Reno Data Breach
What looks like a one-off issue is often tied to legacy tools. In construction firm environments, legacy systems, patchwork fixes, and hard-to-adopt tools can turn into efficiency, visibility, and growth long before anyone notices the warning signs. Closing those gaps early makes proactive device and endpoint management far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why the Innovation Wall Turns Into a Breach Problem
A data breach in a Washoe County construction firm rarely starts with a single dramatic failure. More often, it starts when older laptops, unsupported line-of-business software, aging firewalls, and shared credentials are kept in place because replacing them feels disruptive. That is the Innovation Wall: the point where old hardware and patchwork processes cannot safely support modern cloud platforms, AI-assisted workflows, mobile field access, or current security controls. Once a business hits that wall, visibility drops and risk rises at the same time.
We see this often in Reno and Sparks construction environments where office staff, estimators, superintendents, and field teams all need access to plans, email, accounting systems, and file shares from different locations. If one endpoint cannot run current protection tools, or if an old server is left in place because a specialty application still depends on it, the entire environment becomes harder to secure. That is why proactive device and endpoint management in Northern Nevada matters: it gives businesses a way to standardize patching, enforce endpoint controls, and identify aging assets before they become the weak point. In incidents like the one Carolina dealt with, the breach is usually the symptom; the real cause is unmanaged technical debt.
- Legacy endpoint exposure: Older workstations and specialty systems often cannot support current EDR agents, modern encryption standards, or reliable patch cycles, which leaves credential theft, malware execution, and lateral movement far easier than most firms realize.
- Patchwork access design: Shared folders, inherited permissions, and remote access exceptions built over several years create blind spots around who can reach estimating data, contracts, and financial records.
- Construction workflow pressure: When teams are focused on bids, change orders, and field deadlines, temporary workarounds tend to stay in place, especially across multi-site operations in Washoe County.
Practical Remediation That Prevents the Same Failure From Returning
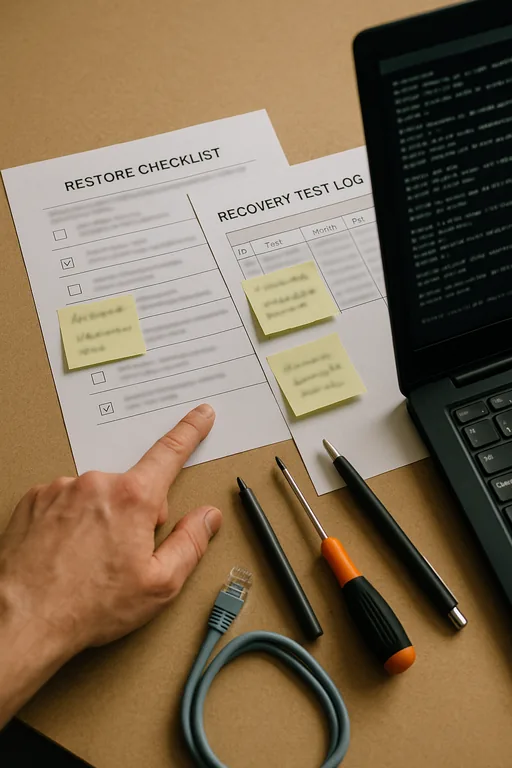
The fix is not just to clean the infected machine and move on. A durable response starts with asset review, operating system support validation, credential resets, log review, and confirmation of what data was exposed. From there, we typically segment older systems, remove unsupported endpoints from sensitive workflows, enforce MFA, and deploy endpoint detection and response across every managed device. Construction firms also need to review where project files live, how remote access is handled, and whether field users are relying on unmanaged personal devices.
Recovery planning matters just as much as prevention. If estimating files, accounting exports, or project documentation are encrypted or altered, the business needs tested rollback options, not assumptions. That is where backup and disaster recovery for Reno business operations becomes part of breach response, not a separate conversation. For practical guidance on reducing cyber risk and improving resilience, the CISA StopRansomware resource center remains one of the more useful operational references for small and midsize organizations.
- Endpoint standardization: Replace or isolate unsupported devices so every active workstation can run current security tooling, centralized patching, and policy enforcement.
- MFA hardening: Require phishing-resistant or app-based MFA for email, VPN, cloud file access, and administrator accounts.
- Network segmentation: Use VLAN separation and access controls so older specialty systems cannot freely communicate with finance, HR, or executive systems.
- Backup validation: Test file-level and system-level restores on a schedule, with documented recovery priorities for estimating, accounting, and project management data.
Field Evidence: Legacy Endpoints Blocking Modern Construction Operations
In one Northern Nevada case, a construction-related office corridor with a mix of warehouse, dispatch, and administrative staff was relying on several older desktops tied to an outdated application workflow. Before remediation, patch compliance was inconsistent, remote access logs were incomplete, and backups existed but had not been tested against a real file corruption event. After a structured cleanup, the environment was rebuilt around supported endpoints, tighter access policies, and documented recovery steps.
The practical change was immediate. Instead of reacting to recurring workstation issues and uncertain restore points, the firm had a clear inventory, current endpoint protection, and verified recovery copies for critical files through managed backup solutions for multi-location operations . That matters in Washoe County, where teams may be splitting time between Reno offices, Sparks yards, and active job sites with inconsistent connectivity and constant schedule pressure.
- Result: Patch compliance moved above 95 percent, restore testing confirmed recovery of key project files in under two hours, and unplanned endpoint-related downtime dropped noticeably over the following quarter.
Construction IT Risk Reference for Legacy Breach Conditions
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Proactive Device And Endpoint Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.

Local Support in Washoe County
Our office in Reno supports businesses across Washoe County that are trying to modernize without breaking critical workflows. For construction firms near south Reno, Sparks, and surrounding industrial corridors, the challenge is usually not just one bad device. It is the accumulation of old endpoints, inherited permissions, and recovery gaps that make a breach harder to contain. Local response matters because site access, travel time, and coordination with office and field teams all affect how quickly operations stabilize.
Modernization Has to Remove Risk, Not Just Add Tools
For construction firms in Washoe County, a data breach tied to legacy systems is usually a sign that the environment has outgrown its original design. Old hardware, unsupported applications, and years of exceptions create the Innovation Wall long before leadership sees it clearly. Once that wall is in place, every new cloud tool, remote workflow, or AI initiative becomes harder to adopt safely.
The practical takeaway is straightforward: inventory what is aging out, standardize endpoints, tighten access, and verify recovery before the next incident forces the issue. Businesses that do this well are not chasing every new platform. They are building an environment that can support growth without exposing operations, billing, and project data to avoidable failure.

