Reno Lockout Help
This kind of issue rarely appears all at once. For medical practices in Northern Nevada, it usually builds through phishing clicks, password reuse, and weak account hygiene and then surfaces as a lockout, slower recovery, or higher exposure. A more reliable setup starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Medical Practices Get Locked Out Before They Realize They Have a Security Problem

The human element gap is usually not a single dramatic failure. In medical offices across Reno, Sparks, Carson City, and surrounding Northern Nevada locations, we more often see a chain of small decisions: a reused password, a rushed click on a fake reset notice, a shared account that no one fully owns, or an employee working through a busy intake window without enough verification steps. The lockout is what gets attention, but the underlying issue is weak identity discipline.
That matters because medical practices do not just lose email access when this happens. They can lose scheduling visibility, patient communication, EHR-related workflow continuity, and the ability to recover cleanly when systems are under strain. Problems like this also erode disaster recovery planning and recovery because teams assume backups solve everything, when in reality account compromise can block access to cloud tools, admin consoles, and recovery workflows. Practices trying to reduce that exposure usually need disaster recovery planning and recovery in Northern Nevada that accounts for identity failure, not just server failure. In cases like Paul’s, the operational damage starts at the front desk but quickly spreads into billing, provider schedules, and compliance risk.
- Identity controls: Weak passwords, reused credentials, and incomplete multifactor enforcement make it easier for phishing emails to trigger account lockouts or unauthorized access.
- Shared workflow dependence: Medical offices often rely on shared mailboxes, scheduling tools, and cloud logins, so one compromised account can interrupt multiple staff roles at once.
- Recovery blind spots: If recovery plans do not include account restoration, privilege review, and cloud access validation, downtime lasts longer than expected.
Practical Remediation for the Human Element Gap
The fix is not just more training. It is a tighter operating model. We typically start by reviewing Microsoft 365 or Google Workspace identity settings, confirming multifactor authentication coverage, removing legacy authentication where possible, and separating shared workflow access from personal credentials. Medical practices also need tested procedures for password reset validation, conditional access, and rapid account containment when a phishing click occurs.
From there, the work becomes operational: role-based access, documented escalation paths, and recurring review of risky sign-ins. This is where technology advisory and assessment for medical operations helps, because the goal is to align security controls with how the office actually functions during intake, referrals, billing, and provider scheduling. For practical guidance on phishing-resistant controls and account protection, CISA’s recommendations on strong passwords and multifactor authentication are a useful baseline.
- MFA hardening: Require multifactor authentication for all users, especially email, remote access, and administrator accounts.
- Phishing-resistant workflow: Train staff to verify reset requests and login prompts through a second channel before acting.
- Account segmentation: Separate admin privileges from daily user accounts and eliminate unnecessary shared credentials.
- Recovery validation: Test whether the practice can still access backup, email, and line-of-business systems after an account compromise.
Field Evidence: Front Desk Lockout to Controlled Recovery
We worked through a similar pattern with a Northern Nevada healthcare office operating between a Reno clinic and an administrative support location. Before remediation, the practice had inconsistent MFA enrollment, no formal process for validating password reset emails, and too much dependence on a few staff accounts for scheduling and billing. A single phishing event created account lockouts, delayed patient intake, and forced manual workarounds for much of the day.
After tightening identity policies, documenting response steps, and aligning leadership around IT strategy engagements for multi-location operations , the office reduced recovery friction significantly. The next suspicious login event was contained without a broad lockout, and staff were able to continue patient-facing work while access was reviewed. That kind of improvement matters in Northern Nevada, where smaller practices often do not have deep internal IT coverage and cannot afford to lose half a day to preventable credential issues.
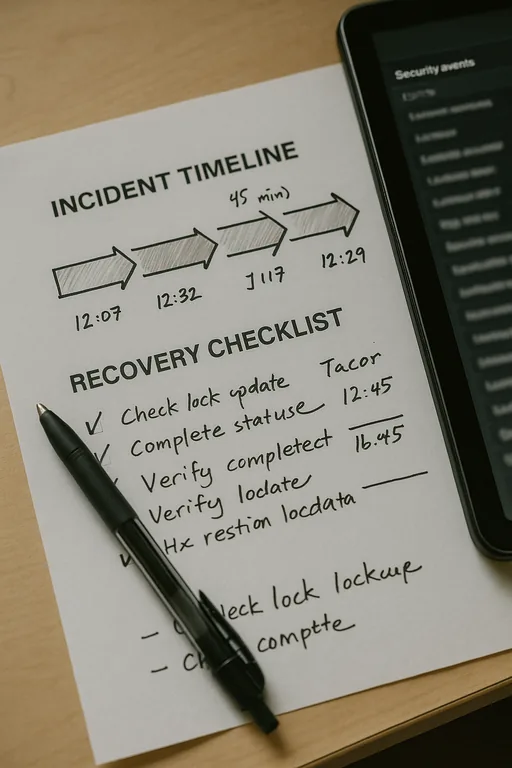
- Result: Recovery time dropped from most of a business day to under 45 minutes, with no missed provider sessions and far less billing delay.
Medical Practice Identity and Recovery Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Disaster Recovery Planning And Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across Northern Nevada and Northern Nevada.
Local Support in Northern Nevada
Medical offices in Reno and nearby communities often need fast, practical support when identity issues interrupt patient flow. From our Ryland Street location, the route to the Crystal Lake Office Park area is typically about 17 minutes under normal conditions, which is close enough for local coordination but still a reminder that prevention matters more than waiting for an emergency response. For practices balancing compliance, scheduling, and limited internal IT coverage, local planning has to account for both security and recovery.
Reduce Lockout Risk Before It Spreads Into Recovery Failure
For medical practices in Northern Nevada, user behavior is often the first point of failure and the first place to improve. A fake password reset email, weak password habits, or incomplete MFA coverage can interrupt scheduling, billing, and patient communication faster than most offices expect. The lockout is only the visible symptom.
A stronger response combines identity controls, tested recovery procedures, and realistic staff habits. When those pieces are aligned, practices recover faster, contain incidents earlier, and avoid turning a routine phishing mistake into a larger operational outage.

