Reno Encrypt Fail
What looks like a one-off issue is often tied to untested backups. In manufacturing plant environments, failed restore tests, missing dependencies, and an unclear recovery order can turn into recovery time, data availability, and business continuity long before anyone notices the warning signs. Closing those gaps early makes managed IT support plans far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Resilience Test Fails Before the Restore Ever Starts
When encrypted files show up in a Washoe County manufacturing plant, the immediate question is usually whether a backup exists. The more important question is whether that backup has been restored under realistic conditions. A backup is just a copy; business continuity is the ability to keep working while the server is effectively unavailable. In plant environments, that difference matters because file shares often support scheduling, quality records, shipping labels, purchasing, and machine-adjacent documentation all at once.
We typically find that the resilience failure comes from dependencies that were never documented or tested together. A server image may restore successfully, but mapped drives break, SQL services start in the wrong sequence, print queues do not reconnect, or a line-of-business application expects an older hostname or credential path. That is why businesses relying on managed IT support plans in Washoe County need restore validation, not just backup status reports. In cases like Alexandra’s, the visible symptom is encrypted files, but the real issue is that recovery order, application dependency, and operator workflow were never tested as one process.
- Restore testing gap: Backup jobs may report success while the actual recovery chain fails because application services, permissions, or network paths were not validated in a live test.
- Hidden dependency risk: Manufacturing systems often rely on shared folders, print servers, ERP databases, scanner workstations, and vendor utilities that must come back in a specific order.
- Operational continuity exposure: Even if production equipment keeps running, shipping, receiving, QA documentation, and billing can stall long enough to create downstream delays.
- Local infrastructure reality: Across Reno, Sparks, and broader Washoe County, multi-building layouts, older industrial construction, and mixed carrier environments can complicate recovery if network failover and storage access are not tested together.
How to Build a Recovery Process That Actually Works Under Pressure
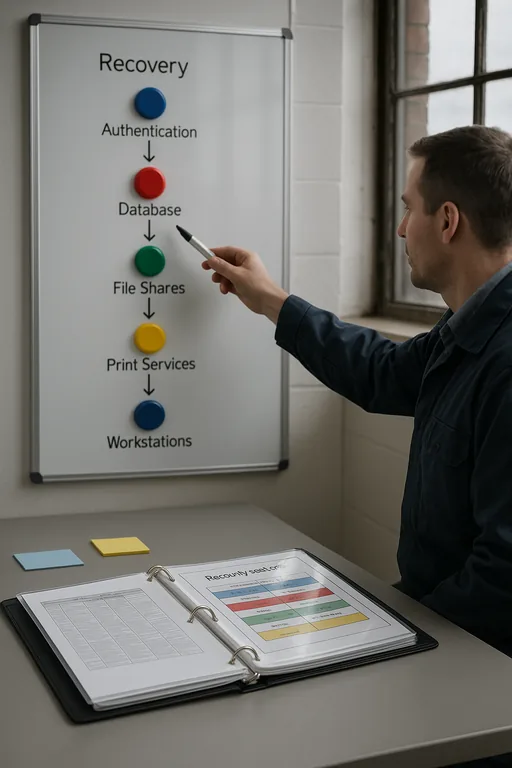
The practical fix is to move from backup ownership to recovery ownership. That means defining recovery tiers, documenting dependency order, and running scheduled restore tests against the systems that matter most to plant operations. For a manufacturing site, we usually prioritize ERP data, production scheduling files, print services, domain authentication, and any workstation or server that supports shipping and compliance records. The goal is not simply to restore data, but to restore usable operations.
That work should be tied to policy and accountability. A documented recovery sequence, approval chain, and test schedule fit naturally into governance and audit preparation for business IT , especially where retention, traceability, or customer requirements apply. It is also worth aligning the process with practical guidance from CISA’s ransomware resilience guidance , which emphasizes tested backups, segmented recovery planning, and incident response discipline.
- Recovery order mapping: Document which systems must return first, including authentication, storage, databases, print services, and line-of-business applications.
- Backup validation: Run scheduled restore tests to isolated environments and confirm files open, applications authenticate, and users can complete real tasks.
- Immutable and segmented copies: Maintain protected backup copies that cannot be altered by the same credentials used in daily operations.
- Endpoint and identity hardening: Pair recovery planning with MFA enforcement, EDR deployment, and privileged access controls so the same event is less likely to recur.
- Alerting and escalation: Set alerts for failed jobs, missed replication windows, storage anomalies, and restore-test exceptions so issues are addressed before an incident.
Field Evidence: Restore Readiness in an Industrial Corridor
We worked through a similar resilience issue for a multi-shift operation in the Sparks industrial corridor where backups had been running for months without a full application restore test. Before remediation, the business could confirm that data copies existed, but it could not prove that production support files, shipping workstations, and reporting systems would return in a usable sequence. The result was uncertainty around downtime, customer commitments, and internal recovery ownership.
After documenting dependencies, testing restores quarterly, and separating critical recovery tiers, the environment shifted from reactive to measurable. The business reduced restore uncertainty, shortened decision time during incidents, and established clearer expectations between operations, finance, and IT. For organizations with customer, contractual, or regulatory obligations, this is also where compliance-focused IT management becomes operationally useful rather than theoretical.
- Result: Verified recovery time for core file and application services dropped from an estimated full-day disruption to a tested 2.5-hour recovery window for priority systems.
Resilience Test Reference Points for Manufacturing IT
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed It Support Plans and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.
Local Support in Washoe County
From our Reno office, we regularly support manufacturers, warehouses, and multi-site operations across Sparks and the broader Washoe County industrial footprint. For plants near Vista Boulevard, short drive time helps, but tested recovery procedures matter more than proximity when encrypted files interrupt production support, shipping records, or quality documentation.
The Operational Takeaway
Encrypted files in a manufacturing environment are often treated as a security event alone, but the larger business problem is usually recovery readiness. If backups have not been tested against real dependencies, the organization does not yet know its true recovery time, its data availability limits, or which business functions will stall first.
For Washoe County manufacturers, resilience improves when backup validation, recovery sequencing, and continuity planning are handled as one operating discipline. That is what turns a copy of data into a workable recovery process.

