Network, Server & Cloud Management in Sparks, Nevada
Network, server, and cloud management keeps Sparks businesses operating by making sure core systems are monitored, patched, documented, secured, and recoverable. Done well, it supports uptime, steadier performance, cleaner troubleshooting, and fewer expensive surprises during outages or cyber incidents.
At 8:17 a.m. on a Monday in Sparks, Alvin V. lost access to scheduling, file shares, and email because a neglected switch power fault had fragmented the office network and stalled cloud synchronization, triggering two days of disruption and $65,200 in overtime, delays, and lost billable work.
This story is based on a real business technology support pattern: the kind of operational breakdown that often becomes visible only after systems, staff, vendors, and workflows are already under strain. Names, dates, timelines, and identifying details have been anonymized or modified for confidentiality, while preserving the practical lessons behind the scenario.

Scott Morris is a managed IT and cybersecurity professional who helps businesses manage networks, servers, cloud platforms, user access, recovery readiness, and day-to-day operational risk in Reno and Sparks business environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is relevant to Network, Server & Cloud Management in Sparks, Nevada because stable infrastructure is rarely the result of one tool; experienced IT teams reduce downtime and security exposure through monitoring, documentation, patch discipline, access control, tested recovery procedures, and practical business continuity planning.
This article explains common operational patterns and evaluation criteria, not a diagnosis of any one company’s environment. This is general technical information; specific network environments and compliance obligations change strategy.
In Sparks, many companies operate hybrid environments with office internet circuits, on-premises line-of-business servers, remote users, Microsoft 365 or other cloud services, VPN access, and printers or wireless networks that still affect daily productivity. When those pieces are managed separately, problems hide in the gaps. That is why many organizations pair infrastructure oversight with broader managed IT services in Sparks so helpdesk patterns, monitoring, patching, and security events inform one another instead of living in separate silos.
The business question is not whether a workload is physical, virtual, or cloud-hosted. The real question is whether the environment is documented, recoverable, and securely administered when staff change, vendors make adjustments, or internet conditions degrade. A mature environment usually has current asset records, backup retention policies, access ownership, and review routines that tie infrastructure work back to compliance and risk management rather than treating security as a separate project.
What does network, server & cloud management actually include for a Sparks business?
For a Sparks business, the scope usually includes core switching, firewall and wireless administration, DNS and DHCP reliability, VPN and remote access, server operating systems, virtualization hosts, storage, backup job health, cloud tenant settings, identity administration, license ownership, and vendor coordination for business software. The work is continuous rather than one-time, because devices age, cloud settings drift, certificates expire, storage fills, and user access changes unless someone is reviewing the environment against a documented baseline.
Why does network, server & cloud management matter beyond uptime?
It matters because most business interruptions do not begin as dramatic outages; they begin as small unmanaged dependencies such as an expiring certificate, a full disk, a stale DNS record, a failed sync connector, or a firewall rule that no longer matches how an application now communicates. When the network, servers, and cloud tenant are managed together, these issues are usually detected earlier and resolved with less finger-pointing between vendors. For organizations handling personal information, Nevada Revised Statutes NRS 603A matters because reasonable security measures and breach notification duties can turn weak infrastructure hygiene into legal and reporting exposure, not just downtime.
What risks does competent network, server & cloud management reduce?
- Hidden single points of failure: One aging switch, internet circuit, storage volume, or domain controller without documented failover can stop work across multiple departments.
- Identity drift: Old accounts, broad admin rights, and inconsistent multifactor enforcement can let one compromised credential become a wider security incident.
- Change collisions: Cloud app updates, firewall edits, and server patches can break line-of-business traffic when dependencies were never mapped.
- Recovery confusion: Backups or snapshots may exist, but without tested restoration order and application checks, the business stays down longer than expected.
How does competent network, server & cloud management work in practice?
In mature environments, monitoring is layered: network devices report interface errors, temperature, power status, and link changes; servers report patch levels, disk growth, service health, and failed logons; cloud platforms record sign-in anomalies, admin changes, mail flow problems, and storage alerts. A competent team reviews those signals against an asset inventory, applies updates in defined maintenance windows, tests whether business services came back cleanly, and records exceptions instead of assuming a change was harmless. During one routine review, repeated interface drops on an uplink matched complaints that a hosted accounting application froze every afternoon; investigation showed a firewall change had forced traffic through an undersized VPN path after a cloud migration, and the permanent fix was a documented rollback, capacity adjustment, and change review step. Guidance from NIST SP 800-207 Zero Trust Architecture matters here because cloud-connected businesses can no longer treat the office network as automatically safe; segmentation and verified access reduce how far a mistake or compromise can spread.

What evidence shows network, server & cloud management is being handled competently?
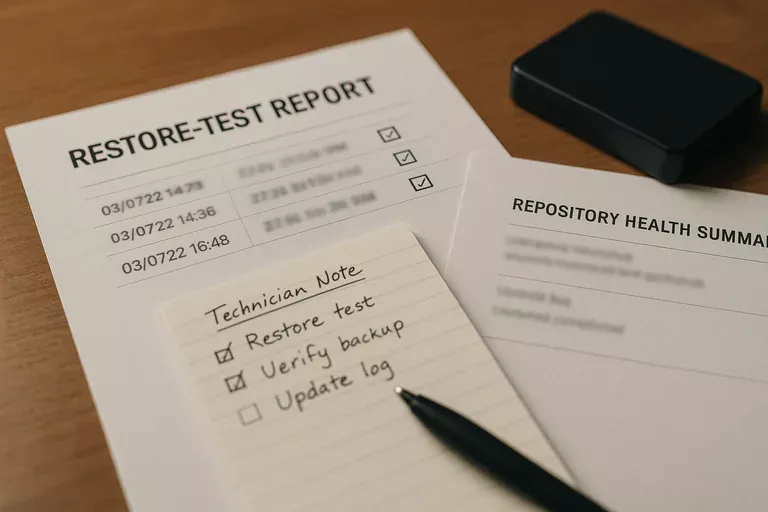
Real evidence looks like current network diagrams, asset inventories, patch compliance reports, alert escalation logs showing who responded and when, monthly review notes, backup restore test records, and access review reports for privileged accounts. A common failure point is a monitoring tool that generates alerts while nobody can produce the last incident timeline, the unresolved exception list, or proof that critical systems were reviewed after patching. In practice, organizations evaluating local managed IT operations should ask to see recent samples of this evidence with sensitive details redacted, because mature environments leave an audit trail of what was checked, what failed, and what was done next.
When does weak network, server & cloud management become dangerous?
This tends to break down when the business has grown faster than its documentation and access controls. Server patches may be applied while firmware is ignored, cloud multifactor authentication may be enabled for employees while shared admin accounts or vendor accounts remain outside policy, and systems may appear healthy because nobody verifies alert thresholds or escalation ownership. Guidance from NIST SP 800-63B is useful because it treats authentication as an identity lifecycle problem rather than a login checkbox. In practice, partial enforcement gives leadership a false sense of safety while an attacker or internal mistake only needs the one unmanaged account or forgotten service dependency that was never reviewed.
What should a Sparks business evaluate next?
Start with a few concrete questions: Is there a current asset list and network diagram, with a named owner for every critical system? Can someone show recent patch compliance, unresolved exceptions, and the last successful restore test of a business-critical application rather than just a backup summary? How are admin accounts reviewed, removed, and logged when employees or vendors change? If the internet circuit, firewall, or cloud identity service fails at 10 a.m., who follows the documented response and how is the business kept operating? Those answers reveal whether the environment is being managed as a business system or as a collection of unattended tools.

