Truckee Login Risk
When a business is dealing with login failures, the failure usually started earlier. Unclear ownership, overlapping tools, and fragmented support can weaken endpoint and threat protection over time and leave dental offices in The Truckee Meadows exposed when pressure hits. Addressing the problem means clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Vendor Chaos Turns Into Login Failure
For most dental offices in The Truckee Meadows, login trouble is not just a password problem. It is usually a control problem. We see this when one vendor manages the firewall, another touches workstations, a software company controls the practice platform, and nobody owns the full authentication path from endpoint to cloud application. The result is fragmented endpoint policy, inconsistent updates, and delayed response when access starts failing. That is why many practices stabilize faster when they put endpoint and threat protection in Northern Nevada under clearer operational ownership.
The vendor chaos issue is especially common in smaller healthcare offices where the office manager is expected to coordinate internet, phones, software, printers, scanners, and workstations while also keeping patients moving. In that environment, a login failure can start with an expired certificate, a disabled sync service, a broken security agent, or a misapplied conditional access rule. By the time staff notice, the real damage is operational: hygiene schedules back up, treatment plans wait, claims are delayed, and front-desk confidence drops. In cases like Addison’s, the visible symptom is a lockout, but the root cause is usually unclear accountability across too many support parties.
- Technical factor: Overlapping vendor responsibility can break the chain between identity management, endpoint security, and line-of-business application access, leaving no single team responsible for diagnosis or escalation.
- Operational detail: Dental offices often rely on tightly timed workflows for imaging, charting, e-prescribing, and billing, so even a short authentication outage can affect the full day’s schedule.
- Local reality: Across Reno, Sparks, and the broader Truckee Meadows, multi-vendor support delays are amplified when onsite dispatch, remote access permissions, and after-hours escalation are not documented in advance.
How To Fix The Ownership Gap Before It Becomes Downtime
The practical fix is not adding more vendors. It is reducing ambiguity. A dental office needs one documented escalation path, one current asset and access inventory, and one accountable process for endpoint policy, identity controls, and vendor coordination. In practice, that means confirming who owns Microsoft 365 authentication, who manages endpoint agents, who approves software changes, and who validates that security tools are not blocking legitimate clinical workflows. Offices that need this level of coordination often benefit from IT consulting in Northern Nevada to define responsibility before the next outage forces the issue.
From a technical standpoint, remediation usually includes reviewing endpoint detection settings, validating directory sync and MFA behavior, checking DNS and certificate dependencies, and testing backup access methods for critical staff. For healthcare environments, it is also worth aligning controls with practical guidance from CISA’s ransomware and resilience guidance , because the same weak ownership model that causes login failures often leaves backup validation, alerting, and incident response underdeveloped.
- Control step: Assign a single operational owner for identity, endpoint security, and vendor escalation.
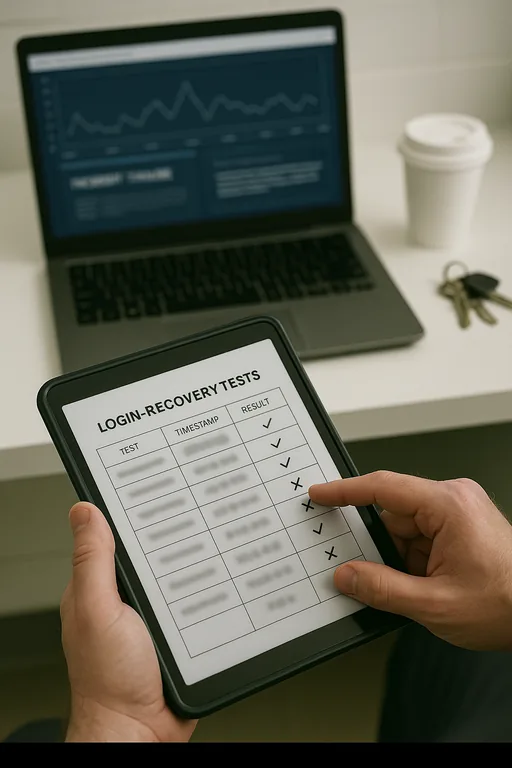
- Practical action: Document application dependencies, enforce MFA hardening, validate EDR policy exceptions, and test login recovery procedures for front-desk, clinical, and billing roles.
- Control step: Standardize escalation windows and contact paths.
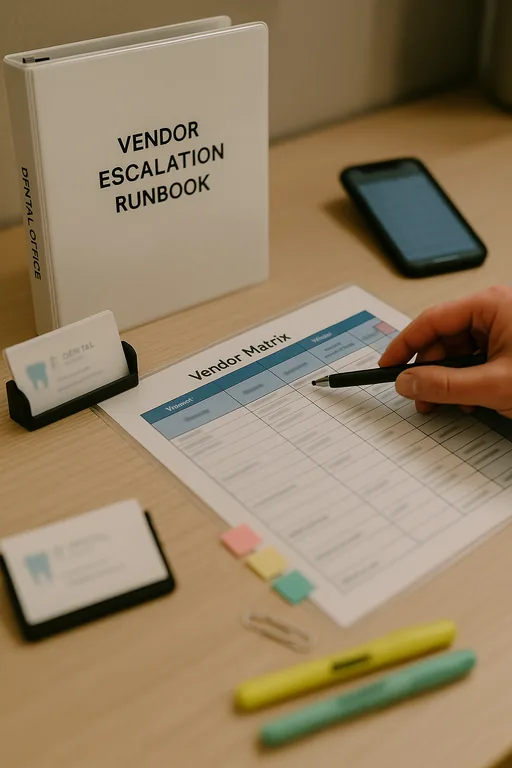
- Practical action: Keep a current vendor matrix with after-hours contacts, admin access boundaries, and approval authority so support does not stall during patient hours.
Field Evidence: Multi-Vendor Access Recovery In A Busy Reno Practice Corridor
We worked through a similar pattern for a healthcare office operating between central Reno and South Meadows where recurring login complaints had been treated as isolated user issues for months. Before remediation, the office had separate support contacts for internet, phones, Microsoft 365, endpoint security, and practice software. Tickets bounced between providers, workstation policies drifted, and no one was validating whether security controls were interfering with legitimate application access.
After consolidating escalation ownership, cleaning up endpoint policy conflicts, and putting strategic IT leadership for multi-vendor operations around the environment, the office moved from reactive troubleshooting to a documented response model. That included tested fallback accounts, clearer vendor boundaries, and a single incident path for authentication failures during patient hours. In Northern Nevada, where weather, staffing gaps, and cross-town dispatch can all slow response, that structure matters.
- Result: Repeated login-related interruptions dropped from several incidents per month to isolated exceptions, and the office cut average access recovery time from most of a morning to under 30 minutes.
Reference Table: Where Dental Login Risk Usually Starts
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Endpoint And Threat Protection and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.
Local Support in The Truckee Meadows
From our Reno office, we regularly support businesses across the Truckee Meadows, including dental and healthcare locations that need fast coordination between software vendors, internet providers, workstation support, and security controls. For offices near Arrowcreek and South Reno, response planning matters because even a short delay can affect patient flow, billing, and end-of-day reconciliation.
Clean Ownership Reduces Login Risk
Dental office login failures in The Truckee Meadows are often the final symptom of a longer vendor-management problem. When endpoint security, identity controls, software support, and network changes are split across too many parties without a clear owner, response slows down and routine access issues become operational outages.
The practical takeaway is straightforward: define ownership, document escalation, and regularly test how staff regain access when a critical system fails. That approach protects scheduling, billing, patient communication, and the security controls that are supposed to support the business rather than interrupt it.

