Reno/Sparks Dental
When a business is dealing with login failures, the failure usually started earlier. Poor safeguards, inconsistent records handling, and a slow response can weaken proactive device and endpoint management over time and leave dental offices in The Truckee Meadows exposed when pressure hits. Addressing the problem means documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Login Failures Become a Legal Liability
For dental offices in The Truckee Meadows, a login failure is rarely just a password problem. In most cases, we find a control gap behind it: stale user accounts, undocumented role changes, inconsistent device enrollment, missing audit trails, or weak escalation procedures when staff cannot access practice management systems. That is where the legal liability issue starts. If patient data is mishandled during a disruption, “I didn’t know” is not a useful defense in a Reno court, especially when the business had prior warning signs such as repeated lockouts, shared credentials, or unmanaged workstations.
Problems like this also erode day-to-day reliability. A dental office may still be seeing patients, but if front-desk systems, imaging workstations, or billing terminals are not governed consistently, the organization is operating on borrowed time. That is why structured proactive device and endpoint management in Reno matters. It closes the gap between basic access and defensible access by tying users, devices, permissions, and response records together. In Iria’s case, the visible symptom was a lockout, but the real issue was that account changes and endpoint controls had drifted apart from documented office process.
- Identity control drift: User permissions often change faster than documentation, especially in busy dental offices where front-desk, billing, and clinical roles overlap during staff absences.
- Endpoint inconsistency: A workstation that misses policy updates, security baselines, or credential cache corrections can trigger repeated login failures even when the directory itself is healthy.
- Records handling exposure: When staff revert to paper notes, personal devices, or verbal workarounds during access failures, protected information becomes harder to track and defend.
- Slow incident response: Delayed triage turns a 15-minute access issue into hours of downtime, rescheduling, and billing backlog across the office.
Practical Remediation for Access Control and Recovery
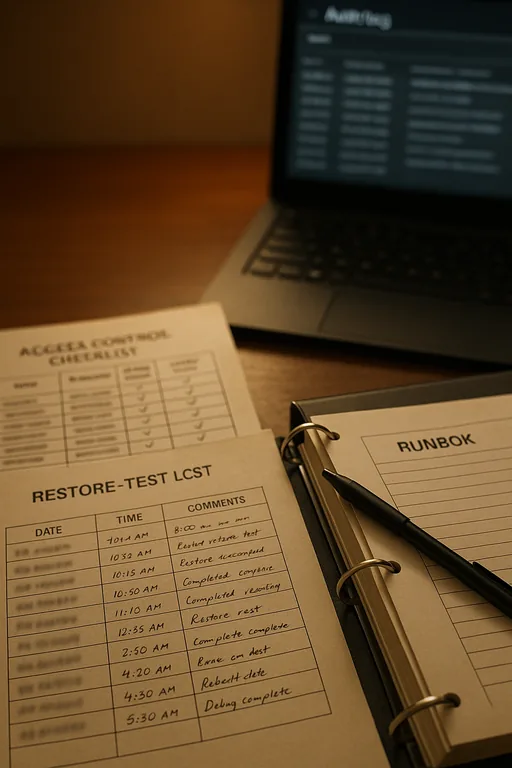
The fix is not just resetting passwords faster. Dental practices need a repeatable access-control process tied to endpoint oversight, documented onboarding and offboarding, and a tested response path for account failures. We typically start by reviewing identity sources, workstation policy compliance, local admin exposure, MFA enforcement, and whether the practice can still operate safely if a line-of-business system becomes unavailable. That includes validating who can approve access changes, how those changes are recorded, and whether the office can restore normal operations without improvising around patient data.
Recovery planning matters just as much as prevention. Offices that build disaster recovery planning for dental operations are better positioned to restore access, verify data integrity, and keep billing and scheduling moving during a disruption. For healthcare-adjacent environments handling protected information, the HHS HIPAA Security Rule guidance is a practical reference for access management, audit controls, and contingency planning.
- Access review: Reconcile every active user, role, and device against current job function and remove shared or unnecessary credentials.
- MFA hardening: Enforce multifactor authentication for email, remote access, and administrative actions that can affect patient systems.
- Endpoint policy enforcement: Standardize workstation baselines, patching, EDR coverage, and login policy application across front-desk and clinical devices.
- Backup validation: Confirm that practice data, configuration records, and authentication-dependent systems can be restored in a usable sequence.
- Response workflow: Define who triages lockouts, who approves emergency access, and how every exception is documented for later review.
Field Evidence: Restoring Access Without Expanding Exposure
We have seen this pattern in Reno and Sparks corridor practices where older tenant configurations, rapid staffing changes, and mixed workstation ages create hidden access problems. Before remediation, the office was relying on informal account changes, inconsistent endpoint status, and manual fallback steps that increased both downtime and records risk. After cleanup, the environment had a documented access matrix, enforced endpoint standards, and tested fallback procedures for scheduling and billing.
One practical improvement was aligning continuity planning with daily workflow instead of treating backup as a separate project. That is where compliance-focused backup continuity controls make a difference. In Northern Nevada, where multi-site coordination and vendor response times can vary, that structure reduces confusion when a practice is already under pressure.
- Result: Login-related downtime dropped from repeated multi-hour disruptions to under 25 minutes per incident, with cleaner audit records and faster restoration of scheduling and claims processing.
Access Control and Liability Reference Points for Dental Offices
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Proactive Device And Endpoint Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
Our office on Ryland Street is positioned to support dental and medical-adjacent businesses across Reno, Sparks, and nearby Truckee Meadows corridors. For practices near Kirman Avenue, access-control issues can escalate quickly because scheduling, imaging, billing, and records handling all depend on stable endpoint and identity management. Local response matters, but so does having the underlying documentation and recovery process in place before the next lockout occurs.
Closing the Login Gap Before It Becomes a Case File
Dental offices in The Truckee Meadows cannot treat repeated login failures as isolated inconvenience. When access control, endpoint oversight, and records handling are loosely managed, the business is exposed to downtime first and legal scrutiny second. The real fix is disciplined documentation, consistent technical controls, and a response process that works under pressure.
In practice, that means knowing who has access, which devices are trusted, how protected information is handled during disruption, and how quickly the office can recover without creating a second problem. Businesses that address those basics early are in a much stronger position when systems are strained.

