Strategic IT Leadership
Strategic IT leadership turns technology from a set of disconnected purchases into a managed business function by aligning systems, budgets, risk decisions, and recovery planning with how the organization actually operates each day.
During a Tuesday payroll close, Aitor U. found the accounting team locked out of the ERP after an overdue firewall replacement broke site-to-site access and nobody had mapped the dependency; four hours of downtime, emergency contractor fees, and missed payment windows turned a preventable planning failure into $57,000.
This situation reflects incident patterns observed across multiple business technology environments. Identifying details have been changed to protect confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, reduce security exposure, maintain recoverable systems, and improve continuity when operations depend on stable technology. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Strategic IT Leadership because practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience depend on disciplined ownership of systems, vendors, documentation, and decision-making across real business environments, including Reno and Sparks organizations that need stable and compliance-aware technology operations.
This article is intended to help decision-makers evaluate how technology leadership affects operational stability, security, and accountability. This is general technical information; specific network environments and compliance obligations change strategy. Formal planning should be based on actual systems, data flows, vendors, and recovery requirements.
Strategic IT Leadership is not just a senior title or a yearly budget meeting. It is the operational discipline of deciding who owns technology direction, lifecycle planning, risk tolerance, vendor accountability, recovery objectives, and the business consequences when those decisions are delayed. In mature environments, that role is often formalized through IT consulting and vCIO oversight so infrastructure choices support business operations instead of reacting to the next outage.
- Ownership: Someone must be accountable for standards, priorities, and escalation when technology decisions affect revenue, compliance, or downtime.
- Visibility: Leadership depends on current asset records, vendor inventories, dependency mapping, and reporting that shows what is actually deployed.
- Accountability: Decisions should produce evidence such as review notes, exception tracking, change records, and test results rather than informal assumptions.
What does strategic IT leadership actually cover?
It covers the business decisions behind the technology estate: hardware lifecycle, software standards, vendor contracts, identity and access policy, support model, cybersecurity priorities, continuity planning, documentation quality, and the order in which systems should be restored after an incident. What usually separates a stable environment from a fragile one is not the presence of tools alone, but whether someone is continuously aligning those tools with business deadlines, staff changes, risk appetite, and operational dependencies.
Why does it matter to daily operations and financial control?
When leadership is weak, the business often pays in irregular ways before it notices a major incident: rushed renewals, duplicate software spend, surprise compatibility problems, slow onboarding, unresolved recurring issues, and avoidable downtime during basic maintenance. In offices that handle regulated data or are reviewing HIPAA security expectations, poor leadership also shows up as undocumented exceptions, weak vendor oversight, and last-minute remediation work because compliance-related technology decisions were never assigned clear ownership.
What risks does it reduce before they become incidents?
It reduces the risks created by accumulated neglect: old accounts that still work, unsupported devices still on the network, single points of failure in line-of-business software, and infrastructure changes made without understanding business impact. Guidance in NIST SP 800-63B exists because identity systems fail when authentication and account lifecycle management are inconsistent; in business terms, that means access can outlive the employee, the vendor, or the business need. Strategic leadership turns those risks into reviewable controls by defining standards for onboarding, offboarding, privileged access, vendor access, and exception handling before a credential misuse or service interruption exposes the gap.
How does strategic IT leadership work in practice?
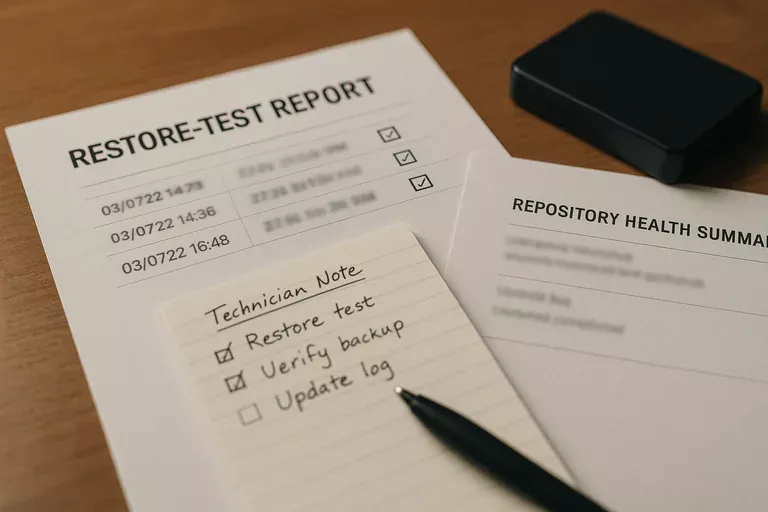
In practice, it runs as a cadence, not a one-time project: current asset inventory, contract and warranty review, patch exception review, privileged access checks, business application dependency mapping, recovery priority review, and scheduled decisions on replacement or remediation. During one routine review pattern, repeated lockouts on a departed manager’s mailbox led investigators to an old copier relay still using that former employee’s credentials. The visible symptom looked like an authentication nuisance, but the real issue was missing service account documentation and an incomplete offboarding process. Competent teams prevent this by linking account lifecycle, device records, vendor documentation, and change control so the same weakness does not reappear in a more damaging form.

How can a business verify that IT leadership is actually working?
When does weak implementation become dangerous?
It becomes dangerous when controls exist only as assumptions. A common failure point is monitoring tools generating alerts with no documented escalation owner, multifactor authentication enabled for some users but not all privileged accounts, or server replacement plans delayed until a dependency breaks during business hours. In environments that have not been reviewed recently, documentation is often outdated, inherited admin rights accumulate quietly, and vendor access survives long after the project ended. The business consequence is not abstract risk; it is slower incident response, wider security exposure, harder recovery, and leadership being forced to make expensive decisions under pressure.
What should leadership teams do next?
Start by identifying who owns technology direction and whether that person can show current evidence of control, not just intent. Review the asset list, account lifecycle process, renewal calendar, critical vendor dependencies, security exceptions, and the order in which core systems must be restored if a major issue occurs. If those records are incomplete, inconsistent, or spread across individuals, the next step is not buying more tools; it is establishing governance, review cadence, and accountability so decisions become deliberate instead of reactive.

