Reno Data Breach
This kind of issue rarely appears all at once. For manufacturing plants in Northern Nevada, it usually builds through unclear ownership, overlapping tools, and fragmented support and then surfaces as encrypted files, slower recovery, or higher exposure. A more reliable setup starts with clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Where Vendor Chaos Turns Into Encrypted Files
When files get encrypted in a manufacturing environment, the immediate question is usually whether the event started with ransomware, a compromised account, or a failed sync platform. In practice, the larger issue is often ownership. We see plants across Reno, Sparks, Carson City, and the broader Northern Nevada corridor running email with one provider, endpoint protection with another, backups with a third, and line-of-business software under a separate reseller agreement. Once something breaks, nobody has full authority to isolate the threat, validate recovery points, and restore operations in the right order.
That is why this incident fits the pattern behind The Vendor Chaos. The office manager ends up acting as dispatcher between internet, phones, software, and hardware vendors even though that role should never carry incident command. In manufacturing, that delay affects quoting, purchasing, shipping, production scheduling, and quality records very quickly. Plants dealing with fragmented account control and inconsistent permissions usually need tighter identity email and user security in Northern Nevada so compromised credentials do not become the path to file encryption or lateral access.
The technical failure is rarely one single bad click. More often it is a chain: weak MFA enforcement, stale admin accounts, shared credentials for vendor access, backup jobs nobody tests, and unclear escalation when alerts start firing. In Tommy’s case, the business consequence was not just unreadable files. It was lost production visibility, delayed approvals, and staff standing still while multiple vendors argued over who owned the problem.
- Technical factor: Fragmented vendor ownership leaves identity controls, file permissions, backup validation, and incident response split across too many parties, which slows containment and increases downtime.
- Operational detail: Manufacturing plants depend on fast access to drawings, schedules, inventory records, and shared documents; once those are encrypted, supervisors often revert to manual processes that create delays and data inconsistency.
- Local reality: Northern Nevada facilities with multiple buildings, mixed legacy equipment, and separate ISP or telecom contracts are especially vulnerable when no single team is accountable for escalation.
How To Stabilize Ownership And Recover Cleanly
The fix starts by assigning one accountable technical owner for identity, endpoint security, backup integrity, and vendor escalation. That does not mean replacing every outside provider. It means establishing a clear operating model: who can disable accounts, who can isolate endpoints, who approves restore decisions, who validates backup scope, and who communicates status to plant leadership. Businesses that keep adding tools without governance usually benefit from strategic IT leadership for multi-vendor operations so response decisions are made from a single plan instead of a conference call full of handoffs.
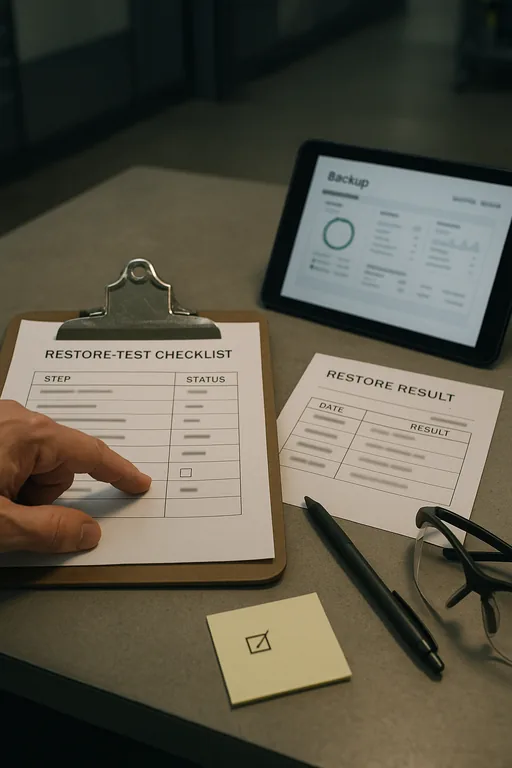
From a control standpoint, we typically recommend hardening Microsoft 365 identities, enforcing phishing-resistant MFA where practical, removing standing admin rights, segmenting production-adjacent systems from general office traffic, and validating backup recovery against real file sets rather than dashboard success messages. For manufacturing environments, recovery order matters: restore the systems that support scheduling, quality, and shipping first, then address lower-priority shared storage. The CISA ransomware guidance is a useful baseline because it emphasizes containment, backup validation, and role clarity rather than tool sprawl.
- Control step: Establish a written incident ownership matrix covering email, identity, endpoints, backups, firewall, and line-of-business vendors.
- Practical action: Enforce MFA hardening, remove dormant vendor accounts, deploy EDR with isolation capability, test backup restores quarterly, and document a single escalation path for after-hours manufacturing incidents.
- Control step: Review budget and lifecycle exposure before renewal cycles.
- Practical action: Use IT planning and budgeting for operational continuity to reduce overlapping tools, close unsupported gaps, and fund the controls that actually shorten recovery time.
Field Evidence: Multi-Vendor Manufacturing Recovery Near Reno
We worked through a similar pattern with a Northern Nevada operation managing office users, plant-floor supervisors, and outside vendors across separate systems. Before cleanup, the business had no confirmed backup testing, no consistent MFA enforcement, and no documented authority to shut off compromised access. During incidents, staff spent more time finding the right vendor than containing the problem.
After consolidating escalation ownership, validating restore points, tightening user access, and documenting recovery order by business function, the environment became much more predictable. That matters in local industrial corridors where weather events, carrier outages, and distance between facilities can already slow response if the process is not disciplined.
- Result: Recovery testing time dropped from nearly a full business day to under two hours, backup confidence improved through scheduled validation, and user lockout and access incidents were resolved through one escalation path instead of four separate vendor queues.
Reference Table: Controls That Reduce Vendor-Driven Encryption Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Identity Email And User Security and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Manufacturing incidents tied to vendor confusion often require both remote coordination and local follow-through. From our Reno office, the Southwest Vistas area is typically about 17 minutes away, which matters when a business needs onsite verification, vendor alignment, or a direct review of account ownership, backup status, and recovery priorities.
Why This Issue Keeps Repeating Until Ownership Is Fixed
Encrypted files in a manufacturing plant are often the visible symptom of a deeper operating problem. When identity, email, backups, endpoint security, and vendor access are split across too many parties without one accountable lead, response slows down and recovery becomes more expensive than it should be.
The practical takeaway is straightforward: define ownership before the next incident, test recovery before you need it, and make sure business leadership knows exactly who has authority to contain, restore, and communicate. That is how Northern Nevada manufacturers reduce downtime instead of managing chaos in the middle of it.

