Managed IT Services in Reno, Nevada
Managed IT services in Reno, Nevada means more than outsourced support. Done properly, it gives local businesses accountable system oversight, faster issue response, stronger cybersecurity discipline, and documented recovery capability so routine problems do not become expensive operational interruptions.
Alicia B. thought her Reno distribution office had managed IT coverage until a failed domain controller patch left staff unable to log in on a Monday morning. Shipping labels stopped printing, invoices could not post, and after nine hours of downtime the disruption was calculated at $62,500.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.
This article explains how managed IT operations are evaluated in real business environments and where weak execution usually creates risk. This is general technical information; specific network environments and compliance obligations change strategy.
Managed IT services is the ongoing operational management of the systems a business depends on: workstations, servers, Microsoft 365 or Google Workspace, identity systems, network equipment, security tools, patching, vendor coordination, documentation, and user support. A common misunderstanding is treating managed IT services as a helpdesk subscription. In practice, competent management means someone owns system health before a user opens a ticket.
For Reno businesses, the issue is rarely one broken device. It is the accumulation of small failures across cloud apps, local networks, remote access, printers, vendor software, and user accounts. That is why mature environments connect IT operations with security disciplines such as access control, endpoint protection, and incident handling instead of separating support from risk management. Many organizations eventually realize they need both operational oversight and managed cybersecurity services in Reno because the same weak processes that cause downtime often create breach exposure.
- Operational ownership: Someone is responsible for alerts, patch status, hardware lifecycle, and vendor escalation before systems become unstable.
- Security discipline: Accounts, devices, and remote access are reviewed, hardened, and monitored instead of being trusted by default.
- Recovery readiness: Documentation, restoration procedures, and continuity planning exist so the business can keep functioning when a failure occurs.
What are managed IT services for a Reno business?
Managed IT services for a Reno business is an operating model in which a provider or internal team continuously maintains, monitors, documents, and supports business technology instead of waiting for failures to become emergencies. That includes user support, system updates, network oversight, cloud administration, endpoint protection, hardware replacement planning, vendor coordination, and escalation during incidents. What usually separates a stable environment from a fragile one is ownership. In weak environments, printers, servers, firewalls, and line-of-business software all technically work until no one knows who is reviewing logs, approving changes, or removing access for former staff. In mature environments, each system has a support path, a maintenance cadence, and a documented record of what changed, why it changed, and how it can be restored if something breaks.
Why does Managed IT Services in Reno, Nevada matter to day-to-day operations?
What risks do managed IT services reduce in real business environments?
Done competently, managed IT services may reduce unauthorized access, patch drift, unsupported software exposure, avoidable downtime, and recovery confusion during an incident. In practice, user identity is one of the most common weak points. Guidance from NIST SP 800-63B exists because authentication controls fail when account lifecycle management is inconsistent, multifactor authentication is applied unevenly, or privileged access is never reviewed; the business consequence is that a single compromised password can become lateral movement across email, file access, and finance systems. Nevada businesses also need to remember that Nevada Revised Statutes NRS 603A requires reasonable security measures for personal information, which turns sloppy account management and poor system oversight into a legal as well as operational problem. The control is not one tool; it is disciplined identity management, patch enforcement, logging, and review.
How does competent managed IT work day to day in practice?
Competent managed IT works through repeatable operational workflows: asset inventory stays current, endpoints report health status to monitoring tools, patches are approved and enforced on a schedule, security alerts are triaged by ownership rules, and ticketing data is tied to the actual device, user, and system involved. During a routine review, a series of overnight VPN authentication failures may look like user error at first. An experienced team checks the account, finds it belongs to a vendor who left months earlier, then discovers the account was excluded from multifactor enforcement and still had access to a sensitive subnet. The lesson is not that the alerting tool failed; it is that identity offboarding, exception review, and segmented access were never operationalized. In mature environments, the process around the tool is what prevents a small signal from becoming a larger incident.

How can a business verify that its managed IT provider is doing real work?
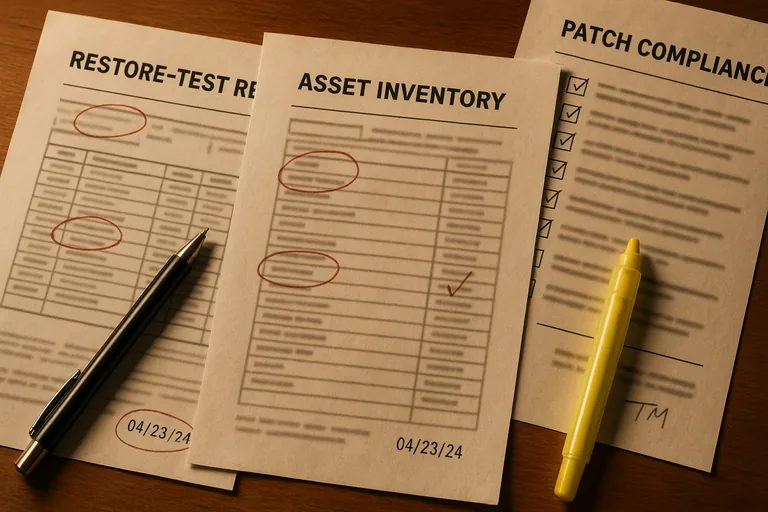
A business should ask for evidence, not reassurance. A mature environment should produce regular patch compliance reports, asset inventory records showing what is actually in scope, alert escalation logs showing what triggered review and how it was resolved, access review reports for privileged accounts, and change records for firewall, server, or cloud configuration updates. If backups or recovery processes are in scope, there should also be documented restore test results rather than a statement that jobs completed successfully. One of the clearest ways to judge ongoing managed IT oversight is to compare what the provider says is managed against what can be observed in reporting and documentation. If there is no inventory, no exception log, no review cadence, and no restoration evidence, the business is being asked to trust a process that has not been made visible.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when a control exists on paper but nobody verifies it under real conditions. A common failure point is monitoring that sends alerts to an inbox nobody reviews after hours, endpoint protection that is installed but never tuned for false positives or containment workflows, and administrator rights that accumulate because offboarding is handled informally. This tends to break down when a business relies on one aging server for authentication, printing, and a line-of-business application, yet there is no current diagram, no tested rollback plan, and no documented owner for maintenance windows. During incident response, it is common to discover that support looked responsive while core infrastructure had gone months without review. The operational consequence is longer downtime, slower containment, more finger-pointing between vendors, and higher cost to recover because nobody can quickly establish system state.
What should Reno decision-makers review before renewing or replacing managed IT services?
Decision-makers should review scope, evidence, dependencies, and accountability before they review price. Ask which systems are actually covered, who owns after-hours escalation, how identity changes are handled, what reports are delivered monthly, what exceptions remain unresolved, and how recovery steps are documented when a key server or cloud service fails. A competent provider should be able to explain where support ends and where security monitoring, vendor coordination, and continuity planning begin. The most useful comparison is not feature count; it is whether the environment shows disciplined ownership, current documentation, and a credible path to stable operations. If those answers are unclear, the business is not really evaluating service quality. It is inheriting hidden operational risk.

