What should Reno businesses look for in a managed IT services provider?
Reno businesses choosing a managed IT services provider should look past sales language and evaluate response discipline, security operations, documentation, recovery readiness, and local support capability, because those factors usually determine whether technology stays stable during real disruptions.
Aubree N. spent a Tuesday morning explaining to clients why her staff could not access email or the tax application after an outside provider left remote access exposed and never reviewed failed admin logins. Payroll was delayed, eight employees sat idle, and the combined recovery, legal, and productivity hit reached $77,000.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps Reno and Sparks businesses manage infrastructure, secure user access, maintain recoverable systems, and reduce disruption when systems fail or accounts are compromised. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to how a business should evaluate a managed IT provider, because competent technology management is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, compliance-aware operations, and operational resilience rather than broad promises.
This article explains how to evaluate a provider from an operational and risk perspective. This is general technical information; specific network environments and compliance obligations change strategy. A medical office, warehouse, law firm, and multi-location retailer will not need the same controls or review cadence.
A managed IT provider should do far more than answer support tickets. A mature managed IT services relationship assigns ongoing ownership for endpoint health, account changes, patching, vendor coordination, backup oversight, documentation, and escalation when something starts failing before users fully feel the impact. What usually separates a stable environment from a fragile one is whether someone is accountable for recurring operational tasks every week, not just during visible outages.
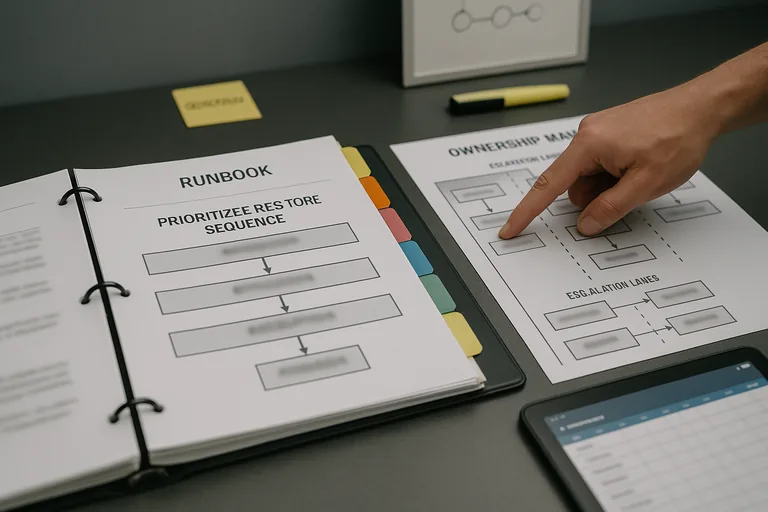
- Ownership: The business should know who watches systems after hours, who approves changes, who contacts vendors, and who leads communication during an outage.
- Visibility: A competent provider maintains an accurate asset inventory, flags unsupported systems, tracks warranty and licensing exposure, and knows which devices actually matter to operations.
- Recovery: The provider should be able to explain what is backed up, what is not, which applications must be restored first, and how long a realistic recovery sequence may take.
For Reno companies with physical offices, warehouses, or clinics, local presence still matters when firewalls fail, internet circuits need hands-on testing, or users are blocked by workstation, cabling, or printer issues. Businesses comparing agreements should understand how remote coverage connects to on-site technology needs and whether the provider can translate strategy into day-to-day operational support without leaving gaps between vendors.
What does a managed IT services provider actually manage beyond the helpdesk?
A competent provider manages the operating condition of the environment, not just the queue of incoming tickets. That usually includes endpoint deployment, account provisioning and removal, patch approval and enforcement, vendor coordination, documentation of critical systems, monitoring of servers and network equipment, and an escalation path for security events or service degradation. In mature environments, the provider also knows which business processes depend on which systems, so a failed switch at a front desk is treated differently than latency on a file server that supports accounting, production, or patient flow. A common failure point is when the provider only reacts to user complaints while no one owns background maintenance, lifecycle planning, or exception tracking.
Why does provider quality affect uptime, security, and liability so directly?
What should Reno businesses ask to judge whether support is truly proactive?
How should monitoring, patching, and escalation work in practice?
In practice, the issue is rarely the tool alone; it is the process around it. Monitoring should generate alerts tied to named devices and services, route them to a documented escalation workflow, create time-stamped tickets, and lead to either remediation or an approved exception with follow-up. During a routine infrastructure review, an experienced team may notice repeated disk latency alerts on a virtual host even though users have not yet opened tickets; that signal often leads to checking storage errors, backup overlap, replication lag, and whether a critical line-of-business server shares the same stressed datastore. The operational lesson is that competent providers do not just clear alarms; they investigate root cause, document changes, and reduce the chance that a minor performance issue becomes a midday outage.
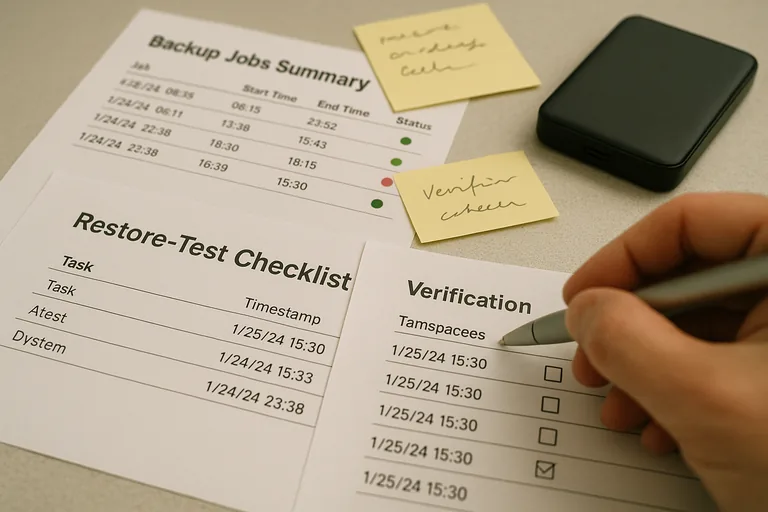
How can a business verify that security and recovery controls are really working?
Verification is where many weak environments break down. Businesses should expect observable evidence such as access review logs, multifactor enforcement records, patch compliance summaries, backup restore test results, endpoint policy status, and incident timelines showing when alerts were received, triaged, escalated, and closed. Guidance in NIST SP 800-63B matters here because authentication is not just about turning on MFA; it is about identity lifecycle discipline, which means accounts are approved, changed, disabled, and reviewed consistently so stale access does not remain active after role changes or departures. Without verification, businesses often discover that a backup job reported success while one application database was excluded, or that MFA existed for email but not for VPN, remote admin, or shared cloud applications.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when important controls exist on paper but nobody proves they work under pressure. This tends to break down when documentation is outdated, admin rights accumulate over time, internet and cloud vendors are blaming each other during an outage, or the provider has no clear answer on who owns emergency decision-making after hours. Hidden fragility usually shows up in small signals first: recurring tickets from the same users, unmanaged devices that never appear in reports, delayed offboarding, unsupported firewalls still in production, or security tools installed without someone reviewing detections every day. By the time leadership notices, the business is often already paying in lost labor, delayed billing, emergency consulting, or breach-response complexity.
What should happen before signing or renewing a managed IT agreement?
The business should review scope, exclusions, response expectations, reporting cadence, documentation ownership, offboarding procedures, and how security incidents are handled from first alert through recovery. A provider worth considering should be able to walk through a sample monthly report, explain how risk is communicated to leadership, identify what requires separate project work, and show how the environment would be handed over if the relationship ends. This is also the time to test whether the provider understands the business itself, because a law office, manufacturer, and nonprofit may all use Microsoft 365 but they do not share the same uptime priorities, access risks, or continuity needs. If those answers stay vague before the contract is signed, they usually become harder to get during a live incident.

