Reno Med Lockout
Seeing a lockout is often the visible symptom of compliance gaps, not the root problem itself. In medical practices across Reno, issues like missing controls, weak documentation, and loose access policies can quietly undermine managed IT services until work stops or risk spikes. The fix usually starts with reviewing controls, access, and recovery steps before they are tested under pressure.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Compliance Gaps Turn Into Lockouts
A medical practice usually gets locked out because a control failed long before the visible outage. In Reno healthcare environments, we often find the real issue is not the password reset itself but the absence of documented access reviews, role-based permissions, termination procedures, backup validation, and policy alignment with HIPAA and related operational requirements. Regulations change faster than many internal teams can document them, and that gap creates unstable conditions where managed systems keep running until one event exposes the weakness.
For clinics, specialty offices, and multi-provider practices across Reno and Sparks, this matters because scheduling, EHR access, imaging portals, billing platforms, and secure messaging all depend on tightly managed identity and device controls. When those controls drift, a lockout can spread into patient intake delays, chart access interruptions, and claim submission backlogs. That is why businesses dealing with recurring access issues often need structured oversight through managed IT support in Reno that ties security controls to daily operations instead of treating compliance as paperwork. In cases like Ryan’s, the lockout was only the moment the underlying governance problem became impossible to ignore.
- Identity governance: User accounts remain active too long, permissions accumulate over time, and practices lose visibility into who can access clinical, billing, and administrative systems.
- Documentation drift: Policies may exist, but they are outdated, incomplete, or disconnected from actual workflows used by front-desk staff, providers, and remote administrators.
- Recovery weakness: Teams may have backups in place without confirming whether access restoration, MFA recovery, and application reauthorization can be completed quickly during an outage.
- Compliance pressure: HIPAA expectations around access control, auditability, and safeguards become harder to meet when internal IT processes are informal or inconsistent.
How To Correct the Gap Before It Stops Operations
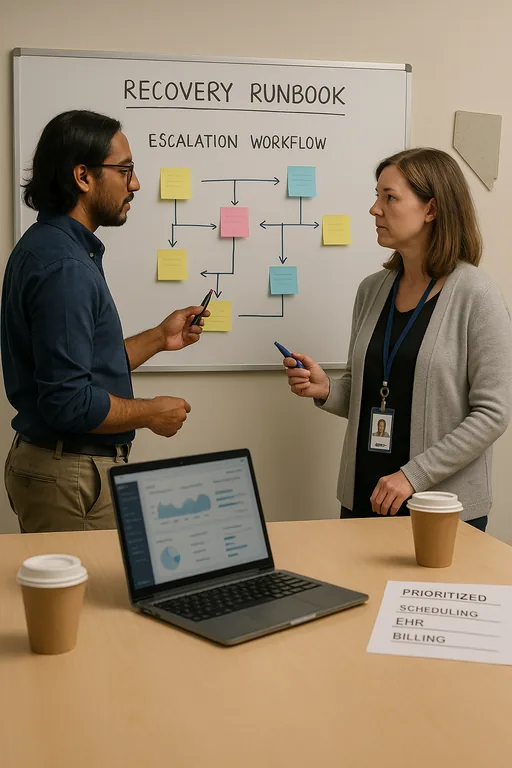
The practical fix starts with control mapping. We review who has access to what, how that access is approved, where MFA is enforced, how devices are managed, and whether backup and recovery steps are tested against the systems the practice actually uses every day. In a medical office, remediation should not stop at resetting credentials. It should include documented onboarding and offboarding, privileged access review, audit log retention, secure remote access standards, and recovery runbooks that front-office staff can follow under pressure.
Support processes matter just as much as technical controls. A clinic with a strong escalation path and responsive IT support for medical office interruptions can contain a lockout faster, preserve evidence, and restore staff access in a controlled order. For healthcare-specific guidance on access safeguards and security expectations, the HHS HIPAA Security Rule guidance remains a useful operational reference.
- Access review: Reconcile every user, role, and application permission against current job duties and remove legacy or shared access immediately.
- MFA hardening: Enforce multifactor authentication for email, EHR portals, remote access, and administrator accounts with documented recovery procedures.
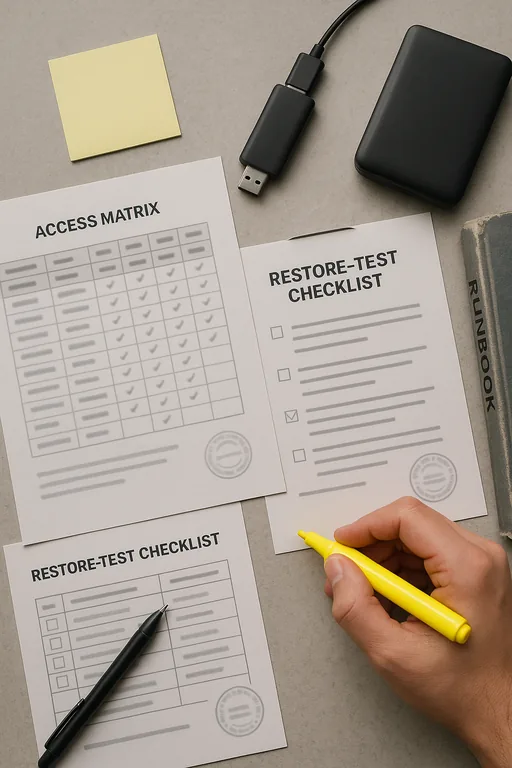
- Backup validation: Test not only file restoration but also application access, credential recovery, and line-of-business system availability after an incident.
- Endpoint control: Standardize workstation configuration, patching, and policy enforcement so front-desk and clinical devices do not drift out of compliance.
Field Evidence: Restoring Access Without Repeating the Failure
We have seen this pattern in Northern Nevada offices operating between Reno, Sparks, and the industrial corridors where administrative teams depend on stable remote access back to central systems. Before remediation, the practice had inconsistent account ownership, no reliable quarterly access review, and no tested sequence for restoring billing and scheduling first. After remediation, the office had a documented access matrix, enforced MFA on critical systems, validated backup recovery steps, and clearer escalation for account and device issues.
The operational difference was immediate. Instead of treating every login problem as a one-off help desk event, the practice moved to a controlled support model with better auditability and faster endpoint response through proactive endpoint management for healthcare workstations . That reduced repeat lockouts, shortened restoration time, and gave leadership a clearer compliance record during internal review.
- Result: Repeat access incidents dropped, priority systems were restorable in a defined order, and the office reduced account-related downtime from most of a morning to under 45 minutes during later disruptions.
Medical Practice Compliance and Access Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed It Services and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.
Local Support in Reno, Sparks, Carson City, and Northern Nevada
Medical practices in Reno often need support that understands both compliance pressure and the practical realities of serving nearby corridors such as USA Parkway and the Tahoe-Reno Industrial Center. From our Reno office, we regularly help organizations stabilize access, document controls, and respond to outages without losing sight of billing, scheduling, and patient workflow priorities.
What Medical Practices Should Take From This
A lockout in a Reno medical practice is rarely just a password problem. More often, it is the operational result of weak access governance, incomplete documentation, and recovery steps that were never tested against real clinical and billing workflows. When compliance requirements move faster than internal processes, the gap eventually shows up as downtime, delayed claims, or avoidable audit exposure.
The practical response is to treat compliance as part of system operations, not as a separate checklist. Practices that review access regularly, standardize endpoint controls, validate recovery, and maintain clear support escalation are in a much better position to keep patient-facing work moving when something fails.

