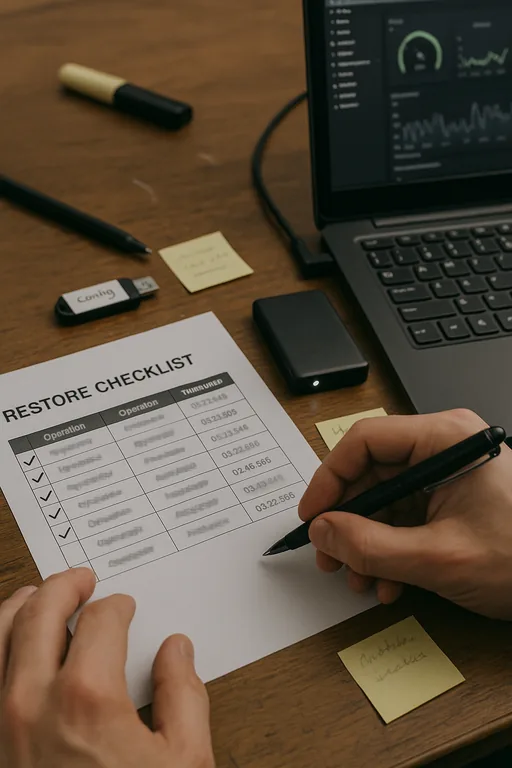
- Backup validation: Test file recovery, configuration backups, and cloud data access on a schedule rather than assuming backups will work during an outage.
- MFA and access review: Tighten administrative access so emergency changes do not create new compliance or security problems during recovery.
Field Evidence: Stabilizing a Multi-Vendor Financial Office
In one Northern Nevada financial office corridor, the environment had grown around separate internet, copier, phone, and software relationships over several years. Before cleanup, every outage triggered a chain of forwarded emails, duplicate tickets, and delayed callbacks. After consolidating documentation, defining escalation ownership, and adding clearer operational oversight through IT systems for multi-location operations , the office moved from reactive vendor chasing to a controlled response process.
The practical difference was immediate. Instead of waiting half a day for vendors to compare notes, the office had a current network diagram, known support contacts, a tested restart sequence, and a clear decision-maker. In a region where weather, downtown building constraints, and mixed carrier availability can complicate service restoration, that discipline matters more than another software subscription.
- Result: Incident response time dropped from roughly 4 hours of unmanaged escalation to under 45 minutes for initial containment, with fewer repeat outages over the following quarter.
Reference Table: Common Failure Points in Vendor-Managed Financial Networks
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Compliance And Risk Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Northern Nevada and Northern Nevada.

Local Support in Northern Nevada
Reno Computer Services supports financial offices across Reno and the surrounding Northern Nevada market, including downtown locations where multiple vendors, older building infrastructure, and shared carrier dependencies can complicate outage response. The route below reflects the short drive from our Ryland Street office to the Virginia Street Opportunity Zone area, where fast local coordination can matter when a network issue affects billing, records access, or client scheduling.
Clear Ownership Prevents Expensive Downtime
A network crash in a financial office is often the visible result of a deeper management problem: too many vendors, too little accountability, and no single response path when systems fail. In Northern Nevada, where firms depend on stable connectivity, secure records access, and timely client communication, that gap can quickly affect both operations and compliance posture.
The practical takeaway is straightforward. Document ownership, simplify the toolset, define escalation rules, and test recovery before the next outage. When those controls are in place, incidents become shorter, decisions become clearer, and the office is no longer dependent on vendor finger-pointing to restore service.

