Reno Data Breach Fix
Problems like this tend to stay hidden until something important breaks. For construction firms in South Meadows, that often means a data breach, avoidable delays, or a bigger recovery burden than expected. The best response is simplifying the stack and making modernization practical.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Innovation Wall Turns Into a Breach Problem
A data breach in a South Meadows construction firm usually is not caused by one bad click alone. More often, we find a stack that has stopped evolving: old servers, unsupported network gear, weak remote access, fragmented file shares, and backup jobs that report success without proving recoverability. That is the innovation wall. The business wants to use cloud collaboration, mobile field reporting, AI-assisted estimating, and faster document flow, but the underlying hardware and operating model are still built for 2019.
For construction operations, that gap matters quickly. Estimators need current drawings, project managers need version control, accounting needs clean job-cost data, and field supervisors need dependable access from trailers, job sites, and mobile devices. When the core environment is outdated, every modernization step gets bolted onto unstable infrastructure. That is how a breach becomes more than a security event. It becomes a scheduling issue, a billing issue, and a recovery issue. In cases like Harold saw, firms often need managed backup solutions in Reno because the real problem is not only intrusion risk, but whether the business can restore current data without losing days of work.
- Legacy infrastructure: Older servers, firewall appliances, and line-of-business systems often cannot support current encryption standards, modern endpoint controls, or reliable cloud synchronization, which leaves project files and operational data exposed.
- Remote access sprawl: Construction firms commonly rely on a mix of VPNs, RDP exceptions, personal devices, and vendor access paths that were added over time without consistent review.
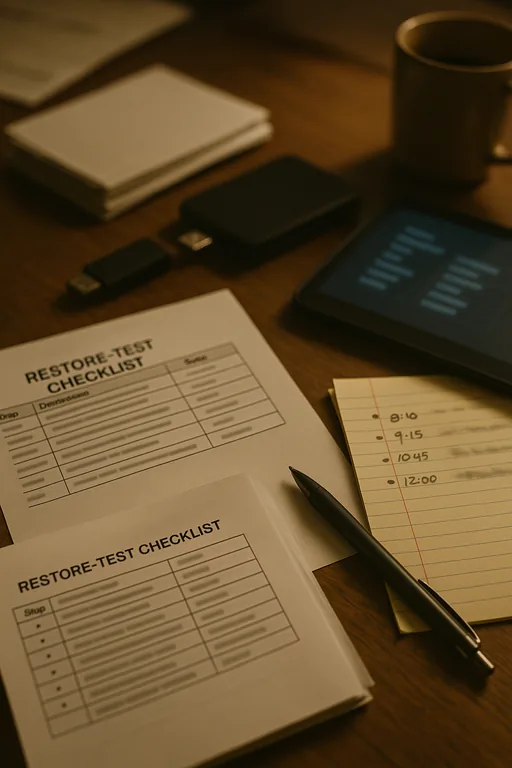
- Unverified backups: Backup completion alerts are not the same as tested recovery. We regularly see firms with backup jobs running, but no recent proof that drawings, accounting data, and shared folders can be restored cleanly.
- Operational dependency on stale systems: Once crews, office staff, and subcontractor coordination all depend on one aging file platform, a single failure can stop submittals, RFIs, payroll support, and invoicing at the same time.
Practical Remediation for Construction Environments
The fix is usually not a single product. It is a controlled simplification effort. We start by identifying what must stay on-premises, what should move to a supported cloud platform, and what should be retired entirely. For construction firms, that often means replacing exposed remote access methods, standardizing identity controls, separating critical project data from general office traffic, and validating that backups can restore both file shares and business applications in a usable timeframe.
That work is more effective when it is tied to a formal roadmap instead of ad hoc upgrades. A structured approach such as IT strategy engagements in Northern Nevada helps prioritize which systems are creating the most operational drag and breach exposure. For security baselines, the CISA ransomware guidance is a practical reference because it aligns recovery planning, access control, and backup discipline instead of treating them as separate projects.
- Identity hardening: Enforce MFA for email, VPN, cloud storage, and admin access; remove dormant accounts and vendor credentials that no longer serve an active project need.
- Backup validation: Test restores on a schedule, confirm retention windows, and verify that project folders, accounting databases, and shared permissions recover correctly.
- Endpoint and server control: Deploy EDR, patch unsupported systems out of service, and isolate legacy applications that cannot yet be replaced.
- Network segmentation: Separate office users, servers, guest devices, and jobsite-connected equipment so one compromised endpoint does not expose the full environment.
- Operational oversight: Establish alerting, change control, and documented escalation through IT systems for multi-location operations so outages and suspicious activity are handled before they spread.
Field Evidence: South Meadows File Access Recovery After Legacy Server Failure
We worked through a similar pattern for a Northern Nevada business operating between South Meadows and central Reno. Before remediation, project folders lived on an aging server with inconsistent permissions, remote users depended on a brittle VPN, and backup reporting looked healthy even though no recent full restore had been tested. During a hardware fault combined with suspicious login activity, staff lost access to current files and had to fall back to emailed copies and local desktop versions.
After cleanup, the environment was rebuilt around supported storage, hardened identity controls, tested backup recovery, and clearer operational ownership. That reduced confusion during outages and gave managers a defined recovery sequence instead of improvised troubleshooting. In a region where crews may move between office, warehouse, and jobsite in the same day, that consistency matters more than feature count.
- Result: Recovery testing dropped estimated file-restore time from more than 8 hours to under 90 minutes, and project document access stabilized enough to avoid repeat billing delays during the next quarter.
Construction IT Risk and Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Backup Solutions and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno and South Meadows
Our office is positioned to support businesses across Reno, including South Meadows, where construction firms often balance office coordination, field access, vendor communication, and document-heavy workflows. That local proximity matters when a breach, failed restore, or aging infrastructure issue affects active jobs. We can assess the environment, review recovery exposure, and help map out a more stable modernization path without overcomplicating the stack.
Modernization Has to Reduce Risk, Not Add More Complexity
When a South Meadows construction firm hits the innovation wall, the visible problem may be a breach, an outage, or a failed restore. The underlying issue is usually older infrastructure that cannot support current security controls, dependable recovery, or the way teams now work across office, field, and cloud platforms.
The practical answer is to simplify the stack, retire weak points, and validate recovery before the next incident forces the issue. That approach protects project flow, billing continuity, and day-to-day operations far better than adding more tools onto unstable systems.

