Truckee Data Breach
When a business is dealing with a data breach, the failure usually started earlier. Poor safeguards, inconsistent records handling, and a slow response can weaken regulatory compliance support over time and leave construction firms in The Truckee Meadows exposed when pressure hits. Addressing the problem means documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Where Legal Liability Usually Starts
A construction firm in The Truckee Meadows rarely gets into breach trouble because of one dramatic event. More often, the legal liability failure starts with ordinary operational gaps: shared credentials for field supervisors, untracked file transfers, inconsistent retention of HR and contract records, and no documented chain of response when sensitive data leaves the business. Once client data is lost, the issue is no longer just technical. It becomes a records, reporting, and accountability problem. In Reno, that matters because “we did not know” does not carry much weight once counsel, insurers, or regulators start asking what controls were in place.
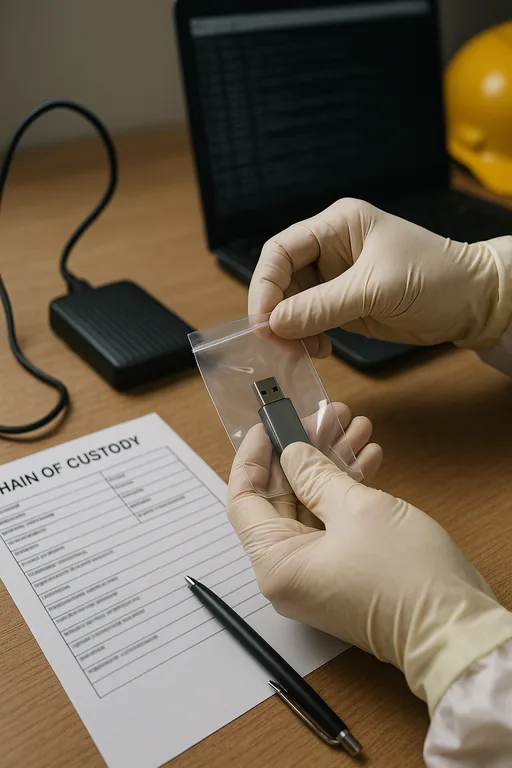
We typically find that firms with weak documentation also have weak escalation. That means the first few hours after discovery are spent figuring out who owns the problem instead of containing it. For companies that handle employee files, project financials, lien documentation, or customer payment information, structured regulatory compliance support in Northern Nevada helps establish what data exists, where it moves, and what must happen when exposure occurs. That is the point many firms miss until after an incident. Bruno’s situation is a good example: the breach itself was serious, but the larger failure was the absence of a documented process for access control, evidence preservation, and notification review.
- Records handling: Sensitive files often move between accounting, project management, and field operations without a consistent retention policy, access log, or approval trail.
- Email and identity controls: A single compromised mailbox can expose contracts, payroll attachments, and vendor communications if MFA, conditional access, and alerting are not enforced.
- Response ownership: When no one is assigned to legal, technical, and operational coordination, the first response becomes fragmented and delays containment.
- Construction workflow pressure: Bid deadlines, subcontractor coordination, and multi-site communication across Reno, Sparks, and Carson City can push security steps aside unless they are built into daily operations.
How Construction Firms Reduce Breach Exposure and Response Failure
The practical fix is not a single tool. It is a controlled operating model. Start by identifying regulated and sensitive data sets, then map who can access them, where they are stored, and how they leave the organization. From there, tighten identity controls, standardize incident response steps, and require evidence preservation from the first sign of compromise. Firms that lack internal ownership usually benefit from strategic IT leadership for compliance-focused operations so legal, insurance, and technical decisions are coordinated instead of improvised.
We also recommend aligning breach response with a recognized framework so the business can show reasonable care and repeatable process. The CISA ransomware and incident response guidance is useful because it translates security controls into operational actions: isolate affected systems, preserve logs, validate backups, reset credentials, and document the timeline. For construction firms, that should be paired with role-based access, secure document sharing, tested backup recovery, and a notification checklist reviewed with counsel before an event occurs.
- Identity hardening: Enforce MFA, disable stale accounts, and restrict admin rights so one compromised user does not expose estimating, payroll, and project systems.
- Documented incident workflow: Define who handles containment, insurer contact, legal review, client communication, and evidence collection within the first hour.
- Backup validation: Test file and system recovery on a schedule so restoration is measured, not assumed.
- Secure file controls: Move contracts, HR records, and financial documents into managed repositories with permissions, retention rules, and audit visibility.
Field Evidence: From Untracked Exposure to Controlled Response
We worked through a similar pattern with a Northern Nevada contractor managing office staff in Reno and crews moving between Sparks yards and job sites near USA Parkway. Before remediation, the company had shared inbox access, inconsistent offboarding, and no tested breach checklist. After tightening identity controls, documenting response steps, and reviewing capital priorities through IT planning and budgeting for growing operations , the business could isolate affected accounts quickly, preserve logs for review, and restore access without shutting down the full office.
- Result: Initial containment time dropped from most of a business day to under 90 minutes, and documented recovery steps reduced avoidable downtime during the next security event review.
Construction Breach Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Regulatory Compliance Support and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
Our office in Reno supports businesses across The Truckee Meadows, including contractors working between downtown Reno, Commercial Row, Sparks, and surrounding industrial corridors. For firms dealing with breach exposure, response timing matters. The route below reflects the local service reality for organizations operating near Commercial Row and needing practical support close to the work.
What Construction Firms Need to Take Seriously
A data breach at a construction firm is usually the visible result of earlier control failures. Weak access management, inconsistent record handling, and an unstructured response process create the legal liability long before the incident is discovered. In The Truckee Meadows, where firms move quickly across bids, payroll, project files, and subcontractor coordination, those gaps can turn a manageable event into a reporting and recovery problem.
The practical takeaway is straightforward: know what sensitive data you hold, limit who can reach it, document your response steps, and test recovery before you need it. That is how firms reduce downtime, support defensible decisions, and avoid making legal exposure worse after the fact.

