Professional Services
Professional services firms need IT and cybersecurity support that protects client data, preserves billable time, and keeps document, email, and practice systems reliable. The right structure reduces disruption, clarifies accountability, and supports steady operations.
At 8:12 a.m., Alexander M.‘s accounting firm lost access to a shared document workspace after a neglected Microsoft 365 admin account was used to alter permissions and remove retention controls. Four partners spent two days reconstructing client files and missed filing deadlines, turning a preventable support failure into $60,750 in write-downs, overtime, and recovery work.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.

Scott Morris is a managed IT and cybersecurity professional who helps businesses secure identities, stabilize infrastructure, maintain critical applications, document recovery procedures, and recover from preventable technology failures. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to professional services because these firms depend on client confidentiality, document availability, secure remote work, and predictable uptime; in real business environments, competent IT management reduces downtime, limits security exposure, supports business continuity, and improves operational resilience for Reno and Sparks organizations that cannot afford fragile systems.
Every firm has different applications, contractual obligations, data retention duties, and risk tolerance. This is general technical information; specific network environments and compliance obligations change strategy. Legal, financial, engineering, and clinical-adjacent practices may require additional review based on the systems and information they handle.
In IT terms, professional services support is the operating model behind firms that sell expertise, time, and trusted client relationships. It usually centers on identity management, secure email, document systems, line-of-business applications, workstation standards, vendor coordination, and clear response ownership so a missed filing, broken timesheet platform, or inaccessible client matter does not become a revenue problem.
What usually separates a stable firm from a fragile one is not the software brand but the discipline around it. Professional practices often depend on a small set of critical systems: Microsoft 365, document repositories, scanners, practice management, accounting, and remote access for partners and staff. When those systems are wrapped in structured managed IT services, firms tend to get consistent patching, helpdesk triage, device standards, and monitoring; when support is ad hoc, permissions sprawl, unsupported workstations linger, and busy-season outages become more likely.
Some firms also sit close to regulated data. An accounting office may hold tax identifiers, a law firm may retain litigation records, and a specialty practice may overlap with healthcare environments where privacy and availability requirements are higher. In those cases, a mature ongoing support model should include documented access reviews, retention settings, vendor risk discussions, and recovery priorities tied to billable operations rather than generic desktop support.
What does competent IT support for professional services actually include?
A competent model covers the full lifecycle of people, devices, data, and vendors. That means standardized workstation builds, enforced multifactor authentication, onboarding and offboarding tied to HR events, secure document sharing, patch windows that respect billing deadlines, support for scanners and line-of-business tools, and escalation rules for issues that interrupt client work. In mature environments, the service is designed around continuity of billable work, not just ticket closure.
Why do professional services firms become fragile when IT is handled informally?
A common failure point is ownership drift. One partner approves software, an office manager creates accounts, a copier vendor configures scan-to-email, and nobody maintains a current view of how access, retention, and backups intersect. In environments that have not been reviewed recently, former employees often still have delegated mailbox access, old laptops miss security updates, and shared folders carry years of inherited permissions. The operational consequence is not abstract risk; it is deadline pressure, client confidentiality exposure, and expensive reactive work when something breaks during a busy week.
Which risks should professional services support reduce?
The main risks are unauthorized access to client data, interruption of document or practice systems, loss of email history, billing disruption, and weak recovery capability after human error or vendor outages. Competent support reduces these by controlling who has access, hardening endpoints, monitoring core services, documenting critical dependencies, and prioritizing recovery for systems that affect client delivery. In practice, the issue is rarely the tool alone; it is the process around it, especially when security tools are installed but nobody reviews alerts or removes stale access.
How should professional services IT support work in practice?
In practice, the workflow starts with a reliable asset inventory, identity standards, and configuration baselines for laptops, Microsoft 365, and line-of-business applications. Alerts should route into a documented triage process, routine patching should have exception handling for specialty software, and onboarding or offboarding should trigger mailbox, file access, VPN, and mobile device changes in one controlled sequence. During a quarterly review, repeated sign-in attempts against a departed contractor account led to a deeper check and exposed an active mobile token plus lingering SharePoint permissions; the ticket to disable the account had been closed, but the identity lifecycle had not been fully completed. Guidance in NIST SP 800-63B matters here because strong authentication only reduces risk when account creation, changes, and deprovisioning are handled consistently across the full user lifecycle.
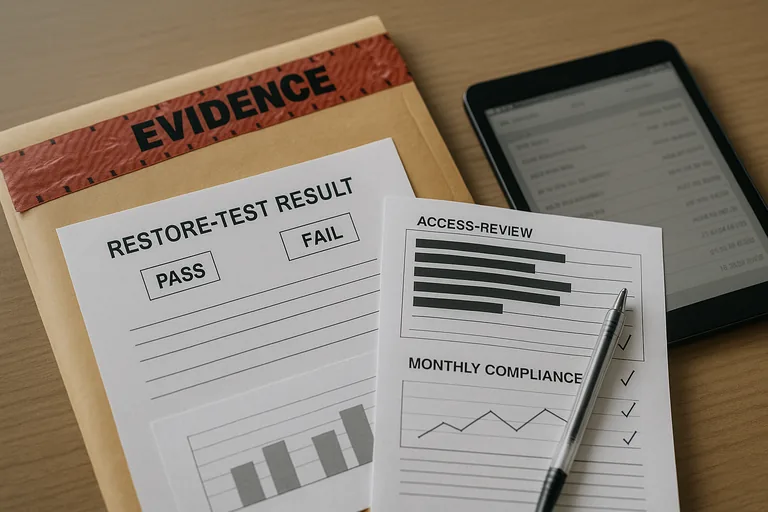
How can leadership verify that the service is real and not just promised?
A competent provider should be able to explain and show evidence. Useful proof includes a current asset inventory, monthly patch compliance reports, access review records for privileged and shared accounts, documented escalation timelines for major incidents, restore test results for critical data, and change records showing who approved material system changes. Without that evidence, firms often assume controls exist because the tools are licensed, when in reality alert queues may be ignored, exceptions may be undocumented, and recovery steps may still depend on tribal knowledge.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when convenience quietly overrides control. This tends to break down when a partner keeps local admin rights just in case, a legacy application server is excluded from updates because reboots are inconvenient, external sharing links remain open after projects close, or a document platform has no tested rollback plan before major configuration changes. These shortcuts can remain invisible for months, then surface as exposed client material, a failed integration during tax or audit season, or an outage that forces manual workarounds with little documentation to guide recovery.
What should leadership ask for before accepting or renewing professional services IT support?
- Critical systems map: Ask which applications, file stores, identity systems, and vendor dependencies would stop billable work within a few hours.
- Evidence package: Ask to see the latest patch report, access review, restore test result, and incident escalation record.
- Ownership model: Ask who approves access, who handles exceptions, who maintains documentation, and who coordinates with software vendors during an outage.
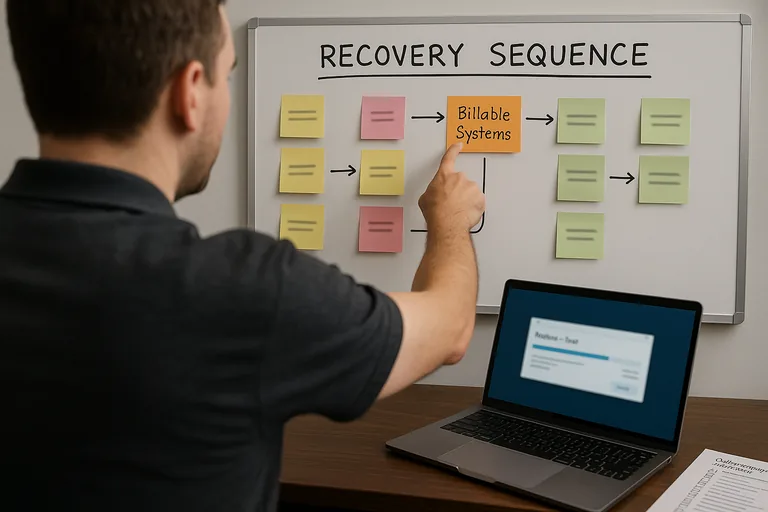
- Recovery priorities: Ask in what order systems are restored, what manual workarounds exist, and how staff are informed during disruption.

