Reno’s Hidden Threat
Seeing encrypted files is often the visible symptom of hidden threats, not the root problem itself. In manufacturing plants across Reno, issues like stolen credentials, MFA gaps, and weak monitoring can quietly undermine technology advisory and assessment until work stops or risk spikes. The fix usually starts with hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Encrypted Files Usually Point to a Larger Identity and Visibility Failure
When a Reno manufacturing plant reports encrypted files, the immediate question is usually whether backups are intact. That matters, but it is not the first issue to solve. In many incidents, the real failure is that an attacker did not need to break through the firewall at all. They logged in with a valid account, moved through normal business tools, and stayed below the threshold of what many plants are actively watching. That is the invisible threat gap.
We see this most often where production, office, and vendor access have grown over time without a full review of identity controls. A single compromised Microsoft 365 account, remote access credential, or unmanaged endpoint can give an attacker enough foothold to stage encryption later. That is why technology advisory and assessment in Reno has to go beyond hardware inventories and basic patch status. It needs to examine who can log in, from where, with what protections, and what abnormal behavior is being missed. In cases like Nuria’s, the encrypted files were only the visible end of a longer access problem.
Manufacturing environments add complexity because file shares, ERP systems, label printers, engineering workstations, and line-of-business PCs often depend on each other. If one account is overprivileged or one endpoint is not monitored, the impact can spread from office operations into production timing, shipping accuracy, and vendor coordination. In Northern Nevada, where many plants coordinate across Reno, Sparks, and Carson City, even a short interruption can ripple into missed pickups, delayed receiving, or overtime labor.
- Stolen credentials: Attackers increasingly use valid usernames and passwords to access cloud apps, VPNs, and file systems in ways that look routine unless login patterns, device trust, and privilege use are being reviewed.
- MFA gaps: Multi-factor authentication may exist for some users but not for legacy apps, service accounts, remote tools, or administrative roles, leaving a practical path around the control.
- Weak monitoring: Many plants collect logs but do not correlate impossible travel, unusual sign-in locations, mass file changes, or after-hours privilege escalation into actionable alerts.
- Flat access paths: Shared credentials, broad file permissions, and limited segmentation allow one compromised account to reach more systems than operations teams realize.
What Practical Remediation Looks Like in a Manufacturing Environment
The fix is not just restoring files. It starts with confirming how the attacker authenticated, what systems they touched, and whether persistence still exists. In a manufacturing plant, that means reviewing identity logs, endpoint telemetry, remote access tools, administrative groups, and file activity together rather than in isolation. We typically prioritize account containment, forced credential resets, token revocation, endpoint isolation, and validation of clean backups before any broad restoration begins.
From there, the goal is to reduce the chance of recurrence. Plants with mixed office and production systems usually benefit from tighter endpoint oversight, especially where shared workstations, engineering laptops, and remote vendor access are involved. Structured endpoint management for manufacturing operations helps close those blind spots by enforcing patching, EDR coverage, device health checks, and alerting consistency. For identity hardening and ransomware resilience, the guidance from CISA’s ransomware resources is practical and aligns well with what works in the field.
- Identity hardening: Enforce MFA across all user and admin accounts, remove legacy authentication where possible, and review conditional access rules for location, device compliance, and risky sign-in behavior.
- EDR deployment: Ensure every workstation and server, including less-visible production support systems, reports into a monitored endpoint detection platform with isolation capability.
- Privilege reduction: Remove standing local admin rights, separate admin accounts from daily user accounts, and tighten access to shared folders, ERP exports, and finance-related data.
- Backup validation: Test restore points regularly, confirm immutable or offline recovery options, and verify that backup credentials are not exposed to the same identity plane as production users.
- Alert tuning: Create alerts for impossible travel, mass file rename or encryption behavior, unusual PowerShell use, and sign-ins from unmanaged devices.
Field Evidence: Before-and-After Recovery in a Reno Production Workflow
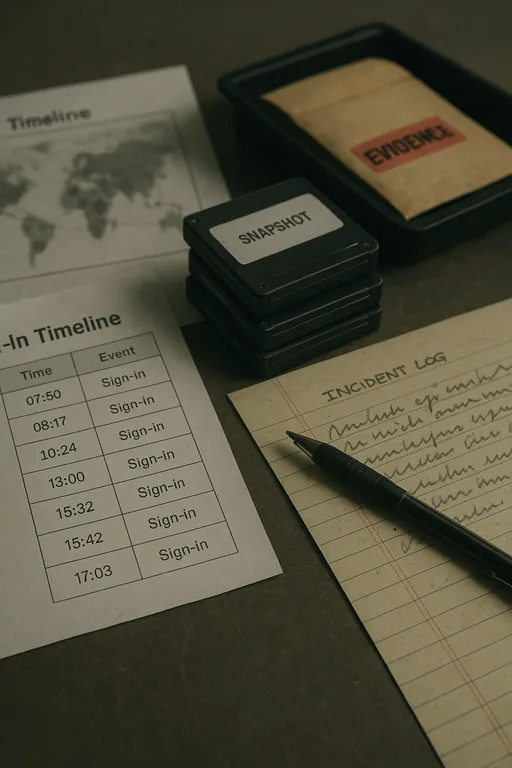
In one Northern Nevada manufacturing environment, the initial condition was familiar: shared folders were intermittently inaccessible, several files had changed extensions, and supervisors assumed the issue was limited to a single server. Review of sign-in history showed otherwise. A compromised user account had authenticated from an unusual location, accessed cloud resources first, then reached on-premise file shares through a trusted path. The plant also had inconsistent endpoint visibility on a few older floor-adjacent systems.
After containment, the recovery plan focused on restoring clean data, revoking sessions, tightening access, and standardizing oversight across office and production endpoints. The business also improved IT systems for multi-location operations so alerts, account reviews, and recovery procedures were handled consistently across sites. That mattered because the company coordinated shipping between Reno and Sparks and could not afford repeated uncertainty around file integrity.
- Result: File restoration was completed from verified backups, unauthorized sign-ins were blocked, and the business reduced recovery time for future account-based incidents from multiple business days to under 6 hours.
Reference Table: Hidden Threat Controls for Manufacturing Plants
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Technology Advisory And Assessment and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Manufacturing businesses in Reno often need support that can connect office systems, plant-floor endpoints, and recovery planning without losing sight of local logistics. From our Ryland Street office, the route to the Huffaker area is typically about 16 minutes depending on traffic, which matters when a file encryption event is disrupting scheduling, shipping, or production coordination.
Closing the Invisible Threat Gap Before the Next Outage
Encrypted files in a Reno manufacturing plant are rarely just a storage problem. More often, they are evidence that identity controls, endpoint visibility, and operational monitoring have drifted apart. If the response stops at file recovery, the same access path may still be available to the next attacker.
The practical takeaway is straightforward: verify how access was gained, tighten authentication, monitor endpoints consistently, and make sure recovery procedures are tested under real operating conditions. That approach reduces downtime, limits repeat incidents, and gives plant leadership a clearer view of where risk actually sits.

