Sparks Manufacturing Risk
The outage or lockout is usually the last symptom to appear, not the first. Surprise spending, delayed upgrades, and aging infrastructure create weak points that can disrupt proactive device and endpoint management and put budget control, resilience, and uptime at risk. Reducing that risk starts with planning upgrades deliberately and aligning IT decisions to business risk.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Financial Roadmap Gaps Turn Into Encrypted Files
When a manufacturing plant in Sparks ends up with encrypted files, the immediate cause may be malware, credential abuse, or an unpatched endpoint. The deeper cause is often financial planning that treats IT as a surprise expense instead of an operating system for the business. In practice, that means aging PCs stay in service too long, unsupported operating systems remain on the floor, backup appliances are not tested on schedule, and security tooling gets added unevenly. By the time production users notice a lockout, the organization has usually been carrying technical debt for months or years.
We see this pattern across Northern Nevada facilities where uptime matters and margins are tied to throughput. Plants in Sparks and Reno often depend on a mix of office workstations, shared file repositories, line-of-business applications, label printers, and vendor remote access. If those endpoints are not governed through structured proactive device and endpoint management in Northern Nevada , small budget deferrals can quietly become major operational exposure. That is why the financial roadmap matters: it connects refresh timing, security controls, and business risk before the incident forces the decision. In cases like Lilly’s, the encryption event is simply the point where deferred planning becomes visible.
- Aging endpoints: Older workstations and laptops often miss current security baselines, run unsupported software, or cannot support modern endpoint detection tools reliably.
- Unplanned capital spending: When replacement cycles are not budgeted, emergency purchases happen after failure instead of before risk increases.
- Flat file dependencies: Manufacturing teams frequently rely on shared folders for scheduling, quality records, and shipping documents, making one compromised file system a broad operational problem.
- Inconsistent patching: Plants with mixed devices, vendor software, and limited maintenance windows often delay updates until a vulnerability is already being exploited.
- Weak governance: Without a vCIO-level roadmap, leadership sees isolated invoices instead of a coordinated plan tied to uptime, resilience, and ROI.
How To Reduce Encryption Risk With Planned Controls
The fix is not just buying a new firewall or replacing one server. The practical answer is to build a staged roadmap that prioritizes the systems most likely to interrupt production, billing, and shipping if they fail. That starts with an asset inventory, lifecycle review, patch status validation, backup recovery testing, and a ranking of endpoints by business criticality. From there, leadership can budget refreshes and security improvements in a sequence that supports operations instead of reacting to emergencies.
For manufacturers, we typically recommend combining endpoint visibility, tested recovery procedures, and layered security oversight. That often includes EDR deployment, MFA hardening for remote access, network segmentation between office and production-support systems, and documented response playbooks. Businesses that need stronger containment and monitoring usually benefit from managed cybersecurity programs for manufacturing operations aligned to practical guidance from CISA ransomware prevention resources . The goal is not theoretical compliance. It is keeping file access, scheduling, and plant administration available when a device fails or an attack attempt lands.
- Lifecycle planning: Set replacement windows for endpoints, switches, servers, and backup hardware before supportability becomes a risk.
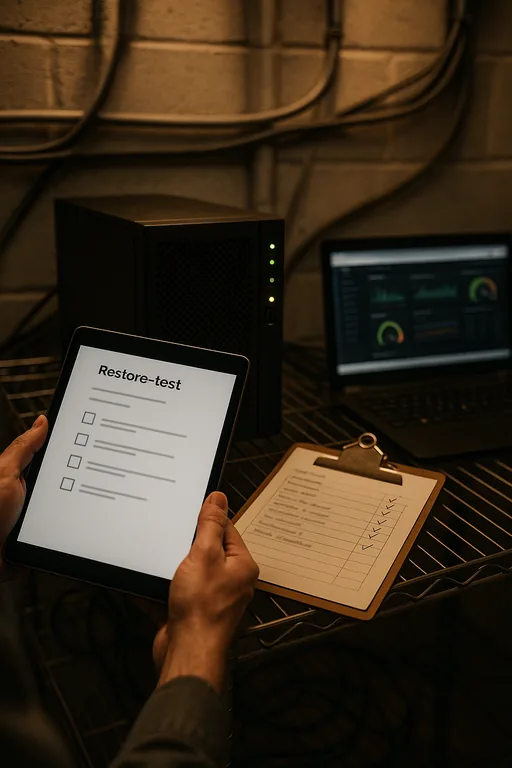
- Backup validation: Test file-level and full-system restores on a schedule so encrypted data does not become a recovery surprise.
- EDR and alerting: Deploy endpoint detection with centralized monitoring to catch suspicious encryption behavior early.
- MFA hardening: Require multifactor authentication for email, VPN, admin access, and vendor remote sessions.
- Segmentation: Separate production-support devices, office systems, and guest or vendor access to limit lateral movement.
Field Evidence: From Surprise Expense To Controlled Recovery
In one Northern Nevada industrial corridor, a plant operating near major freight routes had built up several years of deferred endpoint replacement because every quarter brought a more urgent spend request. Before remediation, the environment included aging Windows workstations, inconsistent local admin controls, and backups that existed on paper but had not been fully restore-tested. After a file encryption event disrupted scheduling and document access, the business shifted to a phased roadmap with asset prioritization, endpoint standardization, and recovery testing tied to budget cycles.
The result was not just better security posture. It was better operational predictability. Instead of emergency purchases and unplanned downtime, leadership had a defined refresh schedule, clearer reporting, and fewer interruptions during production weeks affected by vendor deliveries, staffing changes, and weather-related logistics common around Sparks and the broader Reno market. For organizations with audit obligations or customer security requirements, this is also where compliance-focused IT management becomes useful, because financial planning and risk management need to support each other.
- Result: Recovery testing improved restore confidence, endpoint standardization reduced unsupported devices by 70 percent, and unplanned IT spend dropped over the next two budget cycles.
Reference Points For Manufacturing IT Financial Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Proactive Device And Endpoint Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada
We regularly support organizations across the Reno-Sparks market where manufacturing, logistics, and office operations depend on stable endpoint performance and predictable response times. From our Reno office, the route to the destination noted here is typically about 14 minutes under normal conditions, which matters when a file lockout or endpoint failure is affecting scheduling, shipping, or production administration.
Budget Discipline Is Part Of Ransomware Prevention
Encrypted files in a Sparks manufacturing environment are rarely just a security problem. They are usually the result of delayed refresh decisions, uneven endpoint standards, and no clear financial roadmap for keeping critical systems supportable. When leadership budgets IT as a planned operating function instead of a series of emergency purchases, resilience improves and downtime becomes easier to prevent.
The practical takeaway is straightforward: identify the systems that would interrupt production first, assign replacement and recovery priorities, and connect those decisions to business risk. That approach supports uptime, keeps spending more predictable, and reduces the chance that one compromised endpoint turns into a plant-wide disruption.

