Network, Server & Cloud Management in Fernley, Nevada
Network, server, and cloud management keeps Fernley businesses operational by controlling performance, access, updates, and recovery with local accountability. When these systems are maintained well, companies usually see fewer outages, better security visibility, and less preventable disruption.
At a Fernley distribution office, Ana G. watched order processing stop when an overfilled virtual server datastore froze the ERP system and cloud file sync began pushing stale inventory data to staff. By the time invoicing, shipping, and after-hours recovery work were untangled, the interruption had cost $67,100.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
This article is intended to help business leaders understand how infrastructure management decisions affect uptime, security, and recovery planning. This is general technical information; specific network environments and compliance obligations change strategy.
Network, server, and cloud management is the ongoing control of how traffic moves, where business systems run, who can access them, how updates are applied, and how failures are contained. In a Fernley business, that usually means firewalls, switching, Wi-Fi, VPN, virtual hosts, storage, Windows or Linux servers, Microsoft 365 or Azure services, and the identity systems connecting them.
A common failure point is split ownership. The firewall may be supported by one vendor, the server by another, Microsoft 365 by nobody in particular, and the documentation by nobody at all. This tends to break down when a password reset fails, a circuit flaps, DNS stops resolving, or a line-of-business application slows down and no one can tell whether the root cause lives on the network, the server, or the cloud side.
What usually separates a stable environment from a fragile one is operational discipline: accurate asset inventory, current network diagrams, patch and reboot windows, admin role reviews, configuration baselines, and evidence that alerts are acknowledged and closed. Businesses comparing this work to broader managed IT services in Fernley should look for named ownership and documented follow-through rather than a vague promise to watch the systems.
What does network, server & cloud management actually include?
It includes lifecycle oversight for the systems that keep users connected and applications available. On the network side, that means firewalls, switches, wireless, VPN, DNS, DHCP, internet failover, and segmentation. On the server side, it includes operating systems, virtualization hosts, storage, patching, capacity, backups, and application dependencies. On the cloud side, it covers Microsoft 365 or other SaaS platforms, identity, permissions, email flow, device enrollment, and admin controls. In practice, the issue is rarely the tool alone; it is the process around it, including ownership, documentation, change control, and recovery planning.
Why does this matter for daily operations in Fernley businesses?
Most infrastructure failures appear first as business delay, not as a technical alert. If DHCP scopes fill up, scanners and phones drop. If DNS or WAN failover is unstable, cloud applications time out and users get blamed for being unable to log in. If domain policies drift, printers, mapped drives, and line-of-business software behave inconsistently across departments. For Nevada organizations that store employee or customer information, Nevada Revised Statutes NRS 603A matters because it requires reasonable security measures, which means weak infrastructure management can create both downtime and legal exposure when personal information is involved.
Which risks does competent management reduce before they become outages or security events?
Competent management reduces risk by closing the small gaps that outages and attackers usually exploit first. Unreviewed admin accounts, unpatched switch firmware, flat networks, expired certificates, and cloud apps with excessive permissions create different symptoms but the same underlying problem: nobody is managing the environment as one system. Guidance in NIST SP 800-63B is useful here because strong authentication only helps when identity is managed throughout the account lifecycle; in practice, that means enforcing multifactor authentication, removing stale access, and tracking privileged changes. This is also where infrastructure oversight overlaps with compliance and risk management, because controls that protect uptime often also support audit readiness and reduce breach exposure.
How does this work in practice inside a real business environment?
In mature environments, management runs as a repeatable workflow: devices and servers are inventoried, monitoring thresholds are tuned, logs from firewalls and servers are reviewed, patch windows are scheduled, cloud admin roles are limited, and every material change leaves a record. During a routine infrastructure review, a storage-latency alert on a virtual host initially looked like an internet complaint from users. Correlating the alert with change records showed that an old snapshot chain from a failed maintenance window had never been removed, so disk growth was choking write performance on the ERP server. The fix was not just deleting files; it required snapshot aging rules, post-change validation, and confirmation that alerts route to someone who can investigate the underlying cause instead of only rebooting the server.
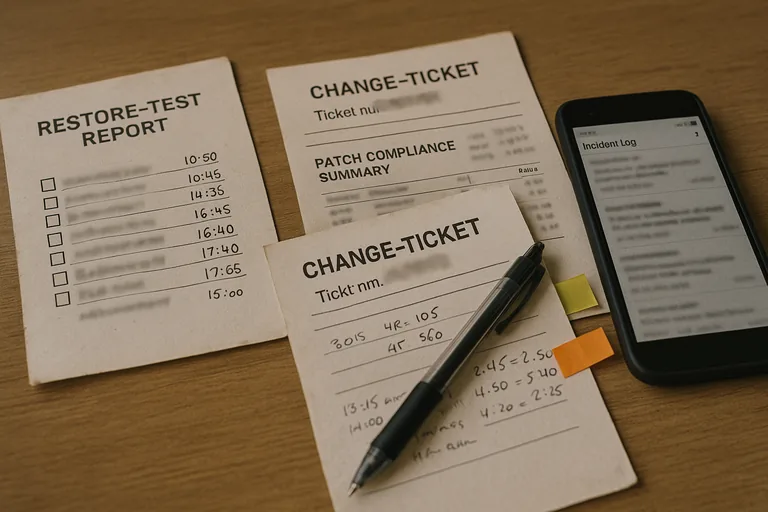
What evidence shows the environment is actually being monitored and maintained?
A mature environment produces visible evidence: current asset inventory, patch compliance reports, firewall configuration backups, change tickets, alert escalation logs, access review records, and periodic restore or failover test results. A monitoring system should generate alerts, but competent teams also maintain documented escalation workflows showing who responded, what was investigated, and whether the issue was fully resolved. Without these artifacts, many businesses are relying on memory and vendor reassurance. One of the first things experienced IT teams check is whether the documentation matches reality, because stale records during an outage usually lengthen recovery far more than the original fault.
What warning signs suggest weak or dangerous implementation?
Weak implementation becomes dangerous when controls exist on paper but not in enforcement. Common signs include shared admin accounts, firewall rules nobody can explain, switch stacks still running years-old firmware, cloud tenants with personal email addresses set as recovery contacts, antivirus deployed without any response workflow, and monitoring alerts routed to mailboxes that no one actively watches. This tends to break down during staff turnover, internet outages, or vendor changes, because undocumented exceptions and accumulated permissions surface all at once. What looks inexpensive month to month can become very expensive when a preventable outage turns into lost billing, delayed shipping, or an incident that cannot be scoped cleanly.
What should a Fernley business do next if its environment feels fragile?
If an environment feels fragile, the next step is a structured review rather than a rushed platform change. A business leader should be able to ask for a current network diagram, the last patch compliance report, the last restore or failover test, a list of privileged accounts, and an explanation of who owns alert triage after hours. If that evidence is missing, compare the situation against broader service expectations for Fernley businesses and the organization’s own risk and compliance responsibilities. The point is to determine whether the environment is documented, supportable, and recoverable before the next incident answers that question at a higher cost.

