Reno’s Secure Plant Audit
Seeing encrypted files is often the visible symptom of untested backups, not the root problem itself. In manufacturing plants across Reno, issues like failed restore tests, missing dependencies, and an unclear recovery order can quietly undermine regulatory compliance support until work stops or risk spikes. The fix usually starts with validating backups regularly and proving recovery before a real outage.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Usually Mean the Resilience Test Failed
When a Reno manufacturing plant reports encrypted files, the first question is not only whether malware was involved. The more important question is whether recovery has ever been proven end to end. A backup can exist for months and still fail when the business actually needs it. We see this most often when file servers are copied successfully, but the plant has never tested whether permissions, ERP connectors, scan stations, label printers, quality records, and line-of-business databases can all come back in the right order.
That is the core of the resilience test. A backup is just a copy. Business continuity is the ability to keep shipping, receiving, documenting, and meeting audit expectations while systems are under stress. For plants that depend on regulatory compliance support in Reno , encrypted files can quickly become a documentation problem as much as an IT problem. If production records, maintenance logs, calibration files, or batch documentation are unavailable, the outage can affect traceability, customer commitments, and internal control evidence. That is why the visible symptom matters less than the unproven recovery process behind it. In cases like Shirley’s, the file issue is often only the first sign that recovery sequencing was never operationally validated.
- Restore dependency gaps: Backups may capture data, but they often miss mapped drives, service accounts, application paths, SQL dependencies, or permission inheritance needed to make restored systems usable under plant conditions.
- Recovery order confusion: If teams do not know whether to restore domain services, storage, ERP, file shares, or workstation access first, downtime expands while staff improvise.
- Compliance exposure: Manufacturing environments with retention, traceability, or audit obligations can face reporting gaps when encrypted files interrupt controlled records.
- Operational bottlenecks: In Northern Nevada facilities, one unavailable server can stop scheduling, receiving, QA review, and shipping labels across multiple departments at once.
How to Fix the Backup Problem Before the Next Outage
The practical fix is to move from backup completion reports to recovery proof. That means selecting critical systems, documenting dependencies, and running scheduled restore tests that confirm the business can actually function after an incident. For manufacturing operations, we typically start with file shares, ERP or MRP systems, authentication, print services, and any workstation or scanner workflows tied to production or shipping. The goal is not just to recover data, but to restore usable operations within a defined timeframe.
That work usually sits inside broader network server and cloud management because backup success depends on storage health, identity services, virtualization, and alerting. It also helps to align the recovery process with practical guidance from CISA’s ransomware resilience guidance , especially around offline copies, tested recovery, and incident response roles. Plants with multiple VLANs, remote access, and mixed legacy equipment should also verify that backup traffic, restore bandwidth, and authentication controls are not creating hidden recovery delays.
- Restore testing cadence: Run quarterly recovery tests for critical systems and document actual recovery time, missing dependencies, and business impact.
- Recovery runbooks: Define the exact order for restoring domain services, storage, applications, file shares, and user access so the team is not deciding under pressure.
- Immutable and offline copies: Keep at least one backup set protected from routine credential compromise and unauthorized deletion.
- MFA and privileged access review: Reduce the chance that an encryption event spreads through backup consoles, admin tools, or remote access platforms.
- Alerting and validation: Monitor failed jobs, repository health, storage capacity, and test restores instead of relying on green checkmarks alone.
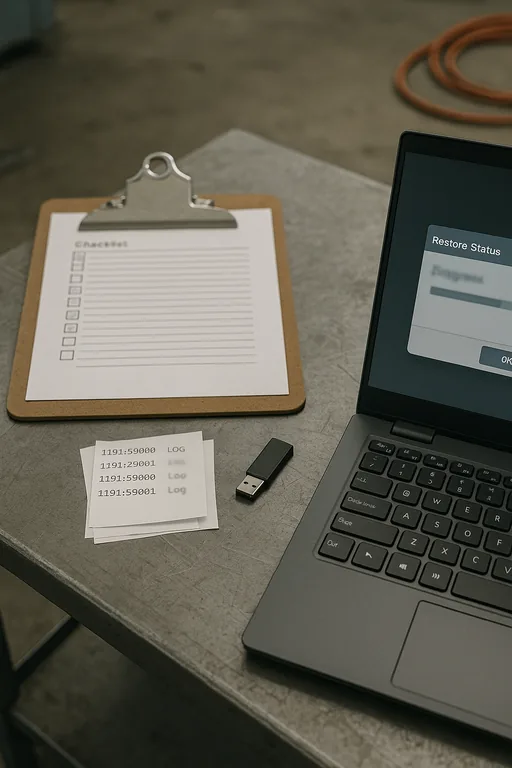
Field Evidence: The Resilience Test in a Reno Production Environment
We worked through a similar pattern with a Northern Nevada operation in an industrial corridor where file access looked recoverable on paper, but the first live test exposed missing service dependencies and broken permissions on restored shares. Before remediation, the site had backups completing nightly yet no verified sequence for bringing authentication, shared storage, and production-adjacent applications back online. During the test, staff could see restored data but could not use it in a way that supported normal work.
After documenting recovery order, validating application dependencies, and tightening IT systems for multi-location operations , the environment moved from theoretical backup coverage to measured recovery capability. The next test restored critical file access and supporting services within the planned window, and supervisors had a clear escalation path instead of ad hoc troubleshooting. In a region where weather events, carrier issues, and distance between sites can complicate response, that difference matters.
- Result: Verified recovery time for critical file and application services dropped from an unproven multi-hour estimate to a documented 95-minute restore sequence with usable access confirmed by operations staff.
Resilience Test Audit Reference Points
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Regulatory Compliance Support and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Manufacturing and compliance-driven organizations in Reno often need fast, practical support that accounts for travel time, facility access, and the difference between a backup report and an actual recovery. From downtown Reno to Longley Lane and the broader Truckee Meadows area, local response matters when encrypted files affect production records, shared storage, or audit-sensitive documentation.
What the Audit Should Confirm
If files are encrypted, the immediate event matters, but the larger business question is whether recovery has been tested under real operating conditions. In Reno manufacturing environments, that means confirming not only that data exists in backup storage, but that the plant can restore permissions, dependencies, application access, and documentation workflows in the right order.
The resilience test audit should produce evidence, not assumptions. When backups are validated, recovery steps are documented, and infrastructure dependencies are understood, encrypted files become a contained incident instead of a prolonged operational failure.

