Reno Lockout Risks
When a business is dealing with a lockout, the failure usually started earlier. Unclear ownership, overlapping tools, and fragmented support can weaken business continuity and backup compliance over time and leave medical practices in The Truckee Meadows exposed when pressure hits. Addressing the problem means clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
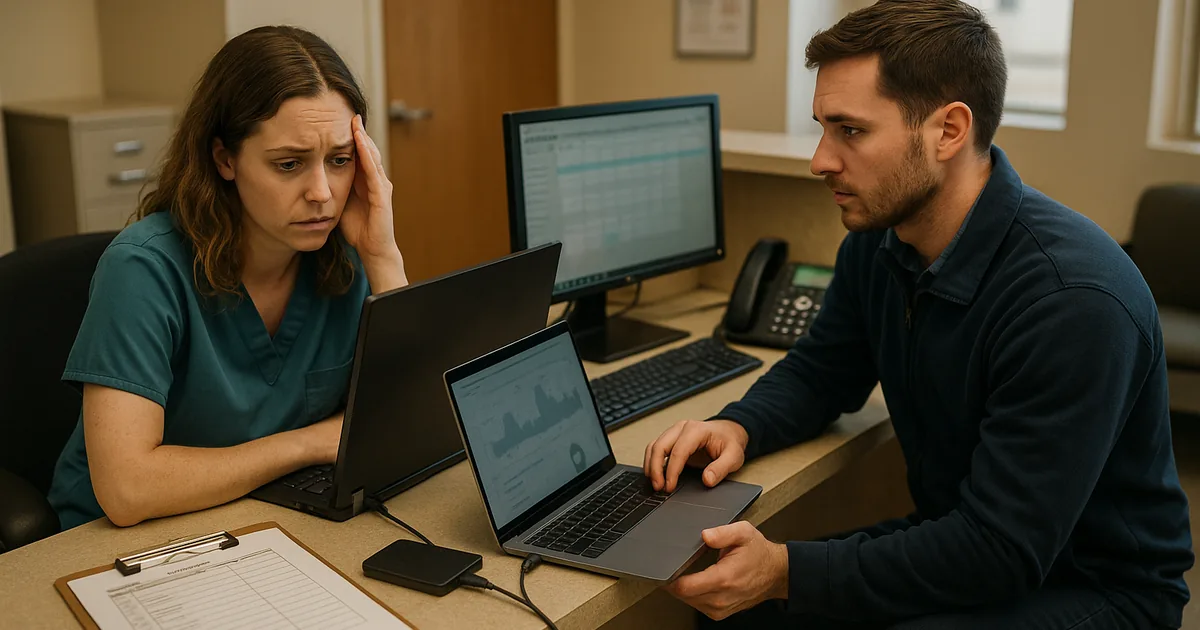
Where Vendor Chaos Actually Causes a Lockout
A medical practice usually does not get locked out because of one dramatic failure. In The Truckee Meadows, we more often see a chain of smaller management gaps: one vendor controls the firewall, another handles phones, a software reseller owns licensing, and nobody clearly owns identity, backups, or escalation. That is the core risk behind vendor chaos. When access fails, every provider can explain their own boundary, but no one is accountable for restoring operations end to end.
This is why business continuity and backup compliance in Northern Nevada has to include ownership mapping, not just backup software. In a medical office, lockouts affect more than email. They can interrupt patient intake, e-fax workflows, chart access, claims processing, and front-desk coordination. In Heidi’s case, the immediate symptom looked like a login problem, but the root cause was fragmented administration across multiple vendors with no tested escalation path and no single source of truth for privileged access.
- Technical factor: Shared admin credentials, undocumented vendor handoffs, and overlapping remote tools create confusion during outages and slow recovery when a practice needs fast access restoration.
- Operational factor: Office managers are often left coordinating internet, phones, software, printers, and line-of-business vendors even though that work requires technical authority and documented response ownership.
- Business consequence: Delayed appointments, missed billing windows, staff downtime, and backup uncertainty can all stack up quickly in a regulated healthcare environment.
How to Reduce Lockout Risk Before the Next Outage
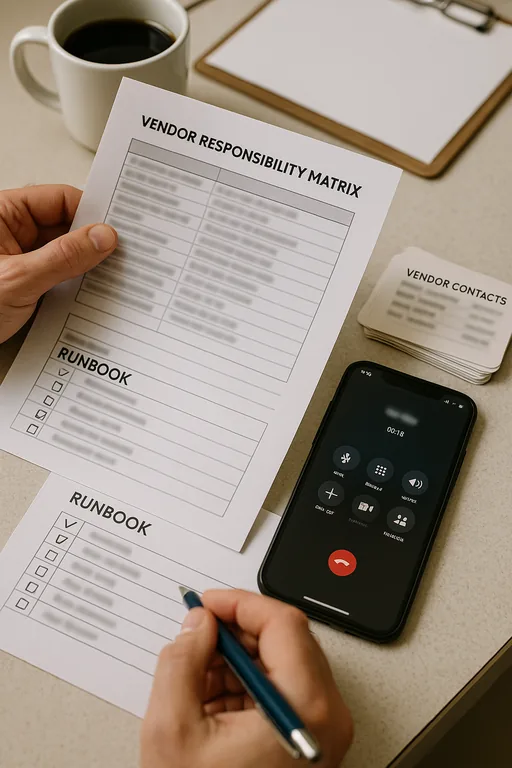
The practical fix is not adding more vendors. It is reducing ambiguity. We typically start by documenting who owns identity, who owns endpoint security, who can authorize account changes, where backups are stored, and how failover decisions are made. For medical practices, that also means confirming that vendor access is limited, monitored, and removable without breaking daily operations.
From there, the environment needs layered controls: tested backup recovery, documented emergency admin access, MFA enforcement, and endpoint visibility. Practices that want to contain account compromise and workstation-based disruption usually benefit from endpoint and threat protection for healthcare operations tied to alerting and response. Guidance from CISA is useful here because it emphasizes recovery planning, identity control, and validation rather than assuming backups alone will solve the problem.
- Control step: Build a vendor responsibility matrix that assigns ownership for internet, phones, line-of-business applications, Microsoft 365, backups, MFA, and emergency escalation.
- Control step: Validate backup recovery against real systems, not just successful job reports, so the practice knows whether patient and billing data can actually be restored.
- Control step: Standardize MFA, privileged access, and account recovery procedures to reduce the chance that a single lockout spreads across multiple systems.
Field Evidence: Multi-Vendor Recovery in a Reno Medical Office
We worked through a similar situation for a healthcare office operating between central Reno and Sparks where internet service, VoIP, Microsoft 365, and backup administration were split across separate providers. Before remediation, the practice had no current escalation list, no confirmed backup test history, and no documented owner for identity changes. A simple account issue turned into a half-day outage because each vendor only checked their own system.
After consolidating escalation paths, documenting administrative ownership, and tightening identity and email security controls , the office had a single incident workflow for access failures. That mattered during a later disruption caused by a carrier-side service issue and a building handoff problem common in older Reno commercial spaces. Instead of spending hours deciding who should respond, the team had a defined sequence for failover, user communication, and recovery validation.
- Result: Access-related downtime dropped from nearly 4 hours of confusion to under 45 minutes of controlled response, with verified backup status and no missed billing batch that week.
Reference Table: Systems Most Affected by Vendor Ownership Gaps
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Business Continuity And Backup Compliance and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
Medical offices in Reno, Sparks, and nearby practice corridors often depend on several outside providers at once, which makes response discipline especially important when access fails. Our office on Ryland Street is close to downtown Reno and only about 3 minutes from the destination noted here, which helps when a situation requires local coordination, on-site review, or direct vendor escalation.
What Medical Practices Should Take Away
If a practice in The Truckee Meadows gets locked out, the visible outage is usually only the final stage of a longer control problem. Unclear vendor boundaries, weak escalation discipline, and untested recovery procedures create the conditions for downtime, delayed billing, and compliance exposure.
The right response is operational clarity. Define ownership, reduce overlapping tools, verify backup recovery, and make sure identity, endpoint, and communications systems can be restored in a controlled order. That is how practices shorten outages and avoid turning a manageable incident into a multi-vendor scramble.

