Truckee Data Recovery
When a business is dealing with encrypted files, the failure usually started earlier. Surprise spending, delayed upgrades, and aging infrastructure can weaken managed cybersecurity programs over time and leave manufacturing plants in The Truckee Meadows exposed when pressure hits. Addressing the problem means planning upgrades deliberately and aligning IT decisions to business risk.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Usually Point to a Budgeting Failure First
When files are encrypted in a manufacturing environment, the immediate issue is security, but the underlying cause is often financial planning. We regularly see plants in The Truckee Meadows treat IT as a surprise expense instead of a managed operating function. That leads to deferred firewall renewals, aging servers, unsupported workstations, inconsistent patching, and backup systems that exist on paper but have not been tested under production pressure.
The financial roadmap matters because manufacturing systems are interconnected. File shares support purchasing, production schedules, quality records, shipping documents, and vendor communication. Once one weak point is exploited, the disruption moves quickly. A structured managed cybersecurity program in Northern Nevada helps reduce that exposure by tying security controls, lifecycle planning, and monitoring to actual business risk instead of waiting for a crisis. In cases like Bryson’s, the encryption event is simply the point where years of delayed decisions become visible all at once.
- Deferred lifecycle planning: Older endpoints, expired warranties, and postponed infrastructure upgrades create exploitable gaps that attackers and malware routinely use.
- Unbudgeted security controls: MFA hardening, EDR tuning, and log review often get delayed when there is no vCIO process guiding priorities.
- Production dependency: Manufacturing plants rely on shared files for work orders, inventory movement, and shipping, so even a short encryption event can stop output and delay billing.
- Local operational complexity: Multi-building layouts, older industrial spaces, and mixed ISP environments in Reno and Sparks can make weak segmentation and inconsistent visibility worse.
What Remediation Looks Like in Practical Terms
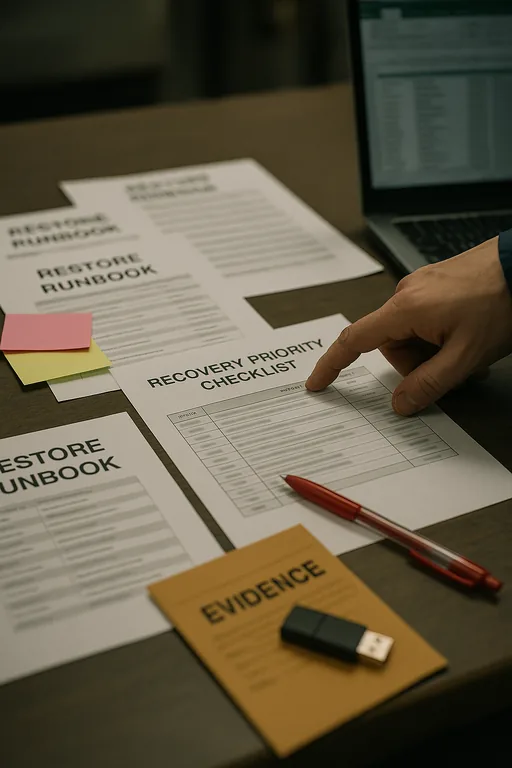
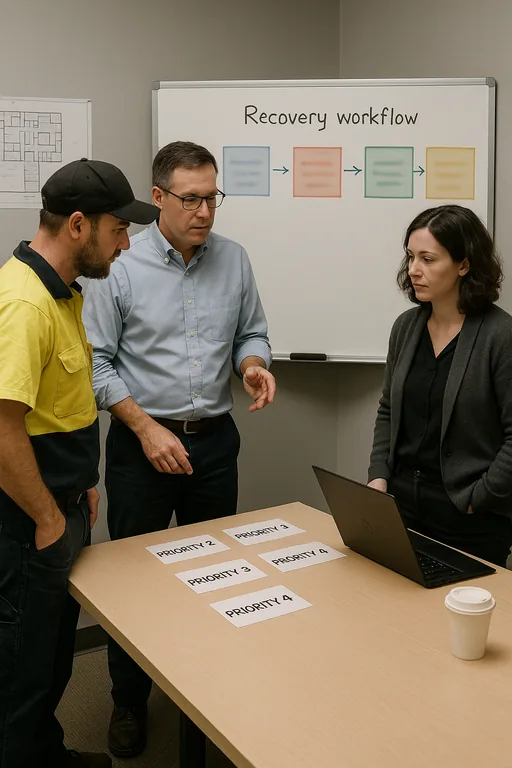
Remediation starts with containment, but it cannot end there. The first step is isolating affected endpoints, validating whether the encryption reached mapped shares or line-of-business systems, and confirming that identity systems were not also compromised. From there, we rebuild the environment around priorities: restore clean data, close the entry point, and remove the budget uncertainty that allowed the weakness to remain in place.
For manufacturing clients, that usually means replacing unsupported devices on a schedule, tightening admin rights, enforcing MFA, deploying tuned endpoint detection, and validating recovery from immutable or isolated backups. Just as important, we map recovery order to operations so production, shipping, and finance come back in the right sequence. Businesses that have not recently tested restores should review backup protection for Reno operations and compare their controls to practical guidance from CISA ransomware resources .
- Containment: Remove affected systems from the network, disable compromised accounts, and preserve logs before cleanup begins.
- Recovery validation: Restore from known-good backups and verify file integrity, permissions, and application dependencies before users reconnect.
- Segmentation: Separate office systems, production assets, and backup repositories with VLANs and access controls to limit lateral movement.
- Financial roadmap: Build a 12- to 36-month plan for endpoint refreshes, storage replacement, licensing, and security controls so risk reduction is budgeted instead of reactive.
Field Evidence: Recovery Planning Changes the Outcome
We have seen a clear difference between plants that only buy tools and plants that plan recovery around operations. In one Truckee Meadows manufacturing corridor case, the business had aging file storage, inconsistent patch cycles, and no tested order for restoring production support systems. After an encryption event, staff spent hours deciding what to bring back first while shipping and accounting waited on the same shared data.
After remediation, the environment was rebuilt with documented restore priorities, isolated backups, and a defined escalation path for plant leadership. That included formal disaster recovery planning for business continuity so the next outage would not turn into an improvised response. The result was a shorter recovery window, less confusion between departments, and a more predictable budget for future upgrades despite the normal operational pressures we see across Reno and Sparks industrial sites.
- Result: Recovery testing reduced projected file-service downtime from more than 10 hours to under 3 hours for priority systems, while restoring production scheduling and shipping access in the correct sequence.
Financial Roadmap Controls for Encrypted File Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.
Local Support in The Truckee Meadows
Manufacturing businesses in Reno, Sparks, and nearby industrial corridors often need fast onsite coordination when file access fails, especially when production paperwork, shipping records, and accounting systems depend on the same shared storage. From our Reno office, the Wyoming Avenue area is typically about 11 minutes away, which matters when containment, recovery sequencing, and executive decision-making all need to happen quickly.
Financial Roadmap Remediation Has to Be Operational, Not Reactive
Encrypted files in a manufacturing plant are rarely just a malware problem. More often, they reflect years of delayed refreshes, unclear ownership, and security controls that were treated as optional until operations were interrupted. The right response is not only to restore data, but to correct the planning model that allowed the environment to become fragile.
For businesses in The Truckee Meadows, that means aligning cybersecurity, backups, recovery order, and hardware lifecycle decisions to production risk and budget reality. When those pieces are planned together, downtime becomes easier to contain, recovery becomes more predictable, and leadership can make technology decisions before the next disruption forces the issue.

