Truckee Lockout
When a business is dealing with a lockout, the failure usually started earlier. Phishing clicks, password reuse, and weak account hygiene can weaken compliance and risk management over time and leave medical practices in The Truckee Meadows exposed when pressure hits. Addressing the problem means tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
How Human Error Turns Into a Medical Practice Lockout
The immediate problem in most lockout events is not the login screen. It is the chain of weak decisions and missing controls that came before it. In The Truckee Meadows, we regularly see medical offices relying on reused passwords, inconsistent multifactor enrollment, shared admin habits, and staff who are expected to identify phishing messages without enough reinforcement. That combination creates a direct path from one convincing email to a business interruption that affects patient flow, billing, and compliance posture.
For healthcare operations, the human element matters because identity is now the front door to nearly every system. Email, EHR access, document storage, remote sessions, and vendor portals often depend on the same credentials or the same identity provider. Once an attacker gets a valid sign-in, they do not need to break the firewall first. They can reset passwords, register rogue MFA methods, and block legitimate users out. That is why compliance and risk management in Northern Nevada has to include user behavior, access governance, and documented response steps rather than policy paperwork alone.
- Phishing-driven credential theft: A fake reset or shared-document email can capture valid credentials and session tokens before anyone realizes the account has been compromised.
- Password reuse: Staff who reuse passwords across portals increase the chance that one exposed credential leads to multiple system lockouts.
- Weak MFA enrollment control: If users can add new authentication methods without review, attackers can establish persistence quickly.
- Shared operational dependency: Scheduling, intake, and billing teams often rely on the same cloud identity platform, so one compromised account can disrupt several workflows at once.
- Delayed escalation: In cases like Tyler’s, the first signs are often dismissed as a simple login issue, which gives the attacker more time to change settings and expand access.
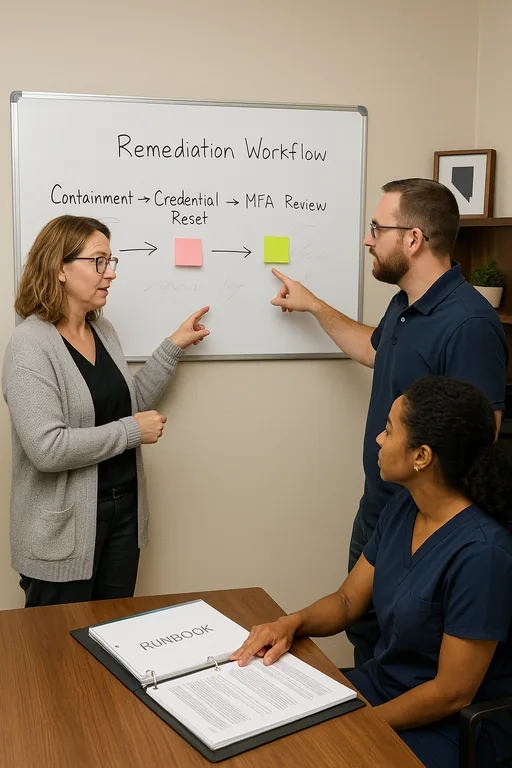
Practical Remediation for Identity, Access, and Daily Security Habits
The fix starts with containment, then moves into control hardening. We typically revoke active sessions, reset credentials, review MFA registrations, validate mailbox rules, and confirm whether any forwarding, privilege changes, or unauthorized sign-ins occurred. After that, the real remediation work is operational: enforce phishing-resistant MFA where possible, remove shared accounts, require unique passwords through a managed password platform, and tighten conditional access around location, device trust, and impossible-travel events.
Medical practices also need infrastructure support behind those identity controls. Stable segmentation, secure remote access, and reliable monitoring reduce the blast radius when a user account is compromised. That is where IT systems for multi-location operations become important, especially for clinics balancing front-desk traffic, cloud applications, printers, imaging devices, and vendor connections across Reno, Sparks, and surrounding offices. For a practical baseline on reducing phishing and account compromise risk, the CISA guidance on strong passwords and account protection is a useful reference.
- Identity lockdown: Reset compromised accounts, revoke sessions, remove unauthorized MFA methods, and review sign-in logs for persistence.
- MFA hardening: Require multifactor authentication for all staff, with stronger enrollment controls and reduced reliance on SMS where possible.
- Conditional access: Limit sign-ins by geography, device state, and risk signals to reduce successful account takeover attempts.
- Phishing simulation and retraining: Use short recurring exercises tied to real email patterns staff actually receive, including fake password reset prompts.
- Alerting improvements: Trigger immediate review for mailbox rule creation, impossible travel, excessive failed logins, and privilege changes.
Field Evidence: Restoring Access Without Repeating the Same Failure
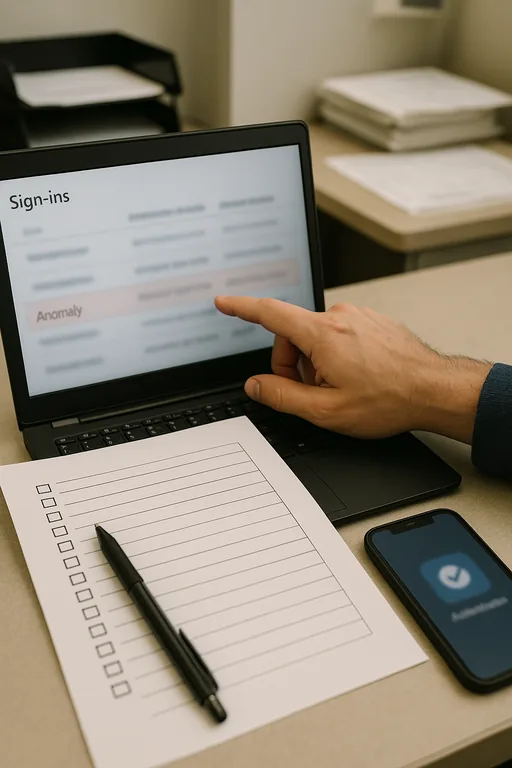
We worked through a similar pattern with a healthcare office operating between central Reno and Sparks where front-desk staff were intermittently locked out after a phishing event triggered unauthorized MFA changes. Before remediation, the office had no consistent process for reviewing sign-in anomalies, and password resets were handled ad hoc. Appointment confirmations stalled, scanned documents backed up at reception, and billing staff had to wait until account ownership was sorted out.
After the response, the practice moved to standardized MFA enrollment, conditional access review, mailbox auditing, and documented escalation for suspicious login prompts. We also recommended tighter server-side oversight through secure business systems from ransomware and account abuse, particularly where line-of-business applications still depended on hybrid infrastructure. In a corridor where weather, provider outages, and staffing gaps already create enough friction, removing identity chaos made the operation noticeably steadier.
- Result: Account recovery time dropped from most of a workday to under 45 minutes, repeat lockouts stopped, and same-day scheduling and billing continuity improved within the first month.
Reference Table: Controls That Reduce Lockout Risk in Medical Offices
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Compliance And Risk Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.
Local Support in The Truckee Meadows
Reno Computer Services supports medical and professional offices throughout The Truckee Meadows, including central Reno, Sparks, and the university corridor. For lockouts tied to phishing, password misuse, or identity control failures, proximity matters, but process matters more. Fast local response helps contain the issue, validate access, and keep scheduling and billing disruption from spreading into a larger compliance problem.
What Medical Practices Should Take Away From a Lockout Event
A lockout at a medical practice in The Truckee Meadows is usually the visible symptom of a deeper identity and process problem. The common thread is not advanced malware. It is weak account hygiene, inconsistent access controls, and too much trust placed in users to spot every fake reset message under pressure. When those gaps are left alone, downtime, delayed billing, and compliance exposure follow.
The practical response is straightforward: tighten identity controls, standardize MFA enrollment, remove risky password habits, and make suspicious login events part of normal operational review. That approach reduces both the chance of a lockout and the time it takes to recover when one happens.

