Reno Lockout
Problems like this tend to stay hidden until something important breaks. For medical practices in South Meadows, that often means a lockout, avoidable delays, or a bigger recovery burden than expected. The best response is hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Hidden Credential Abuse Causes Medical Practice Lockouts
The invisible threat in most lockout incidents is not a firewall failure. It is identity misuse. Modern attackers often do not force entry through the network edge. They sign in with stolen usernames, reused passwords, legacy app credentials, or session tokens that appear valid at first glance. That is why a South Meadows medical practice can feel stable one day and then suddenly lose access to Microsoft 365, line-of-business systems, or shared files the next.
For healthcare offices, the business impact is immediate. Scheduling slows down, intake staff cannot confirm appointments, providers lose access to messages, and billing teams fall behind. In our experience, these events also create compliance exposure because the same weak controls that allow unauthorized sign-ins often leave gaps in logging, retention, and incident response. Practices trying to strengthen regulatory compliance support in Reno medical environments need to treat identity as a core control, not just a convenience layer. That was the real issue behind the lockout Nil faced: the account problem was only the visible symptom.
- Identity blind spots: Stolen credentials, weak MFA enrollment, unmanaged mobile devices, and incomplete sign-in monitoring allow unauthorized access attempts to blend in with normal user behavior.
- Healthcare workflow dependence: Front-desk teams, providers, and billing staff rely on cloud identity for email, scheduling, document access, and secure communications, so one compromised account can disrupt multiple departments.
- Local operational complexity: Practices in South Meadows often coordinate with labs, specialists, and remote staff across Reno and Sparks, which increases the number of endpoints, sessions, and access paths that must be monitored.
- Technical factor: Conditional access and sign-in analytics are often underconfigured, leaving suspicious login patterns undiscovered until an account is locked, a mailbox rule is changed, or a user is forced offline.
Practical Remediation for Identity Hardening and Recovery
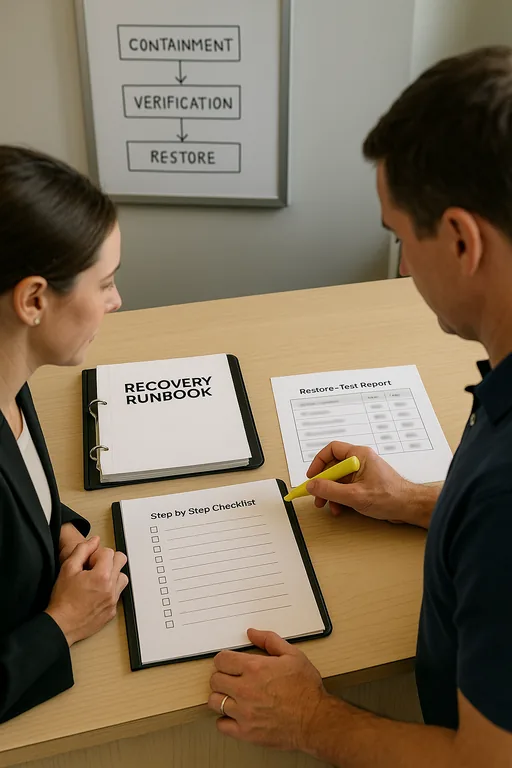
The fix is not a single tool. It is a layered response that starts with account containment, log review, token revocation, password reset, MFA validation, and device trust verification. After that, the practice needs to close the conditions that allowed the event in the first place. For medical offices, that usually means tightening conditional access, removing stale accounts, limiting administrative privileges, and validating that backup and recovery processes can support both email and operational data if a broader compromise is discovered.
We also recommend testing restore paths, not just assuming they work. Offices that depend on cloud platforms still need managed backup solutions for healthcare operations so a mailbox compromise, file deletion event, or ransomware spillover does not become a long outage. For control guidance, the CISA identity security recommendations are a practical baseline, especially when paired with MFA enforcement and alerting tuned for abnormal sign-in behavior.
- Control step: Enforce phishing-resistant MFA where possible, block legacy authentication, review impossible-travel and risky sign-in alerts daily, and document a short recovery runbook for account lockout, token revocation, and access restoration.
- Backup validation: Confirm that email, shared files, and critical practice data can be restored to a known-good state within an acceptable recovery window.
- Endpoint trust: Require managed devices for sensitive access and isolate noncompliant systems until they are reviewed.
- Alerting improvements: Route identity alerts to a monitored queue so suspicious activity is investigated before staff discover it through downtime.
Field Evidence: Credential Lockout Recovery in a Busy Reno Medical Corridor
We have seen this pattern in offices operating between South Meadows and central Reno where patient flow starts early, providers move between locations, and front-desk teams depend on cloud access from the first appointment block. Before remediation, the practice was reacting to isolated login complaints with password resets and no broader review of sign-in telemetry, mailbox rules, or session history. That approach restored access temporarily but left the root cause in place.
After implementing stronger identity controls, backup validation, and documented disaster recovery planning for business continuity , the office had a clearer response path. A later suspicious login event was contained in minutes instead of hours, no appointments were canceled, and staff kept working from approved devices while the account was remediated. In Northern Nevada, where small healthcare teams often cover multiple responsibilities at once, that difference matters.
- Result: Account containment time dropped from roughly 4 hours to under 25 minutes, with no confirmed data loss and no same-day billing interruption.
Reference Controls for Hidden Identity Threats in Medical Practices
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Regulatory Compliance Support and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, and Northern Nevada and Northern Nevada.
Local Support in South Meadows and Greater Reno
Medical practices in South Meadows often need fast coordination with support resources in central Reno, especially when identity issues affect scheduling, billing, or secure communications. From our office on Ryland Street, the route to Saint Mary’s Medical District is typically about 7 minutes under normal conditions, which reflects how closely connected these healthcare corridors are operationally even when the incident starts in a different part of town.
What Medical Practices Should Take Away
If a medical practice in South Meadows gets locked out, the visible outage is usually not the whole problem. The deeper issue is often unauthorized identity use that bypassed weak controls, went unnoticed in logs, or spread through unmanaged access paths. That is why the right response starts with containment and then moves quickly into verification, monitoring, and recovery planning.
Practices that treat identity, backup validation, and incident response as connected operational controls are in a much better position to avoid downtime, protect billing flow, and support compliance obligations. The goal is not to add complexity. It is to remove the blind spots that let a routine login become a business interruption.

