Truckee Audit
When a business is dealing with encrypted files, the failure usually started earlier. Unclear ownership, overlapping tools, and fragmented support can weaken managed IT services over time and leave manufacturing plants in The Truckee Meadows exposed when pressure hits. Addressing the problem means clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Encrypted Files Usually Point to a Vendor Ownership Failure

When files are encrypted in a Truckee Meadows manufacturing environment, the visible problem is ransomware or unauthorized encryption, but the underlying issue is often operational fragmentation. We regularly find that internet circuits, firewall changes, endpoint tools, line-of-business applications, backup agents, and user onboarding are split across several vendors with no single party accountable for escalation. That is the core of vendor chaos. It leaves office managers chasing phone numbers instead of triggering a defined incident process.
In manufacturing plants, that gap shows up fast. Shared folders drive production schedules, purchasing, quality documents, shipping paperwork, and machine-side reference files. If one vendor manages the firewall, another handles Microsoft 365, another sold the backup appliance, and nobody is responsible for endpoint monitoring, encryption can spread before anyone confirms where the alert originated. Businesses trying to stabilize this kind of exposure usually need managed IT support in Reno that establishes ownership across vendors instead of letting each provider defend only their own piece. That is why incidents like the one Wesley faced tend to last longer than they should.
- Technical factor: Overlapping tools and unclear escalation paths create blind spots between endpoint security, backup monitoring, identity controls, and network administration, which delays containment and increases downtime.
- Operational factor: Manufacturing teams in The Truckee Meadows depend on shared file access for scheduling, receiving, inventory, and shipment release, so even a partial encryption event can disrupt the entire day.
- Local factor: Multi-vendor environments are common in Reno and Sparks industrial corridors where businesses have added systems over time without consolidating accountability.
How to Clean Up the Response Path and Reduce Repeat Exposure
The fix is not just restoring files. The real remediation is assigning ownership, simplifying the toolset, and documenting who has authority to act during an incident. We typically start by identifying every vendor touching the environment, then mapping which systems they control, what alerts they receive, and who is authorized to isolate devices, disable accounts, and approve recovery steps. That process usually exposes duplicate tools, unmanaged endpoints, stale admin accounts, and backup assumptions that were never tested.
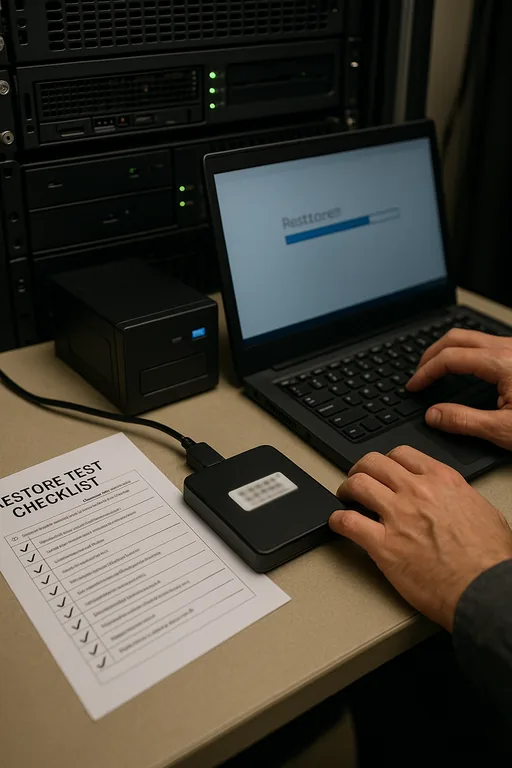
From there, the environment needs practical controls: endpoint detection and response, MFA enforcement, privileged access review, network segmentation for production and office traffic, and verified restore testing. A structured approach to backup and recovery programs matters because many businesses discover too late that backups existed but were incomplete, inaccessible, or too old to support operations. For incident planning and ransomware readiness, the guidance from CISA’s StopRansomware resources is useful because it aligns technical controls with response discipline.
- Control step: Assign one accountable IT owner for incident coordination, vendor escalation, and recovery approval.
- Control step: Separate production systems, office devices, and guest or unmanaged traffic with VLAN segmentation and access policy review.
- Control step: Validate backups with routine file-level and server-level restore tests, not just backup job success messages.
- Control step: Standardize alerting so endpoint, identity, and backup failures are visible in one response workflow.
Field Evidence: Vendor Cleanup Reduced Recovery Time in a Reno Industrial Corridor
We worked through a similar situation for a Northern Nevada operation where file access, remote connectivity, and backup ownership were spread across multiple providers. Before cleanup, nobody could answer a basic question during an outage: who had authority to isolate endpoints, confirm backup integrity, and coordinate with the software vendor. The business had experienced repeated delays because each provider waited for another to act.
After consolidating escalation ownership, documenting vendor boundaries, and tightening IT systems for multi-location operations , the environment became much easier to defend and recover. In practical terms, that meant faster isolation of affected devices, cleaner restore decisions, and fewer hours lost when connectivity or file access problems hit. In the Reno industrial areas where weather, carrier handoffs, and older building infrastructure can complicate troubleshooting, that clarity matters more than most businesses expect.
- Result: Incident triage time dropped from several hours of vendor back-and-forth to under 45 minutes, and tested recovery procedures reduced expected file restoration time by more than 60 percent.
Reference Table: Where Vendor Chaos Creates Encryption Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed It Services and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.
Local Support in The Truckee Meadows
Manufacturing businesses in Reno, Sparks, and the surrounding Truckee Meadows often need fast on-site coordination when file access, vendor handoffs, or recovery decisions stall operations. From our Reno office, we support local facilities that need practical escalation, clearer ownership, and response processes that work under production pressure.
Clear Ownership Matters More Than Another Vendor
Encrypted files in a manufacturing plant usually expose a management problem before they expose a technology problem. If ownership is split across too many vendors, response slows down, backups become assumptions, and production teams lose time waiting for someone to take control. In The Truckee Meadows, where many businesses have layered systems over years of growth, that pattern is common.
The practical takeaway is straightforward: define who owns the incident, simplify the stack where possible, test recovery, and make sure every vendor boundary is documented before the next outage. That is what turns a chaotic event into a controlled recovery.

