Reno Encrypt Fix
This kind of issue rarely appears all at once. For manufacturing plants in Northern Nevada, it usually builds through poor safeguards, inconsistent records handling, and a slow response and then surfaces as encrypted files, slower recovery, or higher exposure. A more reliable setup starts with documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Become a Legal Liability
When a Northern Nevada manufacturing plant reports encrypted files, the immediate concern is usually production downtime. That is valid, but it is not the full issue. The legal liability starts when the business cannot show what data was affected, how long systems were exposed, whether sensitive customer or vendor information was involved, and what safeguards were in place before the incident. In Reno and Sparks, we often see this gap in plants that have grown faster than their documentation, access control, and response process.
The discussion is straightforward: if client data is lost or exposed, saying the team did not know is not a defense that holds much weight. Courts, insurers, and regulators tend to look for reasonable controls, documented response actions, and evidence that the business acted promptly. That is why structured business IT operations management in Northern Nevada matters. It connects endpoint security, file access, backup oversight, incident logging, and leadership decision-making into one operating model instead of a loose collection of tools. In cases like Edward’s, the real failure is rarely one bad click alone. It is usually a chain of weak permissions, incomplete logging, aging file shares, and no clear escalation path once encryption starts.
- Technical factor: Flat network access and inconsistent file-share permissions allow ransomware or unauthorized encryption activity to spread from one compromised endpoint into production folders, quality records, and customer documentation before anyone isolates the source.
- Operational factor: If supervisors, IT contacts, and plant leadership do not have a written incident workflow, valuable time is lost deciding who can shut down systems, who contacts legal counsel, and who validates whether reporting obligations apply.
- Business consequence: Delayed shipping, interrupted billing, and uncertainty around data exposure can create contract disputes, insurance friction, and avoidable legal review costs even after systems are restored.
Practical Remediation for Recovery, Reporting, and Containment
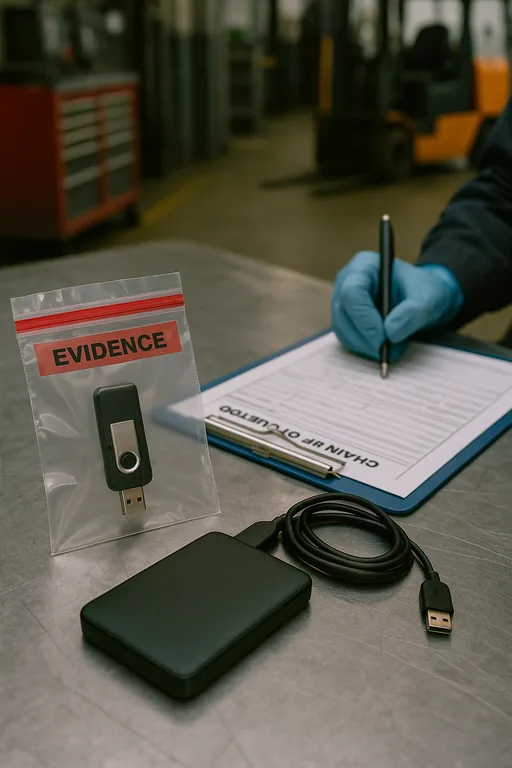
The fix is not just decrypting or restoring files. A defensible remediation plan starts with containment, evidence preservation, and restoration from known-good backups. We typically isolate affected endpoints, disable compromised accounts, review lateral movement, and verify whether the incident was limited to encryption or included data access and exfiltration. For manufacturers, we also check whether ERP exports, CAD files, shipping records, and quality documents were stored only on mapped drives without versioning or immutable backup protection.
From there, the plant needs documented controls that stand up operationally and legally. That includes tested backup compliance and continuity controls , multi-factor authentication for administrative access, segmented file access by department, and a written incident response process that includes legal and insurance notification steps. The CISA StopRansomware guidance is a useful baseline because it ties prevention, containment, and recovery into practical actions businesses can implement without overcomplicating the environment.
- Containment: Remove affected devices from the network immediately, revoke suspect credentials, and preserve logs before cleanup begins.
- Backup validation: Restore from tested recovery points, confirm file integrity, and document what data sets were recovered versus rebuilt manually.
- Access hardening: Apply MFA to privileged accounts, reduce shared credentials, and separate production, office, and vendor access where practical.
- Response governance: Define who approves shutdowns, who contacts counsel and cyber insurance, and how evidence and timelines are recorded.
Field Evidence: Airport Corridor Manufacturing Recovery
We worked through a similar pattern with a manufacturer operating near the airport and serving regional distribution routes into Reno, Carson City, and the Tahoe corridor. Before remediation, the environment depended on broad shared-drive access, inconsistent endpoint alerting, and backups that existed but had not been recently tested against a full file-share restoration. The business could restart some office work quickly, but production support records and shipping documentation remained unreliable for most of a day.
After the environment was rebuilt with segmented access, validated restore points, and clearer escalation procedures, the plant had a much shorter recovery path during later file corruption events. Just as important, leadership had the documentation needed to show what systems were affected, what data sets were restored, and what controls had been improved. That is where recovery programs built around verified restore readiness make a measurable difference for both operations and legal defensibility.
- Result: Recovery testing reduced file-share restoration time from most of a workday to under 2 hours for critical operational data, while incident documentation improved insurer and counsel review readiness.
Manufacturing File Encryption Risk Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Business It Operations Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Northern Nevada and Northern Nevada.

Local Support in Northern Nevada
From our Reno office, we regularly support manufacturers, logistics operators, and industrial businesses across the airport corridor, Sparks, Carson City, and surrounding Northern Nevada service areas. For plants dealing with encrypted files, the local advantage is not just travel time. It is knowing how to coordinate recovery around shift schedules, shipping deadlines, vendor access, and the practical realities of keeping operations moving while evidence is preserved and systems are restored.
Operational Takeaway for Manufacturing Leadership
Encrypted files in a manufacturing environment are not just an IT cleanup issue. They create production delays, documentation gaps, and legal questions about whether the business used reasonable safeguards and responded in a defensible way. In Northern Nevada, where many plants depend on tight shipping windows, shared operational records, and lean internal teams, those gaps become visible quickly.
The practical answer is disciplined operations: documented controls, tested recovery, segmented access, and a response process that includes technical, legal, and management decisions from the start. When those pieces are in place, a file encryption event is still disruptive, but it is far less likely to become a prolonged outage with avoidable liability attached.

