Network, Server & Cloud Management in Carson City, Nevada
Reliable network, server, and cloud management keeps Carson City businesses reachable, secure, and recoverable when systems fail. The real value is not hardware alone; it is disciplined monitoring, maintenance, documentation, and response that keep operations moving.
At 8:17 a.m., Amber J. lost her ERP, shared files, and Microsoft 365 access because an unmonitored core switch failed and the server environment had no tested failover path. Order processing stopped, staff went idle, and the disruption was later estimated at $65,900.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
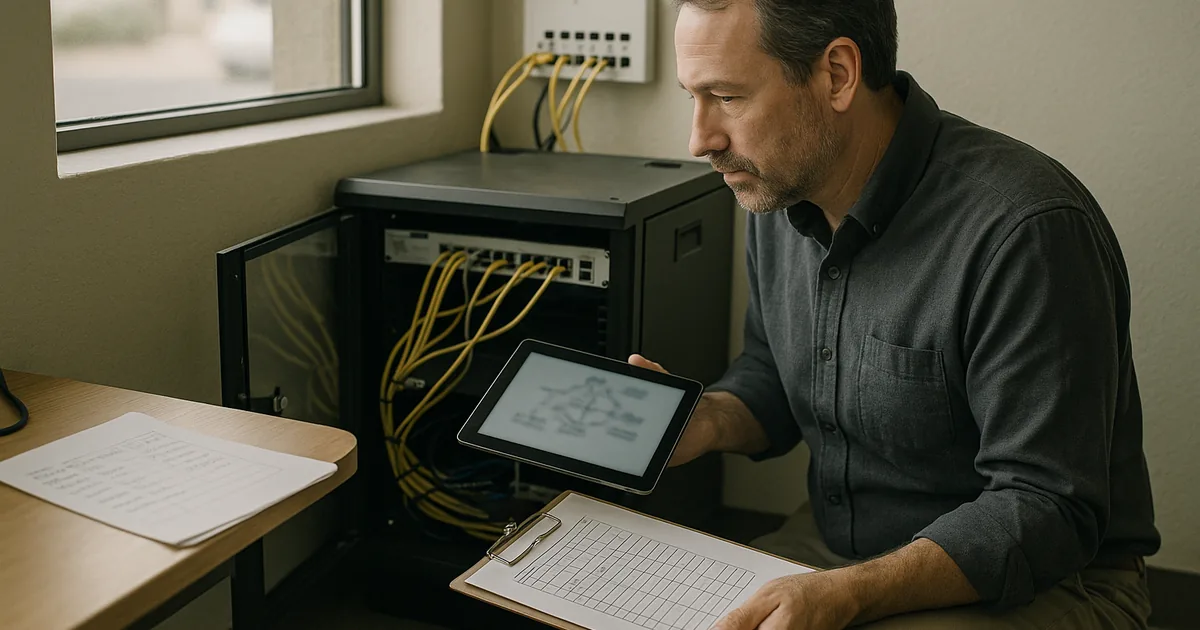
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage networks, servers, cloud platforms, identity controls, recovery planning, and day-to-day infrastructure stability. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Network, Server & Cloud Management in Carson City, Nevada because weak monitoring, undocumented changes, poor ownership, and inconsistent security controls routinely turn ordinary faults into downtime, security exposure, and difficult recovery; experienced IT teams reduce risk through proactive support, defense in depth, business continuity planning, secure infrastructure management, recovery readiness, and operational resilience for business technology environments, including those in Reno and Sparks.
The guidance below is intended to help business leaders evaluate operational risk, documentation quality, and recovery readiness in real environments. This is general technical information; specific network environments and compliance obligations change strategy.
Network, server, and cloud management is the coordinated operation of office switching, firewalls, wireless, internet circuits, virtualization hosts, business servers, Microsoft 365, cloud storage, identity systems, and vendor dependencies. In practice, it overlaps with managed IT services in Carson City because the business question is whether the whole environment remains available, secure, and supportable when staff, software, locations, or internet conditions change.
A common failure point is treating each layer as someone else’s responsibility. The firewall may be maintained, but nobody owns switch firmware; Microsoft 365 may have licenses assigned, but nobody reviews administrative roles; a server may be backed up, but nobody checks whether the line-of-business application will reconnect cleanly after recovery. Mature environments track assets, configurations, alert routing, patch cadence, and documented exceptions, which is why infrastructure oversight often intersects with compliance and risk management rather than sitting in a separate silo.
What does network, server and cloud management actually include for a Carson City business?
It includes more than internet service and a few office PCs. In a real business environment, the scope usually covers switching, firewall policy, Wi-Fi reliability, VPN access, DNS and DHCP, virtualization hosts, domain services, file and application servers, cloud email, SaaS integrations, storage capacity, certificate renewals, user identity lifecycle, and vendor escalation. One of the first things experienced IT teams check is ownership: who approves changes, who receives alerts after hours, and who can restore service if the primary administrator is unavailable. If those answers are unclear, the environment is already more fragile than it appears.
Why does coordinated management matter more than buying decent hardware?
What usually separates a stable environment from a fragile one is coordination across dependencies. A server reboot may look routine until it breaks mapped drives, interrupts a site-to-site VPN, or prevents a cloud application from syncing with on-premises identity. That is why mature managed IT operations rely on shared monitoring, documented maintenance windows, and clear escalation instead of assuming each system can be maintained in isolation. In practice, the issue is rarely the tool alone; it is the process around it, especially when multiple vendors touch the same environment.
Which operational risks does competent management reduce?
Competent management reduces quiet risks that often stay hidden until a busy day exposes them: patch gaps on internet-facing systems, expired certificates that break secure connections, overfilled storage that freezes virtual machines, stale VPN accounts, excessive admin rights in cloud platforms, misrouted traffic after ISP changes, and undocumented firewall rules that allow more access than leadership realizes. For Carson City businesses handling personal information, Nevada Revised Statutes NRS 603A matters because the law expects reasonable security measures and creates breach notification obligations when protected data is exposed. In business terms, weak infrastructure management can become downtime, data exposure, legal scrutiny, and higher recovery cost at the same time.
How does it work in practice across network, server and cloud systems?
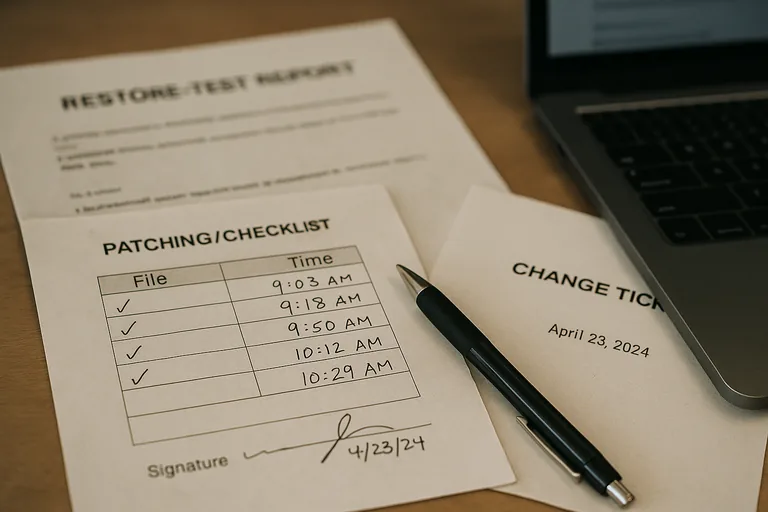
In mature environments, the work runs on a repeatable cadence: health monitoring on firewalls, switches, hosts, disks, and cloud services; patch deployment with rollback planning; configuration backups; account lifecycle review; certificate renewal tracking; and alert triage with named ownership. Guidance in NIST SP 800-207 Zero Trust Architecture matters here because remote users and cloud apps should be continuously verified, not trusted simply because they are on the office network; that reduces lateral movement after a compromised account or device. During a routine infrastructure review, a packet-loss alert on an accounting server led to discovery of an unmanaged switch hidden under a desk feeding phones, printers, and a cloud-connected inventory workstation. The symptom looked like an internet problem, but the real issue was undocumented network growth outside standard controls, and the lasting fix was updated network maps, port labeling, removal of shadow hardware, and change records that made later troubleshooting faster and safer.

How can a business evaluate whether the environment is being managed competently?
A competent provider should be able to show current network and cloud diagrams, an accurate asset inventory, patch compliance reports, alert escalation records, privileged access review logs, recent change tickets, and a clear list of systems that fall outside standard policy. If reporting stops at “everything is monitored,” that is weak evidence. In environments with real accountability, leadership can trace how incidents are handled, who approved major changes, how exceptions are documented, and whether those exceptions are being reduced over time through broader risk and compliance review. Observable records matter because they prove that the controls are operating, not merely promised.
When does weak implementation become dangerous?
What should happen next if your environment feels fragile?
Start with a current inventory of network devices, servers, cloud services, administrative accounts, and outside vendors with access to the environment. Then identify single points of failure, undocumented changes, systems outside patch policy, and applications that would materially interrupt revenue or service if unavailable for several hours. A practical next step is a short remediation plan with owners, deadlines, validation tasks, and a review cadence so improvements can be measured through evidence instead of assumed through habit.

