Managed IT Services in Sparks, Nevada
Managed IT services in Sparks, Nevada give businesses ongoing support, monitoring, security oversight, and infrastructure management so problems are found earlier, systems stay usable, and leaders get clearer control over downtime risk, vendor issues, and recovery readiness.
On a Thursday payroll cutoff, Alma G.‘s Sparks distribution office lost access to inventory and accounting after an unmanaged hypervisor filled with stale snapshots and forced key virtual servers into read-only failure; six hours of halted shipping, emergency labor, and recovery work drove a $64,400 hit. It is the kind of preventable breakdown weak managed IT services in Sparks, Nevada often leave undiscovered until operations are already bleeding time and cash.
The following situation represents a realistic incident pattern derived from real business IT environments. Identifying details have been changed to preserve confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure user access, maintain documentation, recover from outages, and improve continuity planning in operating environments where uptime and accountability matter. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Managed IT Services in Sparks, Nevada because stable operations depend on disciplined monitoring, secure infrastructure management, recovery readiness, practical risk reduction, and operational resilience rather than reactive ticket closure alone; Scott Morris supports Reno and Sparks business technology environments with a restrained, continuity-focused approach to managed IT and cybersecurity.
The guidance below is intended to help business owners and managers evaluate operational risk, service quality, and resilience in everyday IT environments. This is general technical information; specific network environments and compliance obligations change strategy.
Managed IT services are not just helpdesk coverage. In practice, they combine device management, patching, security oversight, account administration, vendor coordination, and documented support processes so a business is not depending on memory and break-fix habits. A common failure point is assuming managed IT services means someone will answer the phone; mature service also means someone is watching system health, ownership, warranty status, login risk, and change impact before an outage spreads.
For Sparks organizations with small internal teams, multiple sites, remote staff, or specialized line-of-business software, the operational value is consistency. When onboarding, offboarding, firewall changes, Microsoft 365 administration, and escalation paths are handled informally, risk accumulates quietly. Businesses comparing standard IT support with managed cybersecurity services in Sparks should understand that security tools only matter if alerts are reviewed, access rights are controlled, and someone owns the response workflow when something abnormal appears.
- Asset visibility: A competent provider maintains an accurate inventory of workstations, servers, network gear, cloud services, and supported software so unknown systems do not sit outside patching or monitoring.
- Operational ownership: Support requests, recurring maintenance, vendor issues, and after-hours escalation should follow documented workflows rather than informal habits tied to one staff member’s memory.
- Recovery capability: The environment should have documented backup scope, restoration priorities, and system dependency notes so the business can recover in a usable order instead of restoring systems blindly.
What are managed IT services in Sparks, Nevada?
Managed IT services in Sparks, Nevada are ongoing operational services used to keep business technology stable, supported, and accountable over time. That usually includes endpoint management, server administration, user provisioning, network oversight, patching, vendor coordination, and support triage. What usually separates a stable environment from a fragile one is not the ticket system or the logo on the invoice; it is whether someone is actively maintaining standards, reviewing risk, documenting changes, and preventing small faults from becoming business outages.
Why do managed IT services matter to daily operations in Sparks businesses?
They matter because most business disruption starts as a small unmanaged condition: a dormant account left enabled, a failed update on one server, an expired certificate, a storage threshold ignored, or a copier scan workflow that stops after a password change. In real business environments, those issues affect payroll, dispatch, scheduling, point-of-sale activity, quoting, and customer response times long before anyone calls it a cybersecurity incident. For Nevada companies handling personal information, Nevada Revised Statutes NRS 603A matters because it requires reasonable security measures; in practical terms, managed IT is where those reasonable measures become visible through access control, system maintenance, and incident handling rather than policy language alone.
Which risks do competent managed IT services actually reduce?
- Credential misuse: When user accounts are created, changed, and removed without discipline, former staff access and weak administrator practices can remain active far longer than leadership expects.
- Patch exposure: A common failure point is assuming updates are automatic everywhere when laptops, servers, and remote devices often fall out of policy if nobody verifies compliance.
- Unmanaged change: Firewall edits, vendor software updates, and cloud permission changes can interrupt production if nobody tracks what changed and why.
- Single-person dependency: Environments become fragile when passwords, vendor contacts, licensing knowledge, and recovery steps live in one employee’s inbox or memory.
How do managed IT services work in practice inside a business environment?
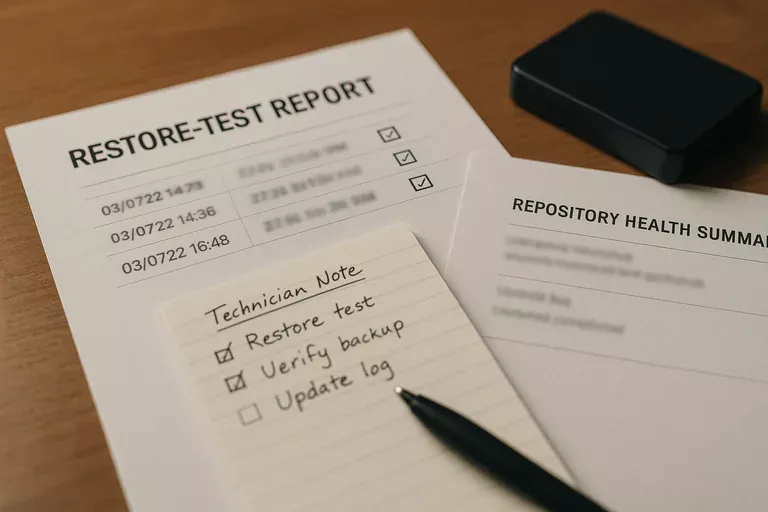
In mature environments, daily operations start with an accurate asset inventory, a defined monitoring scope, and clear ownership for alerts, exceptions, and escalation. Systems send health, patch, storage, and security events into monitored platforms; alerts are triaged, documented, and either resolved, escalated, or formally accepted as exceptions with business signoff. User access is managed as a lifecycle process, which is why guidance such as NIST SP 800-63B matters: identity protection is not just a password rule, but consistent enrollment, multifactor enforcement, account review, and prompt offboarding to reduce unauthorized access. During a routine capacity review in one inherited environment, repeated disk latency alerts on a virtual host led to the discovery that old application snapshots were never pruned after an upgrade. The platform looked available in casual status checks, but accounting performance was already degrading. This is where ongoing IT operations management earns its value: competent teams investigate the signal, document the root cause, correct the process, and confirm the alert thresholds and review cadence were adequate.

How can a Sparks business tell whether managed IT management is being executed competently?
- Ask for evidence, not assurances: A mature provider should be able to show patch compliance reports, managed asset counts, endpoint policy status, and recent ticket or alert trends.
- Review identity controls: There should be documented onboarding and offboarding steps, privileged account restrictions, multifactor coverage, and records showing periodic access review.
- Check monitoring accountability: A monitoring dashboard alone is not enough; there should be escalation logs showing who responded, what was investigated, and how recurring issues were corrected.
- Verify recovery readiness: Ask for restoration test records, dependency notes, and the order in which major systems would be brought back if the office lost a server or cloud access.
When does weak implementation become dangerous?
This tends to break down when tools exist without ownership. A business may have endpoint protection installed, but half the laptops are not checking in; backups may run, but no one has tested whether the finance database restores cleanly; multifactor authentication may be enabled for some users, while shared admin accounts remain outside policy. During incident response, it is common to discover that the environment looked healthy in monthly summaries because exceptions were never tracked and stale devices were still counted as protected. Weak implementation becomes dangerous when leadership is given a green status without underlying proof, because the first real audit of those assumptions often happens during an outage, a breach investigation, or a legal notification deadline.
What should a business in Sparks do next?
Start by asking for a current asset list, an access review, a patch compliance summary, a monitoring escalation path, and documented recovery priorities for the systems that actually run the business. If those items do not exist, or if they exist only as verbal assurances, the immediate issue is not the toolset but the absence of operational control. Businesses that already have internal IT should still compare their current process against managed cybersecurity oversight in Sparks and managed service discipline to identify blind spots before they turn into downtime, data exposure, or vendor-driven surprises.

