Reno Files Encrypted
Problems like this tend to stay hidden until something important breaks. For manufacturing plants in South Meadows, that often means encrypted files, avoidable delays, or a bigger recovery burden than expected. The best response is standardizing how new users, devices, and systems are brought online.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Often Point to a Scalability Ceiling
When a manufacturing plant in South Meadows starts seeing encrypted files, the immediate concern is containment and recovery. The larger issue is usually capacity and process discipline. We often find that growth came first, while account provisioning, endpoint standards, access controls, and storage architecture lagged behind. That is the scalability ceiling gap: the business added people, devices, vendors, and production dependencies faster than IT controls were expanded to support them.
In practical terms, that means a new hire may receive broad file access, a shared workstation may not be fully hardened, or a line-of-business system may still depend on an aging file share with weak segmentation. Once one endpoint is compromised, the damage spreads faster in flat environments. Businesses trying to secure business systems from ransomware need more than antivirus. They need standardized onboarding, role-based access, monitored endpoints, and clear separation between office systems, production support systems, and shared storage. That is where Derek’s situation becomes familiar across South Meadows and the broader Reno industrial corridor.
- Identity sprawl: New users and temporary access exceptions accumulate over time, making it easier for compromised credentials to reach shared folders and critical systems.
- Unmanaged endpoint growth: Added laptops, plant-floor terminals, and remote access devices often outpace patching, EDR coverage, and policy enforcement.
- Flat network design: If file servers, user devices, and operational support systems sit on the same broad network, encryption events move farther than they should.
- Legacy file dependency: Older shares and mapped drives remain common in manufacturing, especially where scheduling, inventory, and QA documents are still handled through shared folders.
How to Fix the Gap Before Growth Causes Another Outage
The right response is not just restoring files. It is rebuilding the operating model around controlled growth. We typically start by validating the scope of encryption, isolating affected endpoints, reviewing identity activity, and confirming whether backups are both intact and restorable. From there, the work shifts to standardization: every new user, workstation, mobile device, and shared application needs a defined onboarding path with security controls applied by default.
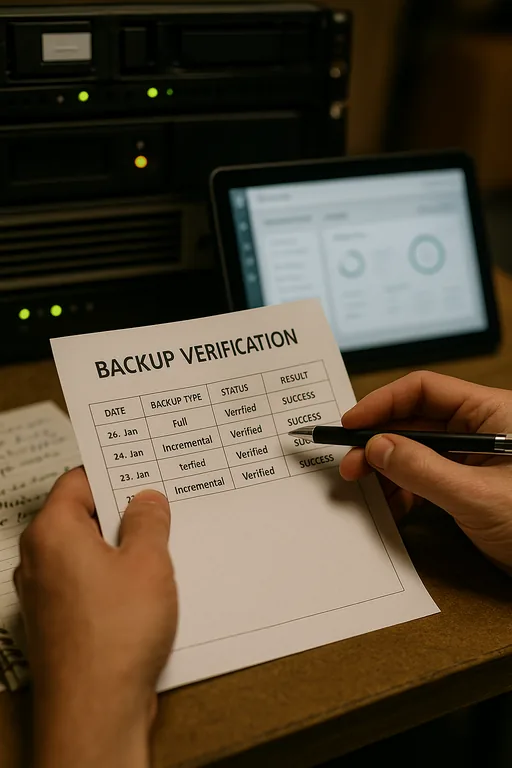
For manufacturing environments, that usually includes network segmentation, MFA hardening, EDR deployment, administrative privilege review, and backup validation across both local and cloud systems. It also means tightening server roles and storage access through structured server and hybrid infrastructure management so file services do not become a weak point as headcount grows. CISA’s guidance on ransomware prevention and recovery aligns closely with what works in the field: reduce lateral movement, limit privilege, and test recovery before an incident forces the issue.
- Standardized onboarding: Build one checklist for users, devices, MFA, endpoint protection, file permissions, and logging before access is granted.
- VLAN segmentation: Separate office users, production support devices, guest access, and server resources to reduce spread during an encryption event.
- Backup validation: Test restore points for file shares, ERP support systems, and critical departmental data on a scheduled basis.
- Privilege reduction: Remove local admin rights where possible and review service accounts, shared credentials, and inherited permissions.
Field Evidence: Growth Pressure in a South Reno Production Environment
We worked through a similar pattern with a growing operation serving customers across Reno and Sparks. Before remediation, the environment had added staff quickly, expanded shared storage, and introduced cloud collaboration without fully aligning permissions or monitoring. The result was inconsistent access, duplicate data locations, and a higher chance that one compromised endpoint could affect multiple departments.
After tightening onboarding standards, segmenting file access, validating backups, and cleaning up Microsoft 365 and shared storage through cloud and Microsoft environment management , the environment became much easier to operate. Instead of relying on ad hoc fixes, supervisors had predictable access, IT had clearer alerting, and recovery paths were documented. In Northern Nevada, where weather events, carrier interruptions, and multi-site coordination already create enough friction, that operational discipline matters.
- Result: File access incidents dropped, restore confidence improved, and the business reduced unplanned downtime during user growth and system changes.
Reference Points for Preventing File Encryption During Growth
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Services and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in South Meadows, Reno, and Northern Nevada
Reno Computer Services supports businesses throughout Reno, including South Meadows manufacturing and operations-heavy environments where response time, recovery planning, and practical system standardization matter. From our Ryland Street office, the route to the Lakeridge area is typically about 13 minutes, which helps when a file access issue, outage, or security event needs local hands and direct coordination.
Standardization Has to Happen Before the Next Growth Step
Encrypted files in a South Meadows manufacturing environment are rarely just a one-time technical malfunction. More often, they expose a business that added users, devices, and shared systems faster than its controls, segmentation, and recovery processes could keep up. If the environment is already near its operational ceiling, one compromised endpoint or one bad permission set can create a much larger interruption than expected.
The practical takeaway is straightforward: standardize onboarding, reduce unnecessary access, validate backups, and align infrastructure with the next phase of hiring before that hiring happens. That approach lowers recovery burden, protects production support workflows, and gives leadership a clearer path to scale without crashing into preventable downtime.

